Written by: Ali-Reza Adl-Tabatabai, Founder and CEO, Gitar
Key Takeaways
- Qodo PR-Agent uses a 4-level configuration hierarchy: Wiki (highest), repo-specific, global pr-agent-settings repo, and local env vars.
- Multi-repo setup requires creating a pr-agent-settings repo, adding .pr_agent.toml files, and merging to the default branch for activation.
- Key limitations include token limits that choke large files, performance degradation beyond 30 repos, and no automatic CI fixes.
- Pro and Enterprise tiers add merge commands and cross-repo context, but the OSS version lacks advanced multi-repo scaling.
- Teams that outgrow Qodo can switch to Gitar for no repository limits, zero-config setup, and automatic fixes that keep builds green across all codebases.
How Qodo PR-Agent’s Multi-Repo Config Hierarchy Works in 2026
Qodo’s configuration system follows a strict hierarchy where settings cascade from global to local levels. The precedence order controls which configuration wins when conflicts appear.
|
Config Level |
Location |
Precedence |
Use Case |
|
Wiki |
Repo wiki .pr_agent.toml |
Highest |
Org-wide overrides |
|
Repo |
Root .pr_agent.toml |
High |
Repo-specific settings |
|
Global |
pr-agent-settings repo |
Medium |
10+ repos default |
|
Local |
PR_AGENT_SETTINGS env var |
Lowest |
One-off overrides |
For GitHub organizations, create a repository named “pr-agent-settings” within your organization or project. This repository acts as the central configuration hub for all repositories under that scope. GitLab follows a similar pattern and supports nested subgroup configurations one level up.
Regardless of platform, the configuration hierarchy lets repository-specific needs override organizational defaults while keeping behavior consistent across your multi-repo setup. This structure suits organizations with standardized practices but grows complex when each repository has different requirements or risk profiles.
Step-by-Step Qodo Multi-Repo Setup for GitHub and GitLab
Multi-repo setup for Qodo PR-Agent demands careful alignment between the configuration hierarchy and each platform’s requirements. Small mistakes here often surface later as inconsistent behavior across repositories.
Step 1: Create a Global Configuration Repository
Create a repository named “pr-agent-settings” in your GitHub organization or GitLab group. Store the default configuration here so Qodo can apply it to every repository within that scope.
Step 2: Configure Base Settings
Add a .pr_agent.toml file to the root of your pr-agent-settings repository. Reference the sample configuration but avoid copying the entire file, since that introduces unnecessary defaults and noise. Focus on essential parameters that match your stack and scale, such as max_model_tokens=32000 for typical Python projects and enable_large_pr_handling=true for repositories with substantial codebases that might exceed token limits.
Step 3: Add Repository-Specific Overrides
For repositories that need custom behavior, add a .pr_agent.toml file to each repository’s root directory. These settings override the global configuration and give you fine-grained control over individual repository rules.
Step 4: Activate Configuration Across Repos
Merge all configuration changes into the default branch. Qodo PR-Agent reads configurations only from the default branch, so feature branch configuration files remain inactive until merged.
Python-heavy monorepos often require higher token limits and async processing, so teams typically adjust limits for large codebases and enable async_ai_calls=true. GitLab users should also configure webhooks that point to https://pro.gitlab.pr-agent.codium.ai/webhook and use their Qodo API key as the secret to ensure events reach Qodo reliably.
If this manual configuration process feels cumbersome, Gitar removes these setup steps entirely with zero-configuration multi-repo support that works across GitHub, GitLab, and all major CI platforms.
Top 7 Qodo PR-Agent Multi-Repo Limitations and Real-World Pitfalls
Qodo PR-Agent supports multi-repo configuration, yet large organizations quickly encounter scaling and reliability issues. These limitations become most visible once teams cross a few dozen active repositories.
|
Limitation |
Impact |
Example |
|
Token limits |
Chokes on large files or multi-repo context |
30+ repos degrade performance 50% |
|
Merge latency |
Reduces urgency in 50+ repo organizations |
Configuration propagation delays |
|
Fix application |
Relies on one-click apply in IDEs |
Manual steps for some remediations |
|
Pro-only advanced features |
OSS limited to single-repo patterns |
Enterprise scaling requires paid tiers |
|
GitHub-centric design |
Weaker GitLab integration |
Setup friction on non-GitHub platforms |
|
No CI integration |
Red builds persist after review |
Broken builds remain unfixed |
|
Performance degradation |
Issues appear around a few dozen repos |
Latency increases exponentially |
Qodo’s context engine provides cross-repo understanding, yet trade-offs appear at enterprise scale, especially for codebases with more than 400,000 files. The 142,606-character context limit forces manual context injection for cross-service dependencies, which creates friction for microservice architectures with 10 or more services.
Multi-repo indexing and specialist agent execution introduce significant compute and latency trade-offs. Organizations should run pilots to measure agent latency in their own environments, because performance varies sharply with repository size, retention windows, and concurrency.
Qodo PR-Agent Pro vs OSS for Multi-Repo Teams
The feature gap between Qodo’s open-source and commercial tiers shapes how far teams can push multi-repo deployments. Many organizations start on OSS, then hit scaling walls that require Pro or Enterprise features.
|
Feature |
OSS |
Pro/Enterprise |
|
Multi-repo context |
Basic PR diff analysis |
Advanced RAG with cross-repo dependencies |
|
Merge commands |
Limited /describe, /review |
Full /merge, /compliance commands |
|
Ignore patterns |
Repository-only configuration |
Global regex patterns across repos |
|
Context injection |
Manual via comments |
/include commands for dependencies |
Open-source configuration exposes many settings but still faces the context limits described earlier. Pro and Enterprise tiers add the Context Engine, which indexes dozens to thousands of repositories and maps dependencies for deeper review analysis, although token constraints can still appear at extreme scale.
The commercial tiers also provide repo tagging to group repositories under custom labels and Deep Research Agent capabilities for thorough multi-repo answers. Even with these upgrades, some architectural challenges remain for very large codebases, particularly around latency and operational overhead.
Why Gitar Solves Qodo’s Multi-Repo Scaling Gaps
Qodo PR-Agent struggles as repository counts and CI complexity grow, while Gitar delivers no repository limits and automatic fixes that keep pipelines green. The following comparison shows how Gitar addresses the critical limitations highlighted in the previous sections.
|
Feature |
Qodo PR-Agent |
Gitar |
|
Max Repositories |
Performance issues around a few dozen repos |
No repository limits on the Team Plan |
|
Auto-Fix CI/Reviews |
One-click apply in IDEs |
Yes, commits fixes and keeps builds green |
|
Multi-Repo Context |
Token-limited with manual injection |
Hierarchical memory system |
|
Setup Complexity |
Manual hierarchy configuration |
Roughly 30-second install |
|
Pricing Model |
Pro tier required for scaling |
14-day full Team trial |
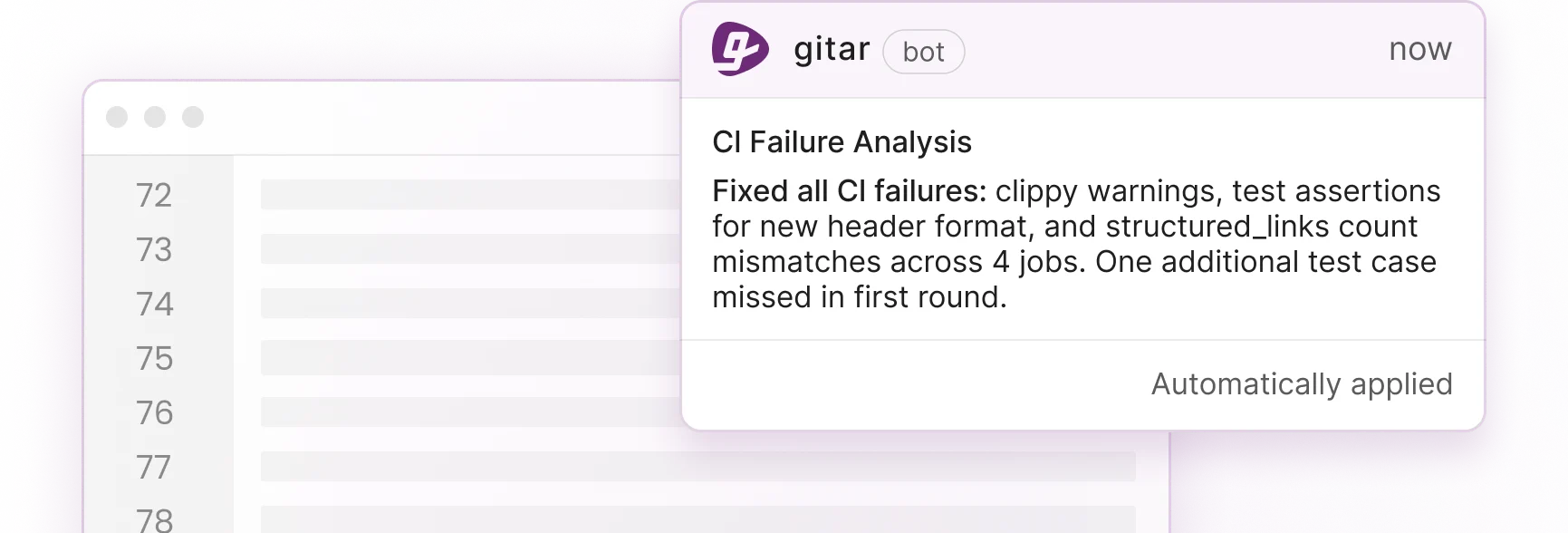
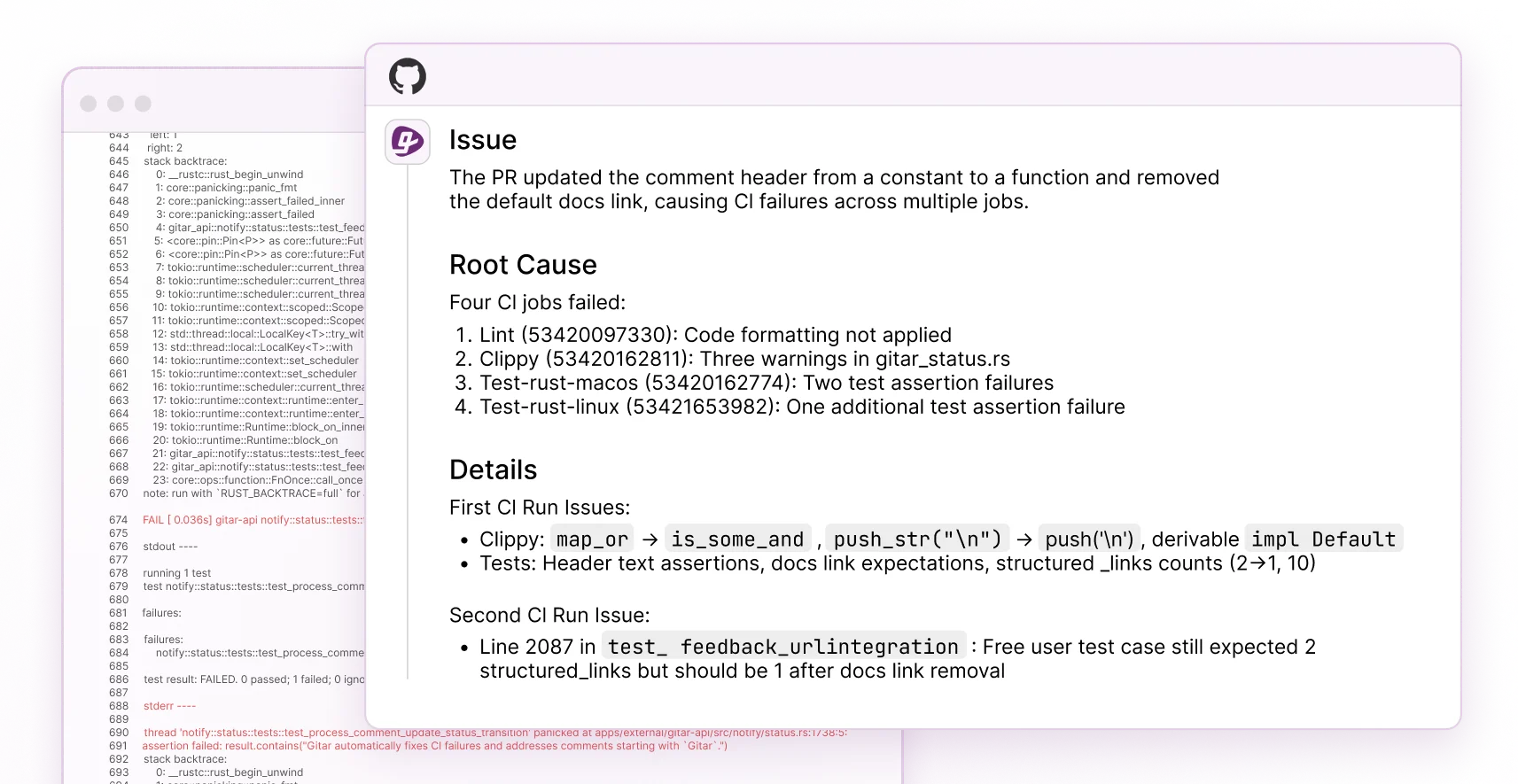
Gitar’s healing engine analyzes CI failures, generates validated fixes, and commits them directly to pull requests. This workflow removes the manual steps that slow many tools and keeps high-velocity teams moving. Gitar’s architecture comfortably handles 100 or more repositories, using hierarchical memory that learns team patterns over time.
The platform integrates natively with GitHub, GitLab, CircleCI, and Buildkite without complex configuration hierarchies. Teams report catching security vulnerabilities that Copilot missed and avoiding notification spam through Gitar’s single updating comment model.
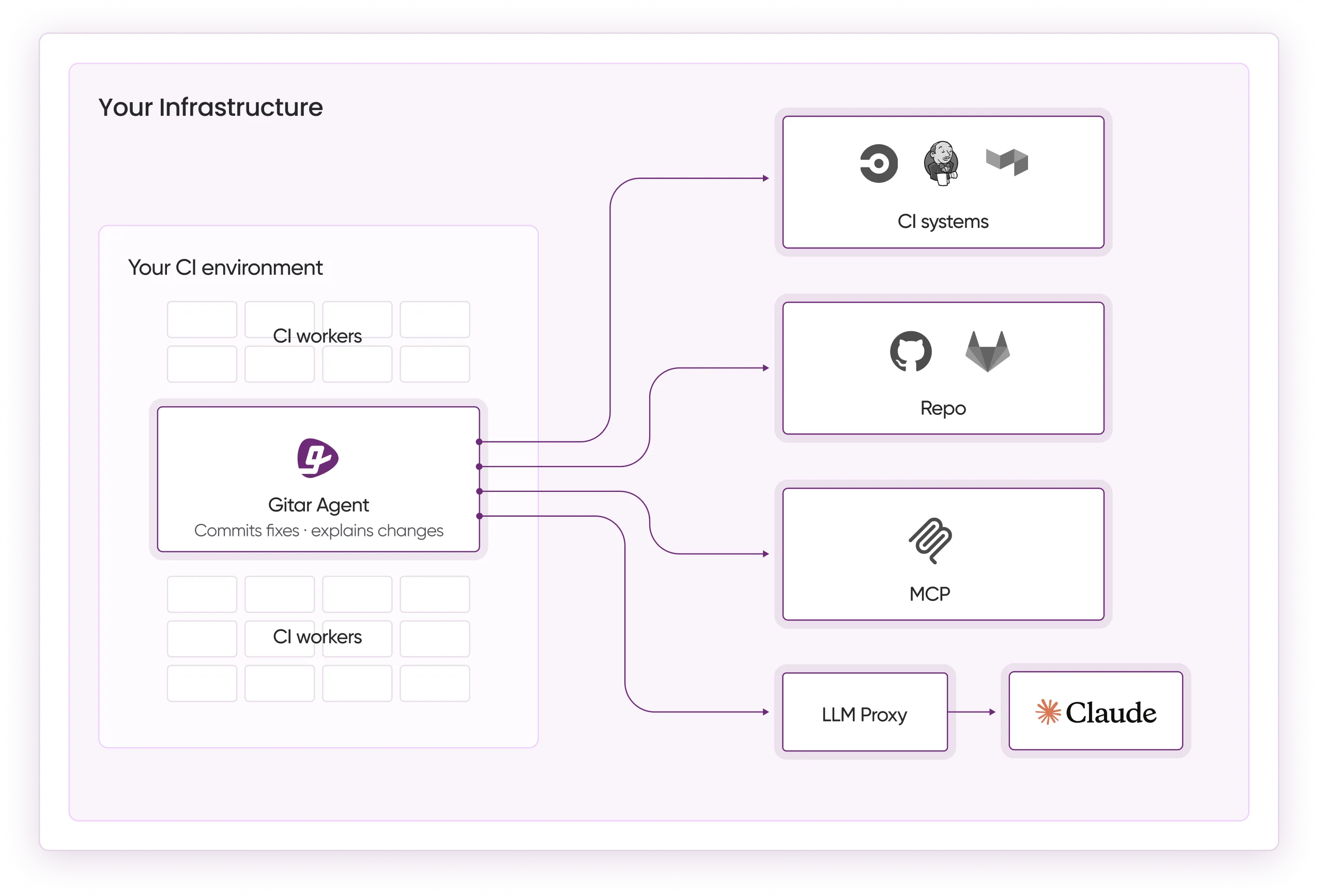
Automatically fix broken builds across large repository fleets with Gitar’s 14-day Team Plan trial, which requires no configuration.
Hands-On Troubleshooting for Qodo Multi-Repo Deployments
Real-world Qodo multi-repo deployments often encounter configuration propagation failures, token limit errors, and inconsistent behavior between repositories. Teams that hit token limits sometimes raise max_model_tokens beyond 32000, yet this change rarely solves issues for very large codebases or complex dependency graphs.
Merge command failures usually stem from insufficient permissions or incorrect webhook configurations. The /merge command also requires Pro tier access and proper repository permissions, so teams on the open-source version cannot rely on it across multiple repositories.
Performance problems tend to appear once organizations reach roughly 20 to 30 repositories. At that point, teams report agent timeouts, incomplete analysis, and slower feedback loops that undermine developer trust.
Instead of building fragile workarounds, many engineering groups now adopt platforms built for large multi-repo estates and automatic fix workflows, which reduces operational overhead.
FAQ: Qodo PR-Agent Multi-Repo Edition
Does Qodo PR-Agent support unlimited repositories?
No. Qodo PR-Agent encounters performance challenges around 30 repositories and faces token limits that hinder effective scaling. The architecture struggles in very large multi-repo environments, which makes it less suitable for organizations with broad repository portfolios.
What are the main limitations of Qodo’s multi-repo configuration?
Key limitations include token-based context restrictions, configuration propagation delays, and performance issues as repository counts grow. The hierarchical configuration system also adds complexity for some scaling scenarios.
Can Qodo PR-Agent automatically fix issues across multiple repositories?
Qodo PR-Agent offers one-click apply fixes in IDEs and targeted remediations. It does not automatically implement fixes, validate them against CI systems, or guarantee resolution without extra steps, which creates overhead in multi-repo environments.
How does Qodo’s Pro tier improve multi-repo support?
The Pro tier adds advanced context analysis, merge commands, cross-repository dependency mapping, and one-click apply fixes. Some architectural limits around tokens and performance scaling can still appear, especially in very large organizations.
What’s the best alternative for large-scale multi-repo AI code review?
Gitar provides no repository limits with automatic fixes that keep builds green. Unlike tools that rely on manual steps, Gitar’s healing engine validates fixes against your CI pipeline and commits working solutions directly to pull requests. The platform comfortably handles 100 or more repositories with zero configuration.
Qodo PR-Agent’s multi-repo configuration model highlights both its flexibility and its scaling challenges. The hierarchy helps organize settings, yet constraints around token limits, performance, and fix implementation reduce its suitability for some large deployments.
Engineering teams that need true multi-repo scalability increasingly choose platforms that fix issues automatically rather than only suggesting changes. Try Gitar’s 14-day Team Plan trial to experience unlimited repository capacity, zero-config setup, and CI-validated fixes across your entire portfolio.