Written by: Ali-Reza Adl-Tabatabai, Founder and CEO, Gitar
Key Takeaways
- Qodo PR Agent connects to CI/CD through Docker images for GitHub Actions, GitLab CI, CircleCI, and Buildkite using tokens and config files.
- Use dotted notation such as config.model for environment variables to prevent model configuration failures reported in GitHub issues.
- Core commands include /review for code analysis, /describe for PR summaries, /improve for enhancements, and /ask for targeted questions.
- Common pitfalls fall into three categories: token permission gaps, Docker image updates that break commands, and authentication failures with LLM providers. The troubleshooting section below explains how health checks, dotted notation, and fallback models address each problem.
- Move beyond Qodo’s suggestion-only workflow with Gitar’s zero-config CI healing that auto-fixes failures, validates changes in your build environment, and keeps pipelines green.
Core Requirements for Qodo: 5 Sequential Setup Steps
Follow these five connected steps to integrate Qodo PR Agent into your CI/CD pipeline. Each step builds on the previous one to create a working configuration.
- Docker Setup: Start by pulling the official Docker image. Use codiumai/pr-agent:0.32-github_action for GitHub Actions or codiumai/pr-agent:0.32-gitlab_webhook for GitLab CI. This image provides the runtime for all later steps.
- Token Configuration: With the image defined, configure authentication tokens as secrets. Use GITHUB_TOKEN for GitHub Actions, GITLAB_TOKEN for GitLab CI, and add your LLM provider key such as GOOGLE_AI_STUDIO.GEMINI_API_KEY.
- Workflow Triggers: After authentication is in place, define when Qodo runs. Configure triggers for pull request opened and synchronize events in GitHub Actions, or merge request events in GitLab CI.
- Configuration File: Once triggers are set, create .pr_agent.toml in the repository root. Add model settings like [config] model=’gemini/gemini-1.5-flash’ and a command list such as [‘review’,’describe’].
- Language Configs: Finally, extend the configuration with language-specific settings for Python, JavaScript, Go, or other supported languages so reviews match your stack.
GitHub Actions Setup for Qodo PR Agent (2026 Guide)
Create a .github/workflows/pr-agent.yml file in your repository with this configuration:
name: PR Agent on: pull_request: types: [opened, synchronize] permissions: contents: read pull-requests: write checks: write jobs: pr_agent: runs-on: ubuntu-latest steps: – name: Checkout uses: actions/checkout@v4 with: fetch-depth: 0 – name: Run PR Agent run: | docker run –rm \ -e GITHUB_TOKEN=”${{ secrets.GITHUB_TOKEN }}” \ -e config.model=”gemini/gemini-1.5-flash” \ -e config.fallback_models='[“gemini/gemini-1.5-flash”]’ \ -e GOOGLE_AI_STUDIO.GEMINI_API_KEY=”${{ secrets.GEMINI_API_KEY }}” \ -e config.git_provider=”github” \ codiumai/pr-agent:0.32-github_action \ –pr_url=”${{ github.event.pull_request.html_url }}” \ review describe
Focus on these configuration details for a stable GitHub Actions integration.
- Environment Variables: Use dotted notation like config.model instead of PR_AGENT.MODEL. This mistake causes model configuration to be ignored.
- Gemini Setup: For Google Gemini models, set GOOGLE_AI_STUDIO.GEMINI_API_KEY instead of GOOGLE_API_KEY.
- Secrets Management: Store API keys in GitHub under Settings > Secrets and variables > Actions.
- Permissions: Confirm the workflow includes pull-requests: write so Qodo can post comments.
For OpenAI models, replace the Gemini configuration with:
-e config.model=”gpt-4o” \ -e OPENAI_API_KEY=”${{ secrets.OPENAI_API_KEY }}”
GitLab CI Configuration for Qodo PR Agent
Add this job to your .gitlab-ci.yml file:
stages: – review pr_agent_review: stage: review image: codiumai/pr-agent:0.32-gitlab_webhook variables: GITLAB_TOKEN: $GITLAB_TOKEN config.model: “gemini/gemini-1.5-flash” config.git_provider: “gitlab” GOOGLE_AI_STUDIO.GEMINI_API_KEY: $GEMINI_API_KEY script: – python -m pr_agent.cli –pr_url=”$CI_MERGE_REQUEST_PROJECT_URL/-/merge_requests/$CI_MERGE_REQUEST_IID” review describe rules: – if: $CI_PIPELINE_SOURCE == “merge_request_event” – if: $CI_MERGE_REQUEST_EVENT_TYPE == “merge_request”
Account for these GitLab-specific details.
- Token Handling: Set GITLAB_TOKEN as a non-protected CI/CD variable in project settings.
- SSL Verification: For self-hosted GitLab, adjust SSL verification if your certificates cause connection issues.
- Draft MRs: This configuration works across draft and ready states without extra rules.
- Multi-language Support: Qodo supports language-specific configurations for translating generated output.
Fast Qodo Integration for CircleCI and Buildkite
For CircleCI, add this job to your .circleci/config.yml:
jobs: pr_agent: docker: – image: codiumai/pr-agent:0.32-github_action environment: – config.model: “gpt-4o” – OPENAI_API_KEY: $OPENAI_API_KEY steps: – run: python -m pr_agent.cli –pr_url=”$CIRCLE_PULL_REQUEST” review
For Buildkite, create this pipeline step:
steps: – label: “PR Agent Review” command: | docker run –rm \ -e config.model=”gpt-4o” \ -e OPENAI_API_KEY=”$$OPENAI_API_KEY” \ codiumai/pr-agent:0.32-github_action \ –pr_url=”$$BUILDKITE_PULL_REQUEST” review
Qodo Commands You Can Run in CI/CD
Qodo PR Agent exposes several commands that you can wire into your CI pipeline.
- /review: Runs a detailed code review and returns suggestions.
- /describe: Generates summaries and descriptions for the pull request.
- /improve: Suggests performance and code quality improvements.
- /ask: Answers targeted questions about the code changes.
Configure multiple commands through an environment variable:
-e PR_AGENT_COMMANDS='[“/review”,”/improve”,”/describe”]’
After you configure these commands, you may still encounter integration issues. The next section covers the most frequent problems and how to fix them.
Common Qodo Integration Pitfalls and Practical Fixes
Recent GitHub issues and community reports highlight a few recurring problems. Use these patterns to diagnose and resolve them quickly.
Model Configuration Issues
GitHub issue #2083 shows that PR_AGENT.MODEL environment variables are ignored. Use dotted notation instead.
- ❌ PR_AGENT.MODEL=gemini-pro
- ✅ config.model=gemini/gemini-1.5-pro
Docker Image Problems
Recent Docker image updates broke the /describe command because of missing configuration. Add fallback models to reduce failures.
config.fallback_models='[“gpt-4o”,”gpt-4″]’
Token Authentication Failures
Use a consistent checklist when debugging authentication problems.
- Confirm token scopes include repository access and pull request write permissions.
- Run the health check with python -m tests.health_test.main.
- Enable configuration debugging using /describe –config.output_relevant_configurations=true.
These steps reduce friction with Qodo’s setup. For teams that want to avoid manual configuration and recovery work entirely, the Gitar documentation explains how zero-setup CI healing removes these integration headaches.
Industry Landscape in 2026 and the Qodo vs Gitar Gap
The AI code review market in 2026 centers on suggestion-based tools. CodeRabbit and Greptile charge about $15–30 per developer for suggestion-only features, while Qodo offers deeper analysis with interactive checkboxes for applying fixes.
|
Capability |
Qodo PR Agent |
Gitar |
|
Auto-fix CI failures |
No |
Yes |
|
Guarantee green builds |
No |
Yes |
|
Single comment (no spam) |
No |
Yes |
|
Natural language rules |
Limited |
Yes |
|
Validates fixes against CI |
No |
Yes |
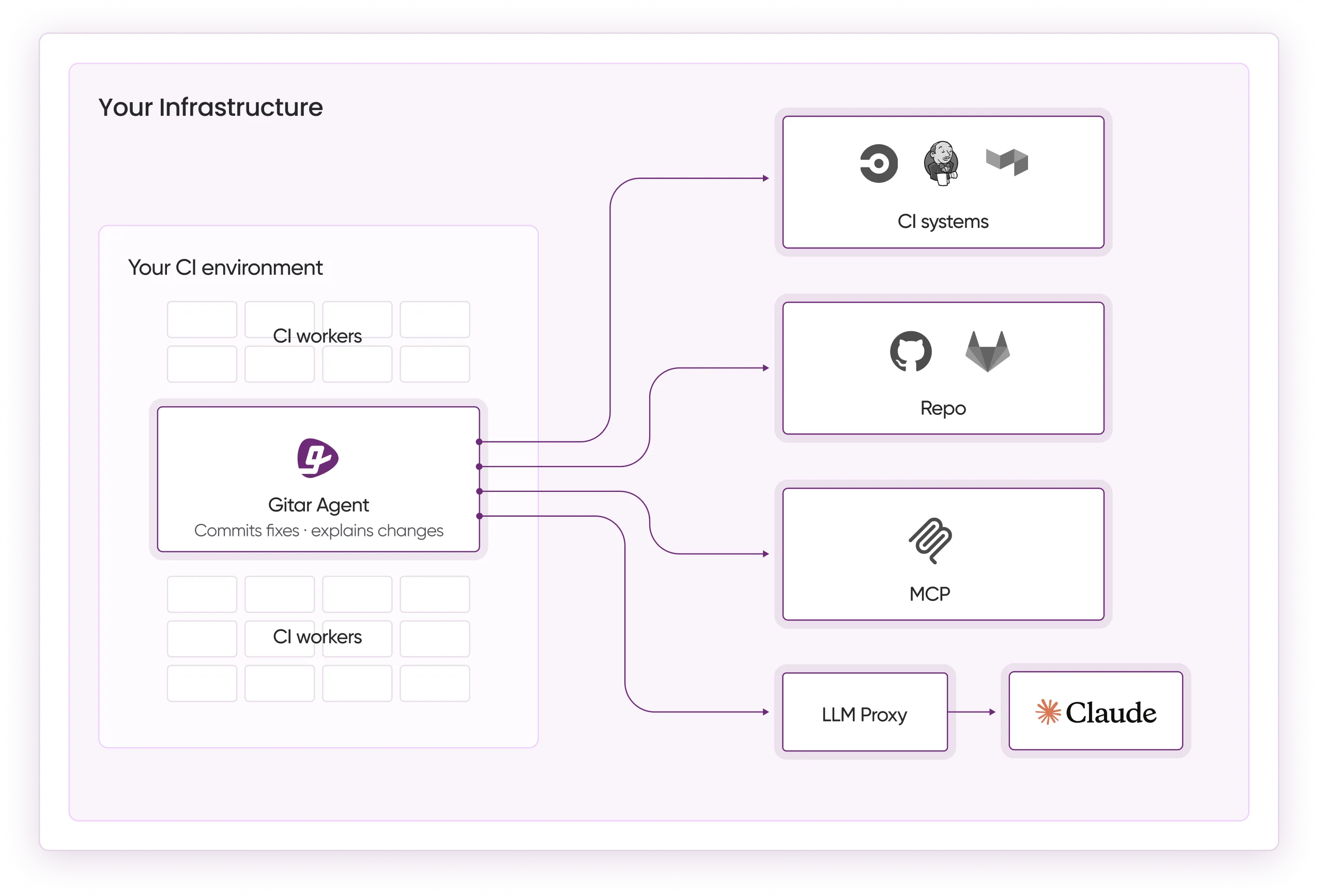
The comparison table highlights a key shift. Qodo focuses on interactive fixes, while Gitar’s CI Failure Analysis deduplicates failures across jobs, surfaces root causes, and keeps information updated in real time while committing validated fixes.
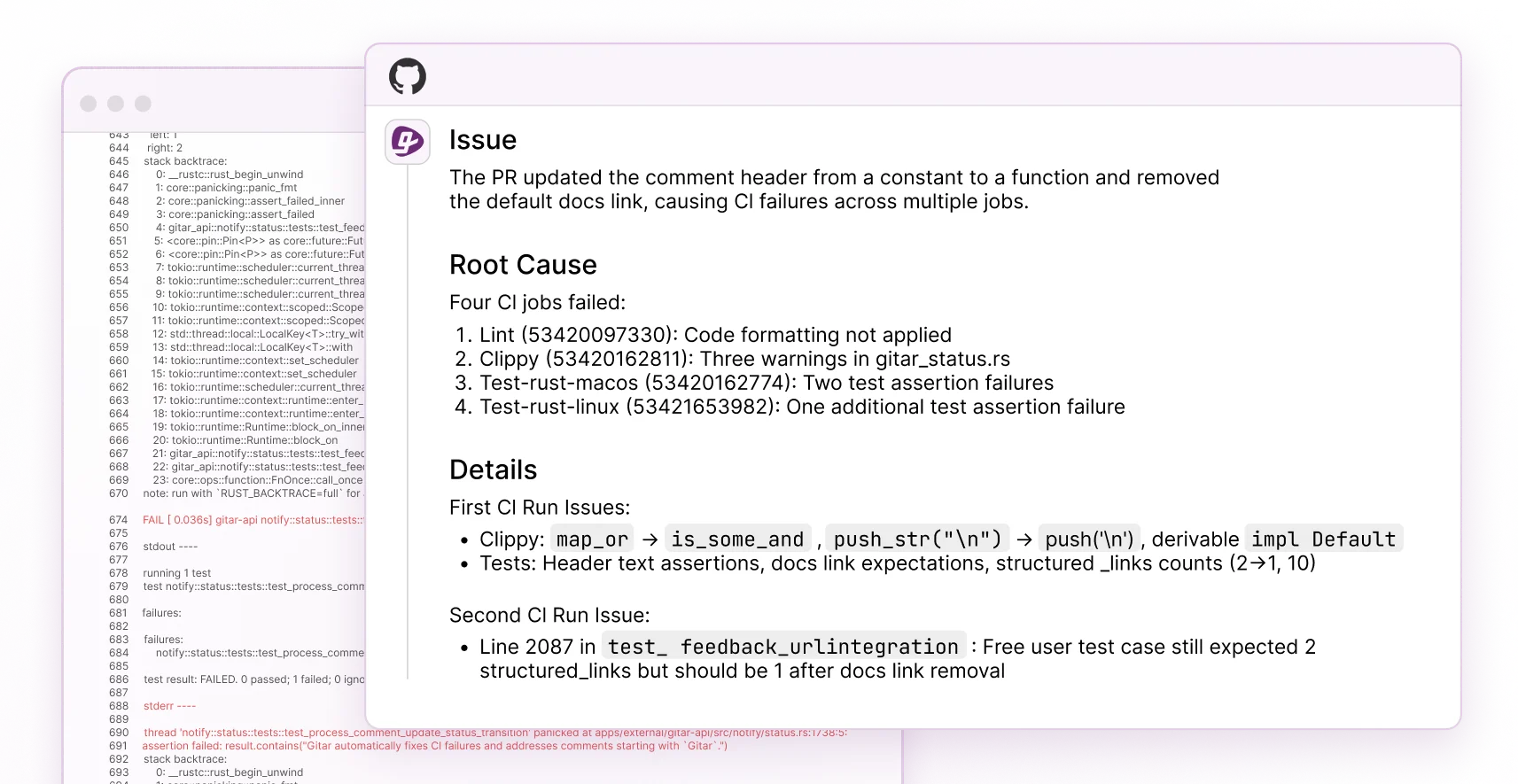
Gitar added CI failure analysis in October 2025, automatically analyzing failures and posting insights in dashboard comments that update with new commits. This capability marks the move from suggestion engines to the healing engine model described earlier.
Why Teams Upgrade from Qodo to Gitar for CI/CD Automation
Qodo PR Agent depends on YAML configuration and manual application of suggested fixes. Gitar focuses on autonomous CI healing with measurable impact. For a 20-developer team that spends 1 hour per day on CI issues, Gitar’s CI agent keeps context from PR open to merge, works continuously to keep CI green, finds root causes, applies fixes, and verifies results.
These advantages explain why teams move from interactive review to automated healing.
- Zero Configuration: Works without complex YAML files or Docker wiring.
- Automatic Fixes: Commits validated solutions instead of leaving suggestions for developers to apply.
- Full Context: Understands your codebase and CI environment together.
- Natural Language Rules: Express complex workflows as prompts instead of scripts.
- Proven ROI: Delivers around $1M per year in productivity savings for mid-size teams.
FAQ
How does Qodo PR Agent compare to Gitar for CI/CD automation?
Qodo PR Agent analyzes code and provides interactive suggestions through checkboxes, and developers still review and commit changes. Gitar automatically analyzes CI failures, generates validated fixes, and commits them directly to pull requests. Qodo relies on YAML configuration and Docker setup, while Gitar runs with zero configuration. As outlined in the comparison table, Qodo acts as an interactive assistant and Gitar functions as a healing engine that focuses on keeping builds green.
What is the basic GitLab CI/CD setup primer for Qodo PR Agent?
For GitLab CI integration, create a job in .gitlab-ci.yml that runs on merge request events using the codiumai/pr-agent Docker image. Set GITLAB_TOKEN as a non-protected CI/CD variable, configure LLM provider credentials such as GOOGLE_AI_STUDIO.GEMINI_API_KEY, and use dotted notation for variables like config.model and config.git_provider. Configure rules so the job triggers on merge_request_event pipeline sources and handles draft-to-ready transitions automatically.
How do I set up Qodo PR Agent GitHub token authentication?
In GitHub, open Settings > Secrets and variables > Actions and add your API keys. Use the built-in GITHUB_TOKEN secret for repository authentication. For LLM providers, add secrets such as OPENAI_API_KEY or GEMINI_API_KEY. In your workflow YAML, reference these as ${{ secrets.GITHUB_TOKEN }} and similar entries, and ensure the workflow has pull-requests: write permissions. Prefer the built-in token instead of personal access tokens when it covers your PR operations.
What are common Qodo PR Agent troubleshooting steps for model errors?
When you see model configuration errors, first confirm you use dotted notation variables like config.model instead of PR_AGENT.MODEL. Add fallback models with config.fallback_models to avoid single-model failures. For debugging, run the command with –config.output_relevant_configurations=true to inspect active settings. Verify that API keys are present and have the correct permissions. For Azure OpenAI, ensure .secrets.toml includes api_type=”azure”, api_base, and deployment_id. Run python -m tests.health_test.main to validate your LLM provider setup.
Can Qodo PR Agent automatically fix CI failures like Gitar does?
Qodo PR Agent cannot automatically fix CI failures. It analyzes code and offers interactive improvements, but it does not detect CI failures, generate fixes, validate them in your build environment, or commit working solutions. Qodo operates as an interactive code review assistant. As described earlier, Gitar’s healing engine analyzes build logs, proposes contextual fixes, tests them in your CI environment, and commits validated changes that keep builds green.
Conclusion
Qodo PR Agent integration demands careful YAML configuration, Docker setup, and manual application of interactive fixes. This guide gives you the technical steps to run Qodo in your CI/CD pipeline, but the largest productivity gains come from tools that move beyond suggestions to full automation.
Try Gitar’s Team Plan free for 14 days to experience CI healing that fixes failures automatically and keeps builds green. Shift from manual configuration and interactive review tools to a platform that takes ownership of CI stability.