Written by: Ali-Reza Adl-Tabatabai, Founder and CEO, Gitar
Key Takeaways
- Vague natural language rules in Qodo PR-Agent cause AI hallucinations, increase PR review times by 91%, and still require manual fixes.
- Natural language configurations via TOML, best_practices.md, and CLI commands enforce security, style, and documentation, but Qodo lacks deep examples and hands-free execution.
- Gitar surpasses Qodo with automatic commits via .gitar/rules/*.md files, saving 45 minutes per developer daily by removing interactive fix steps.
- Copy-paste examples in this guide cover Python and JavaScript security, style, docs, testing, and common rule-writing pitfalls.
- Teams can move from Qodo’s suggestion-only model to Gitar’s full automation for consistently green builds without intervention. Start a Gitar trial to ship higher quality software faster.
Why Natural Language Rules Matter for AI PR Review
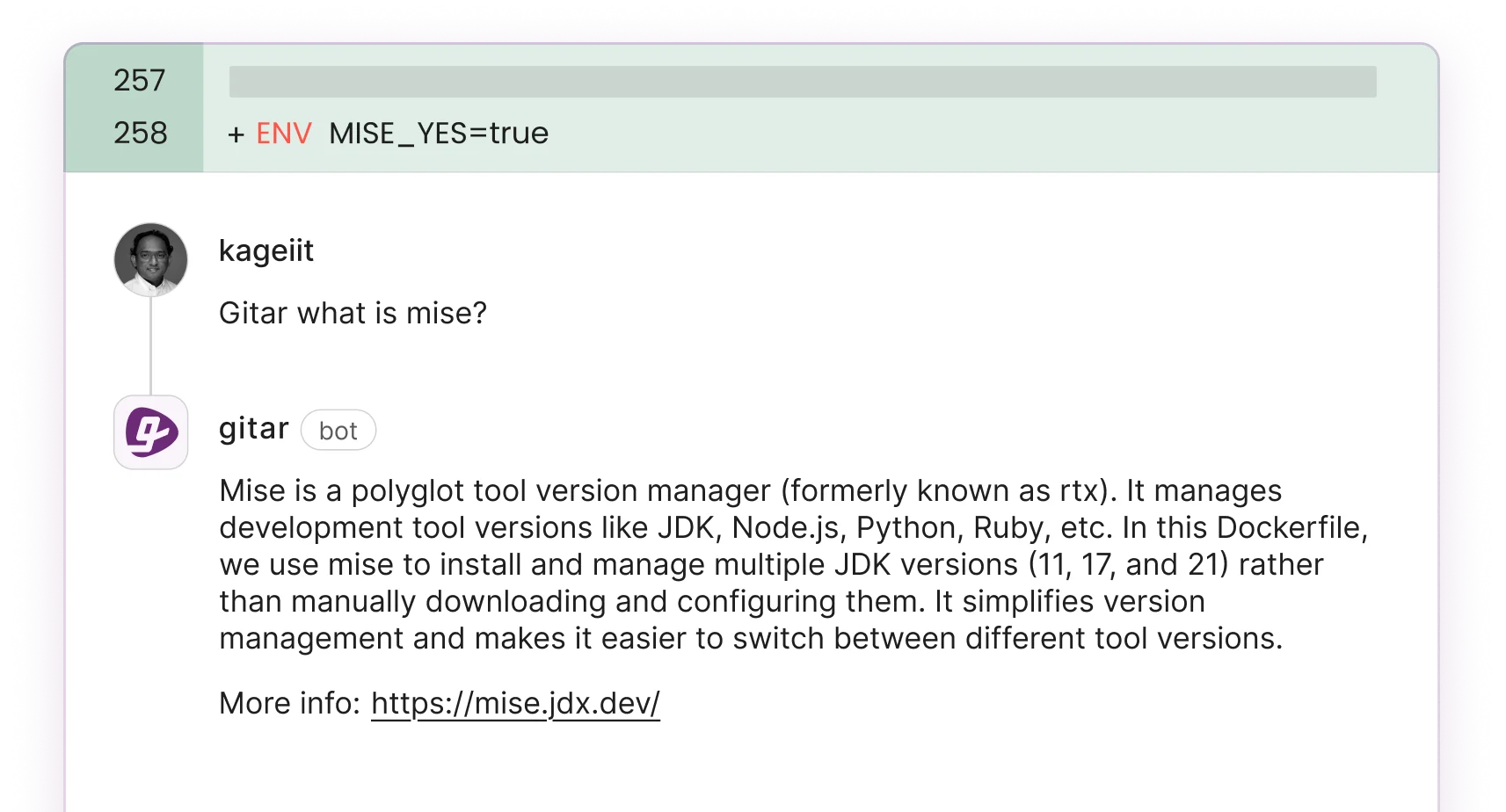
AI code generation accelerates output, which creates a new bottleneck: teams must review far more code without adding reviewers. Natural language configuration through TOML extra_instructions, best_practices.md files, and CLI –extra_instructions parameters gives teams a practical way to enforce security checks, code style, and documentation standards without complex YAML workflows. Qodo CLI supports custom agent configuration that turns natural language into intelligent actions, including interactive chat mode, custom commands, and MCP integration.
Qodo still leaves critical gaps. The tool lacks comprehensive Python and JavaScript workflow examples and clear troubleshooting guidance for rule ambiguity. Most importantly, it does not apply fixes on its own. Qodo offers interactive suggestion application, while Gitar moves to fully automatic commits.
Gitar: Automatic Healing Beyond Qodo Suggestions
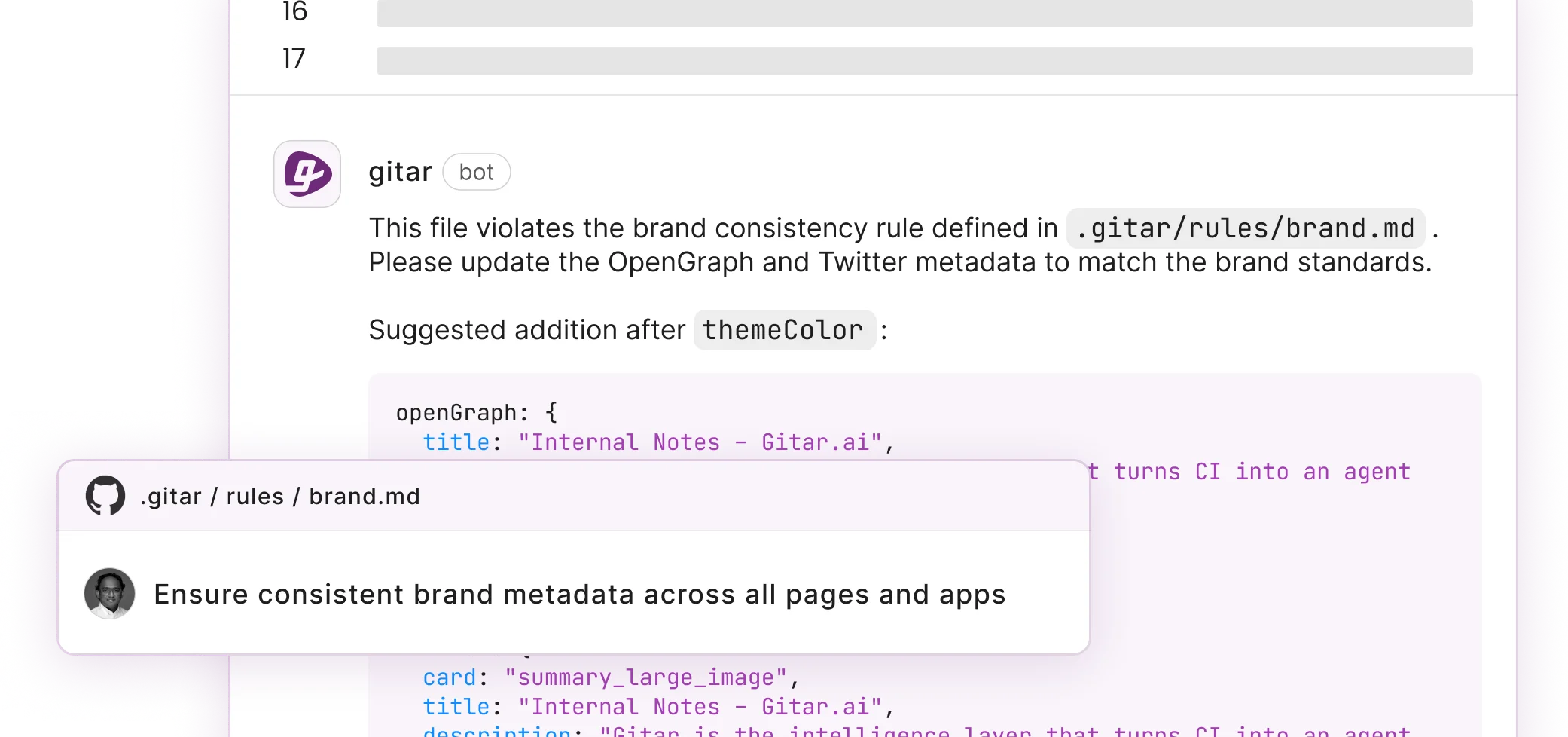
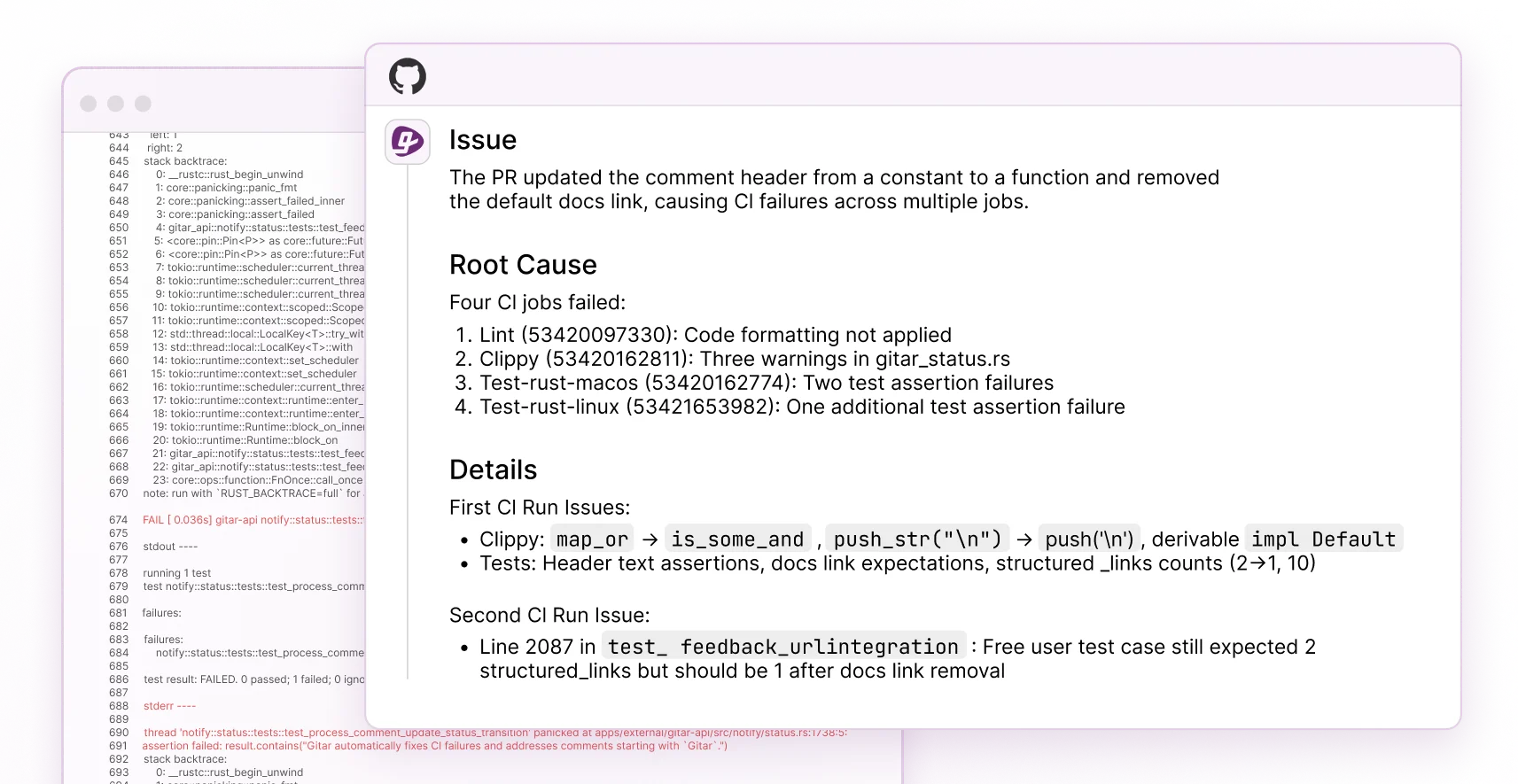
Gitar’s Healing Engine turns natural language rules into self-healing implementations. Qodo presents suggestions that developers must apply, but Gitar uses .gitar/rules/*.md files to trigger fixes and CI commits with no manual steps. Gitar’s documentation explains how natural language rules resolve CI failures, implement review feedback, and keep builds green. Configuration details appear in the Gitar rules configuration guide.
The following comparison highlights the automation gap between Qodo’s interactive approach and Gitar’s hands-free implementation.
|
Feature |
Qodo PR-Agent |
Gitar |
|
Fix Application |
Interactive checkboxes |
Auto-commits |
|
CI Integration |
Limited analysis |
Full auto-fix |
|
Rules Format |
TOML/MD files |
Natural language .md |
|
Time Savings |
Interactive implementation |
45 min/day/developer |
See how Gitar’s automatic implementation removes the interaction bottleneck you face with Qodo
10+ Copy-Paste Examples: Master Qodo Configurations
Five Core Qodo Configuration Methods
These five Qodo PR-Agent configuration methods form a progression from permanent repository rules to per-review customization. Together they create a complete rule system.
- TOML extra_instructions for pr_reviewer and pr_code_suggestions as baseline rules that apply to every review.
- Repository-level best_practices.md templates as shared team standards that extend TOML configuration.
- CLI qodo merge commands with dynamic rules as context-specific overrides for individual pull requests.
- Global response_language and severity settings as cross-repository defaults for consistent behavior.
- Qodo 2.1+ CLI agents and MCP integration as advanced options for complex, automated workflows.
Qodo PR Agent extra_instructions Examples (TOML)
Security-Focused Python Configuration:
[pr_reviewer] extra_instructions = “”” 1. Scan for SQL injection vulnerabilities in database queries 2. Check for hardcoded secrets or API keys in authentication code 3. Verify input validation on user-facing endpoints 4. Enforce secure password hashing (bcrypt, scrypt, argon2) 5. Flag missing CSRF protection in form handlers “”” [pr_code_suggestions] extra_instructions = “”” 1. Suggest secure alternatives for identified vulnerabilities 2. Recommend proper exception handling for security errors 3. Add logging for security-relevant events “””
Style Enforcement JavaScript Configuration:
[pr_reviewer] extra_instructions = “”” 1. Enforce ESLint rules and Prettier formatting 2. Check for consistent async/await usage over Promises 3. Verify proper TypeScript type annotations 4. Flag unused imports and variables 5. Ensure consistent naming conventions (camelCase) “”” focus_areas = “style,performance,maintainability” severity_threshold = “medium”
Documentation Standards Configuration:
[pr_add_docs] docs_style = “Google Style” extra_instructions = “”” 1. Add JSDoc comments to all exported functions 2. Include parameter types and return value descriptions 3. Provide usage examples for complex functions 4. Update README.md for API changes “””
GitHub PR Agent best_practices.md Templates
Create a comprehensive best_practices.md file in your repository root to give Qodo a single source of truth for standards.
# Team Code Standards ## Security Requirements – All user inputs must be validated and sanitized – Use parameterized queries for database operations – Implement proper authentication and authorization – Log security events for audit trails ## Code Style – Follow PEP 8 for Python, ESLint for JavaScript – Maximum line length: 88 characters – Use descriptive variable names reflecting purpose – Include type hints for all function parameters ## Documentation – Add docstrings to all public functions – Update API documentation for endpoint changes – Include inline comments for complex logic – Maintain changelog for breaking changes ## Testing – Minimum 80% code coverage for new features – Include both unit and integration tests – Test error handling and edge cases – Mock external dependencies in tests
Qodo Merge Commands for Dynamic Rules
Use CLI commands when a specific pull request needs a focused review that goes beyond your default rules.
# Security-focused review /review –pr_reviewer.extra_instructions=”Focus on authentication and data validation security issues” # Performance optimization review /review –pr_reviewer.extra_instructions=”Identify performance bottlenecks, memory leaks, and optimization opportunities” # API consistency check /review –pr_reviewer.extra_instructions=”Ensure API endpoints follow REST conventions and maintain backward compatibility” # Documentation completeness /review –pr_reviewer.extra_instructions=”Verify all public methods have docstrings and README updates reflect changes”
Qodo PR Agent Python Configuration Examples
Language-specific Python rules help Qodo catch patterns that general rules often miss.
[pr_reviewer] extra_instructions = “”” 1. Enforce PEP 257 docstring conventions 2. Check for proper exception handling with specific exception types 3. Verify f-string usage over .format() or % formatting 4. Flag mutable default arguments in function definitions 5. Ensure proper use of context managers for file operations “”” [pr_code_suggestions] focus_areas = “docstrings,comments,naming,performance” include_suggestions = true
Common Natural Language Rule Pitfalls
Clear rules reduce hallucinations and keep Qodo focused on the changes that matter.
- Be Specific: Replace “check security” with “scan for SQL injection in user authentication queries.”
- Use Lists: Numbered or bulleted instructions reduce confusion for the AI model.
- Avoid Ambiguity: Swap “improve code quality” for “enforce consistent naming conventions and add missing docstrings.”
- Set Boundaries: Say “only review added lines” when you want to avoid noisy suggestions.
- Test Incrementally: Start with 2–3 rules, validate results, then expand your ruleset.
Qodo’s best practices generation helps teams create consistent standards, but Qodo still requires interaction for every fix. Gitar, in contrast, applies rules on its own. Compare this Gitar rule that resolves issues without manual steps. Full details appear in the Gitar documentation:
— title: ‘Security Review’ when: ‘PRs modifying authentication or encryption code’ actions: ‘Auto-fix common vulnerabilities and assign security team’ —
Social Proof: Impact on PR Speed and Quality
AI code generation tools enable developers to output 2–3x more code, creating a “Review Gap” where human review capacity remains flat. That gap leads to piled-up pull requests and slower deployments. Qodo shortens analysis time with context-aware reviews and interactive fix application, yet teams still spend significant effort on complex changes.
Gitar removes this manual overhead. Teams report the time savings mentioned earlier, 45 minutes per developer per day, through automatic fix implementation. One engineering lead notes that Gitar’s “unrelated PR failure detection” saves “significant time” by separating infrastructure issues from code bugs, context that traditional reviewers rarely provide.
Start your free Gitar trial and reclaim review time on every pull request
FAQ: Qodo Rule Tuning and Gitar Advantages
How do I avoid Qodo rule hallucinations and model confusion?
Write specific, actionable instructions using numbered lists and concrete examples. Instead of vague directives like “improve security,” specify “scan for hardcoded API keys in config files and environment variables.” This clarity reduces ambiguity, but you also need verification. Use groundedness checks to verify claims are supported by retrieved sources, and combine multiple grader types like LLM rubrics and tool call verification. After you define precise rules and checks, test them incrementally, starting with 2–3 instructions so you can see which ones produce reliable results before you scale up.
What’s the difference between Qodo and Gitar natural language rules?
Qodo rules generate interactive suggestions via checkboxes for quick application, while Gitar rules trigger fixes and commits on their own. Qodo uses TOML extra_instructions and best_practices.md files for configuration, which lets developers apply changes interactively. Gitar’s .gitar/rules/*.md files describe desired outcomes in natural language, then carry out fixes, validate against CI, and commit working solutions, which removes the need for interaction.
Can you provide more Python-specific TOML configuration examples?
Focus on Python patterns such as PEP compliance, precise exception handling, and documentation standards. Use configurations like docs_style = “PEP257” for docstring enforcement and focus_areas = “docstrings,comments,naming” for code quality. Add instructions for common Python issues like mutable default arguments, context manager usage, and f-string adoption. The examples above show complete Python rule configurations for security, style, and documentation.
How do I measure the effectiveness of my natural language rules?
Track metrics such as PR review time reduction, number of manual fixes required after AI suggestions, and developer satisfaction with rule clarity. Monitor false positive rates so rules do not generate irrelevant suggestions. Consider moving to Gitar’s autonomous implementation model to remove manual fix overhead and measure actual time savings from automatic resolution of CI failures and review feedback.
What are the limitations of Qodo’s suggestion-only approach?
Qodo requires interactive steps to apply suggestions through checkboxes. Even with well-written natural language rules, developers must select and apply fixes, which slows complex changes. Gitar closes this gap by implementing, validating, and committing fixes automatically, turning suggestions into reliable, production-ready changes without extra clicks.
Conclusion: Move From Interactive Suggestions to Automatic Healing
This guide helps you master Qodo PR-Agent natural language configuration with practical copy-paste examples. These TOML extra_instructions, best_practices.md templates, and CLI commands raise review quality, yet they still depend on interactive application, which limits development velocity.
Gitar’s Healing Engine advances beyond Qodo’s interactive approach by applying natural language rules automatically to keep builds green and remove manual toil. Teams experience the difference between AI that only suggests changes and AI that fixes code for them.
Experience hands-free code fixes with Gitar’s Healing Engine today