Key Takeaways
- AI-generated code speeds up coding by 3 to 5 times but increases PR review times by 91%, which creates serious workflow bottlenecks.
- Qodo PR-Agent setup uses 8 steps, including GitHub App installation, .pr_agent.toml configuration, and a GitHub Actions workflow for auto-approval.
- Common issues such as token permissions, config file placement, and workflow triggers now have clear 2026 fixes and troubleshooting steps.
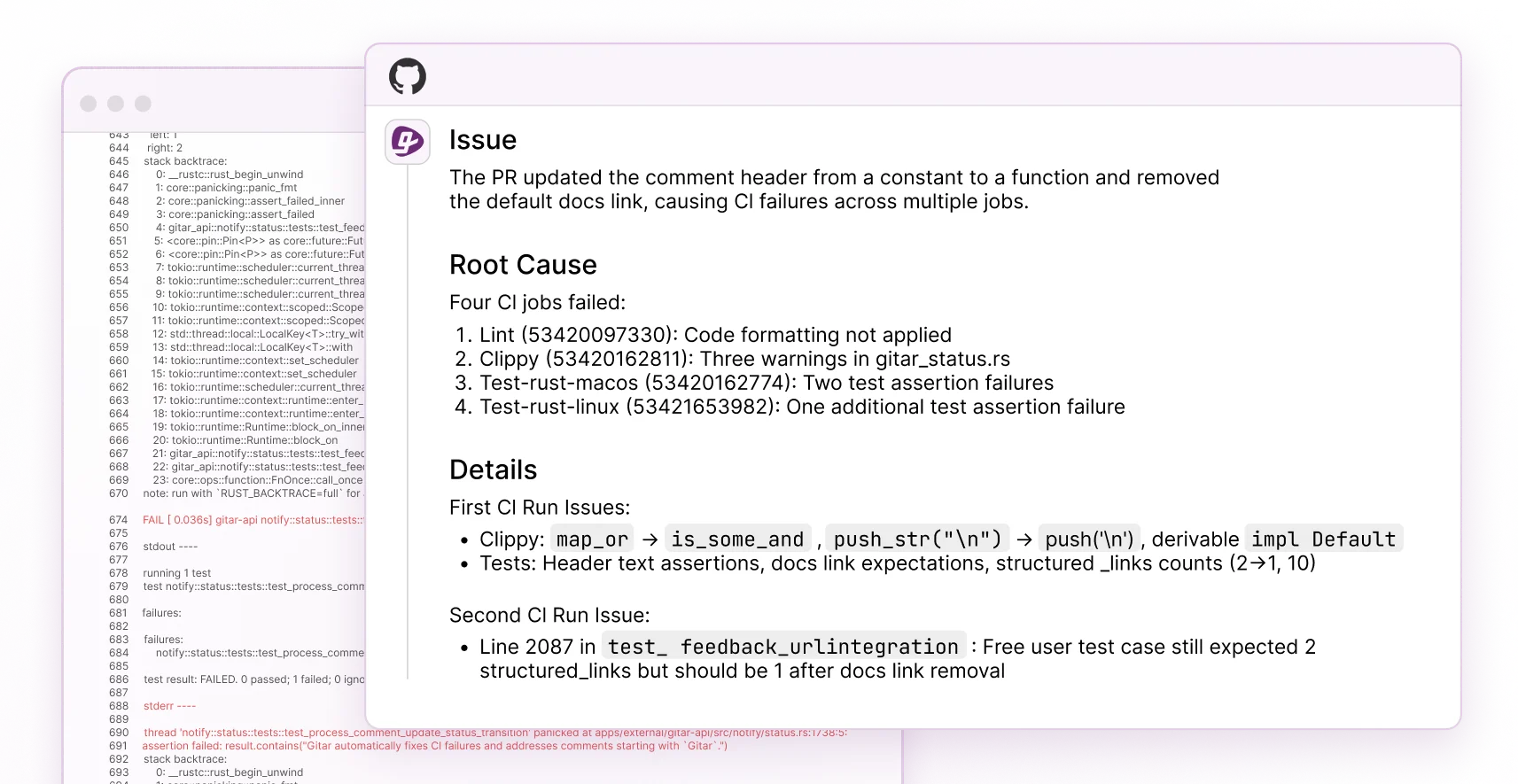
- Qodo supports interactive reviews but does not handle CI failures, unlike newer tools that apply autonomous fixes.
- Migrate to Gitar for natural language rules and automatic CI healing that fixes broken builds instead of only suggesting changes.
Step-by-Step Qodo PR-Agent GitHub Auto-Approval Setup
These 8 steps configure a working Qodo PR-Agent GitHub approval workflow with practical examples.
1. Install Qodo PR-Agent GitHub App
Go to the Qodo PR-Agent repository and install the GitHub App from the marketplace. Grant permissions for repository access, pull requests, and actions.
2. Create .pr_agent.toml Configuration
Add this file to your repository root on the default branch:
[pr_reviewer] auto_review = true require_focused_review = false require_score_review = false require_tests_review = false [pr_code_suggestions] auto_improve = true [github_app] auto_approve = true approve_pr_on_successful_check = true
3. Configure GitHub Actions Workflow
Create .github/workflows/pr-agent.yml with this content:
name: PR Agent on: pull_request: types: [opened, synchronize, reopened] issue_comment: types: [created, edited] jobs: pr_agent_job: runs-on: ubuntu-latest steps: – name: PR Agent action step uses: qodo-ai/pr-agent@main env: OPENAI_KEY: ${{ secrets.OPENAI_KEY }} GITHUB_TOKEN: ${{ secrets.GITHUB_TOKEN }}
4. Set Auto-Approve Rules
Define approval conditions in your .pr_agent.toml file:
[github_app] auto_approve = true approve_pr_on_successful_check = true auto_approve_when_tests_pass = true require_all_checks_to_pass = true
5. Test on a Sample Pull Request
Create a test pull request and comment /review to trigger the agent. Confirm that the approval workflow runs when CI passes.
6. Enable Multi-Agent Configuration
For advanced workflows, reference custom agent files in your GitHub Actions configuration with agent-file: path/to/agent.toml.
7. Integrate with Existing CI Systems
Ensure your GitHub Actions, CircleCI, or other CI systems run before PR-Agent evaluation so approvals reflect accurate CI results.
8. Confirm Approval Triggers Merges
Verify that successful PR-Agent approvals automatically merge pull requests when branch protection rules are satisfied.
2026 Update: This configuration resolves token permission issues introduced by recent GitHub releases.
Qodo PR-Agent configuration.toml Examples for Real Workflows
These three Qodo PR-Agent configuration.toml examples cover common production approval scenarios.
Basic Auto-Approve Configuration
[pr_reviewer] auto_review = true [github_app] auto_approve = true approve_pr_on_successful_check = true
Security-Gated Approval
[pr_reviewer] auto_review = true require_security_review = true [github_app] auto_approve = false manual_approve_for_security_changes = true
Multi-Agent Workflow
[pr_reviewer] auto_review = true enable_multi_agent = true [github_app] auto_approve = true require_all_agents_approval = true
Review the complete configuration options in the official repository for more advanced customization.
Fixing Common Qodo Auto-Approve Problems
These steps resolve the most frequent Qodo auto-approve issues.
Token Permission Errors (#1482)
• Confirm that GITHUB_TOKEN has write permissions for pull requests.
• Verify that the GitHub App installation includes approval permissions.
• Check that branch protection rules allow approvals from apps.
Configuration File Not Found (#856)
• Place .pr_agent.toml in the repository root, not in subdirectories.
• Commit the configuration to the default branch before testing.
• Verify that the file uses UTF-8 encoding without BOM.
Workflow Trigger Issues
• Use the pull_request_target event for pull requests from forks.
• Add the synchronize trigger for updated pull requests.
• Inspect GitHub Actions logs for authentication or permission failures.
Rate Limiting Problems
• Configure API rate limits in .pr_agent.toml.
• Prefer organization-level tokens instead of personal tokens.
• Add retry logic for transient API failures.
These 2026 updates address the most common setup failures reported by the Qodo community.
Why Gitar Outperforms Qodo PR-Agent for CI and Reviews
Qodo PR-Agent delivers basic approval workflows but falls short compared to modern autonomous review and repair tools.
|
Feature |
Qodo PR-Agent |
Gitar |
|
PR Reviews |
Interactive reviews and suggested improvements |
Auto-fixes and CI healing. See Gitar docs |
|
Approval Workflow |
TOML-based configuration |
Natural language rules. See Gitar docs |
|
CI Failures |
No handling |
Automatic analysis, fix, and commit. See Gitar docs |
|
Setup Time |
Hours of configuration |
Thirty-second installation. See Gitar docs |
Qodo PR-Agent depends on TOML configuration, offers interactive review tools that still require developer oversight, and provides no CI failure resolution. When a build breaks, your team returns to manual debugging.
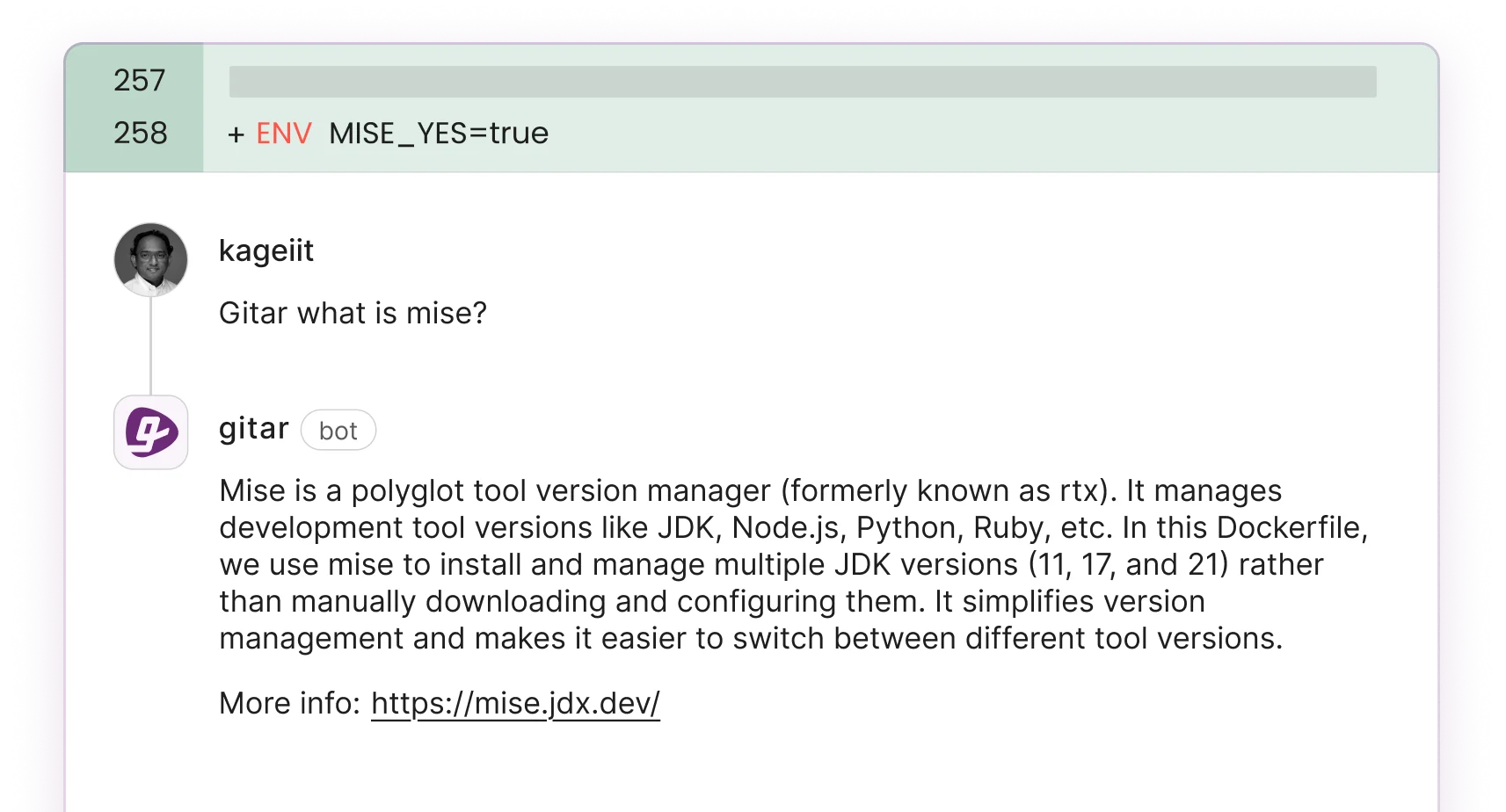
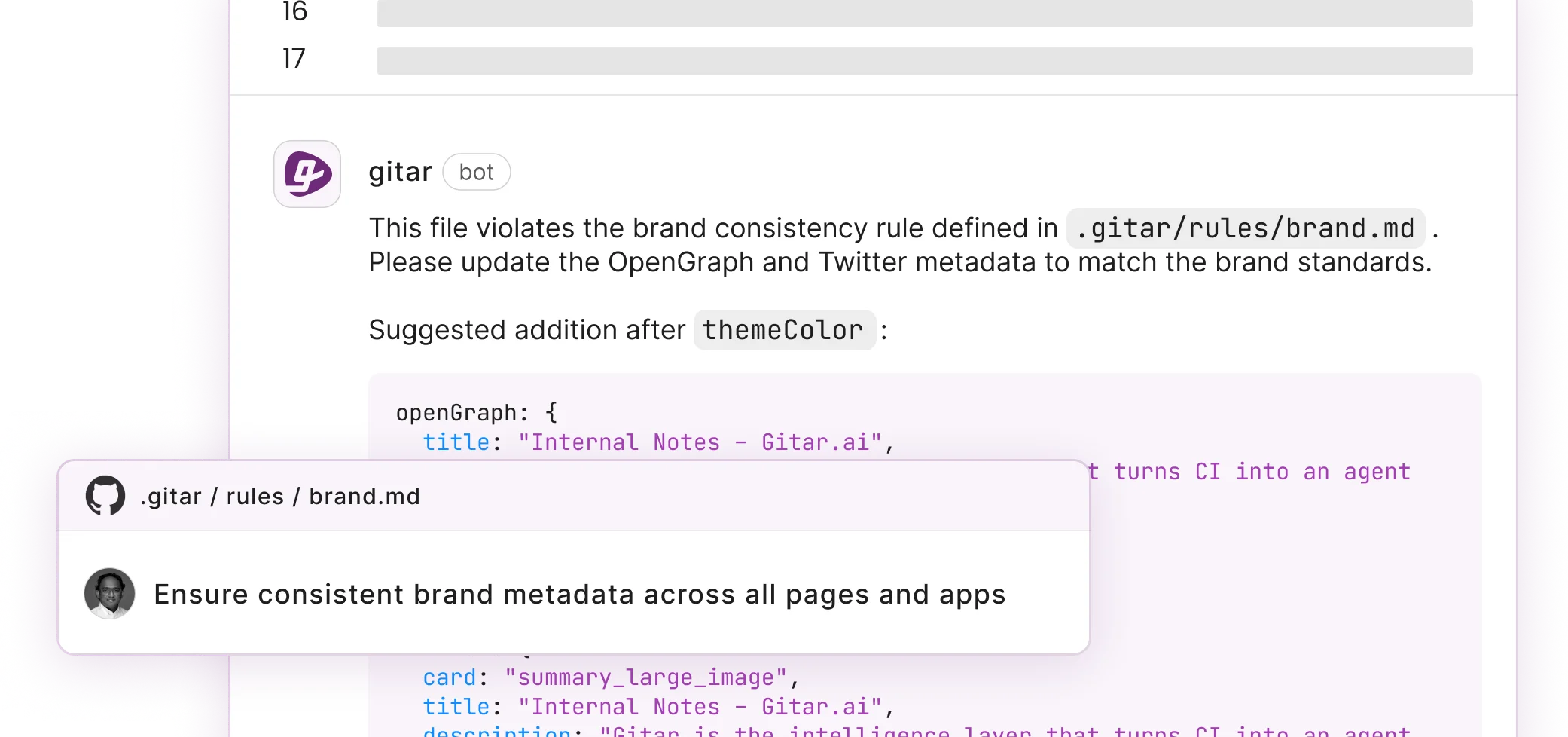
Gitar’s healing engine analyzes CI failures, generates validated fixes, and commits them directly to your pull requests. Instead of managing .pr_agent.toml files, you define simple rules in natural language. The Gitar documentation explains how teams cut review time with autonomous fixes.
Install Gitar now to automatically fix broken builds and ship higher quality software faster.
Advanced Qodo Tips and a Clear Gitar Migration Path
Teams that outgrow Qodo’s review-focused model can move to Gitar for deeper automation without disrupting existing workflows.
— title: “Auto-fix lint errors” when: “CI fails with ESLint violations” actions: “Fix and commit automatically” —
This natural language style removes complex TOML configuration and adds the auto-fixes that Qodo PR-Agent does not provide. Teams keep their current approval workflows and gain autonomous problem resolution. See Gitar docs for migration details.
How Qodo Setup Fits into a 2026 CI Strategy
This Qodo PR-Agent GitHub approval workflow guide gives you configuration examples and troubleshooting steps that match 2026 GitHub behavior. It fits teams that want structured reviews but still accept manual fixes.
Gitar’s autonomous healing engine represents the next step. It delivers real fixes instead of suggestions, natural language rules instead of complex TOML, and consistently green builds instead of repeated manual debugging cycles. Install Gitar now to automatically repair broken builds and ship higher quality software faster.
FAQ
Why Qodo auto-approve often fails in GitHub workflows
The most common causes include insufficient GitHub token permissions, incorrect branch protection settings, and misconfigured .pr_agent.toml files. Confirm that your GITHUB_TOKEN has write access to pull requests and that the GitHub App installation includes approval permissions. Make sure your configuration file is committed to the default branch and that branch protection rules allow automated approvals from GitHub Apps, not only human users.
Recommended PR-Agent configuration.toml for production
A production-ready configuration typically sets auto_review = true, require_all_checks_to_pass = true, and appropriate security gates. Enable auto_approve only after thorough testing and always require CI success before approval. Use multi-agent workflows for complex repositories that need specialized reviews such as security or performance validation.
How to configure Qodo PR-Agent for GitLab instead of GitHub
Qodo PR-Agent supports GitLab through webhooks and GitLab CI/CD pipelines. Place a .pr_agent.toml file in your repository root, configure GitLab webhooks to trigger on merge request events, and use GitLab CI variables for API keys. The agent responds to GitLab merge request comments with commands such as /review and /improve, which mirrors the GitHub experience.
Key differences between Gitar and Qodo for automated code review
Gitar provides autonomous fixes, while Qodo focuses on interactive reviews and suggested improvements. When CI fails, Gitar analyzes the error, generates a working fix, validates it, and commits the solution automatically. Qodo still requires a developer to apply changes. Gitar uses natural language rules instead of TOML configuration, offers a 14-day free trial of full Team Plan features, and includes broad CI healing across multiple platforms.
Trying Gitar’s auto-fix capabilities with a free trial
Gitar offers a 14-day free trial of the Team Plan with full access to auto-fix capabilities, CI healing, custom rules, and all integrations. Unlike competitors that charge 15 to 30 dollars per developer for suggestion-only tools, you can test Gitar’s complete autonomous development platform before making any commitment. The trial gives full access so your team can measure the impact directly.
