Written by: Ali-Reza Adl-Tabatabai, Founder and CEO, Gitar
Key Takeaways
- Integrate code quality tools like ESLint, SonarQube, and Trivy into CI/CD pipelines at multiple stages for early issue detection.
- Use platform-specific YAML configurations for GitHub Actions, GitLab CI, and Jenkins with fail-fast mechanisms and branch protection.
- Implement security scans including SAST, SCA, and container scanning to address vulnerabilities in AI-generated code.
- Improve pipelines with caching, parallel execution, and concurrency controls to maintain fast feedback loops under 10 minutes.
- Supercharge your pipeline with Gitar.ai for automatic CI failure analysis and fixes that guarantee green builds every time.
Key Steps to Integrate Automated Code Checks into Your CI/CD Pipeline
Use these seven steps to build automated code checks that catch issues before they reach production.
1. Choose Your Code Quality Tools – Select ESLint for JavaScript linting, SonarQube for comprehensive code analysis, and Trivy for security scanning that match your technology stack.
2. Hook Into Pipeline Stages – Integrate checks at multiple stages to catch different issue types at the right time. Use pre-commit hooks for immediate feedback on basic issues before code enters the pipeline. Run build-time scans for deeper analysis that would slow down local development. Add deployment gates that verify all checks before code reaches production.
3. Configure Platform-Specific YAML – Implement workflows for GitHub Actions (.github/workflows/), GitLab CI (.gitlab-ci.yml), or Jenkins (Jenkinsfile) with clear job dependencies and fail-fast behavior so broken changes stop early.
4. Enable Gating and Fail-Fast – Configure branch protection rules to block merges until all checks pass. This protection keeps broken code out of main branches and reduces production incidents.
5. Add Security Scans – Include SAST, SCA, and container scanning to detect vulnerabilities early, addressing the 45% of AI-generated code that contains security vulnerabilities.
6. Implement Reporting and Iteration – Set up dashboards and notifications that surface check results clearly. Review recurring failures, then refine rules, thresholds, and test coverage so your pipeline improves over time.
7. Supercharge with Gitar AI – Deploy intelligent auto-fix capabilities that analyze failures, generate corrections, and commit fixes automatically, which removes most manual intervention from CI troubleshooting.
Industry Tools Comparison for CI/CD Code Quality Checks
Step 1 above highlighted tool selection, and this comparison helps you choose based on depth of analysis, speed, and scalability. Selecting the right tools for your automated code checks requires understanding each platform’s strengths and integration capabilities. The table below shows how ratings and integration styles guide choices for quick setup, broad coverage, or enterprise needs.
|
Tool |
Strengths |
Integration Notes |
|
SonarQube |
Code quality, maintainability, security analysis |
|
|
ESLint/Jest |
JavaScript linting, unit testing |
Fast execution, extensive plugin ecosystem |
|
Snyk/Trivy |
Dependency scanning, container security |
|
|
Checkmarx |
Enterprise SAST, comprehensive coverage |
Post-AI code generation introduces new security risks. Traditional tools catch syntax errors but struggle with the security vulnerabilities prevalent in AI-generated code mentioned earlier. This gap creates demand for intelligent solutions that understand context and automatically remediate issues.
GitHub Actions Example: Linting, Tests and Security Checks in CI/CD
This production-ready GitHub Actions workflow shows how to wire linting, tests, and security scans into a single pipeline.
This configuration follows fail-fast CI/CD best practices by running linting before tests and security scans before deployment. The concurrency settings cancel outdated runs, which reduces wasted compute and noisy failures.
GitLab CI Example: Multi-Language Linting and Code Quality Checks
This GitLab CI configuration demonstrates multi-language linting, testing, and security analysis in a single pipeline.
GitLab’s built-in security scans and multi-project pipelines make it a strong fit for teams that want an all-in-one DevSecOps platform.
Jenkins Example: Automated Code Scans and Testing Pipeline
This Jenkins pipeline uses common plugins and shell steps to run linting, tests, and security scans.
For comprehensive Jenkins configurations, refer to the GitHub Actions and GitLab examples above, which provide more detailed security scanning implementations.
Beyond Checks: Use Gitar AI for Automatic CI Fixes
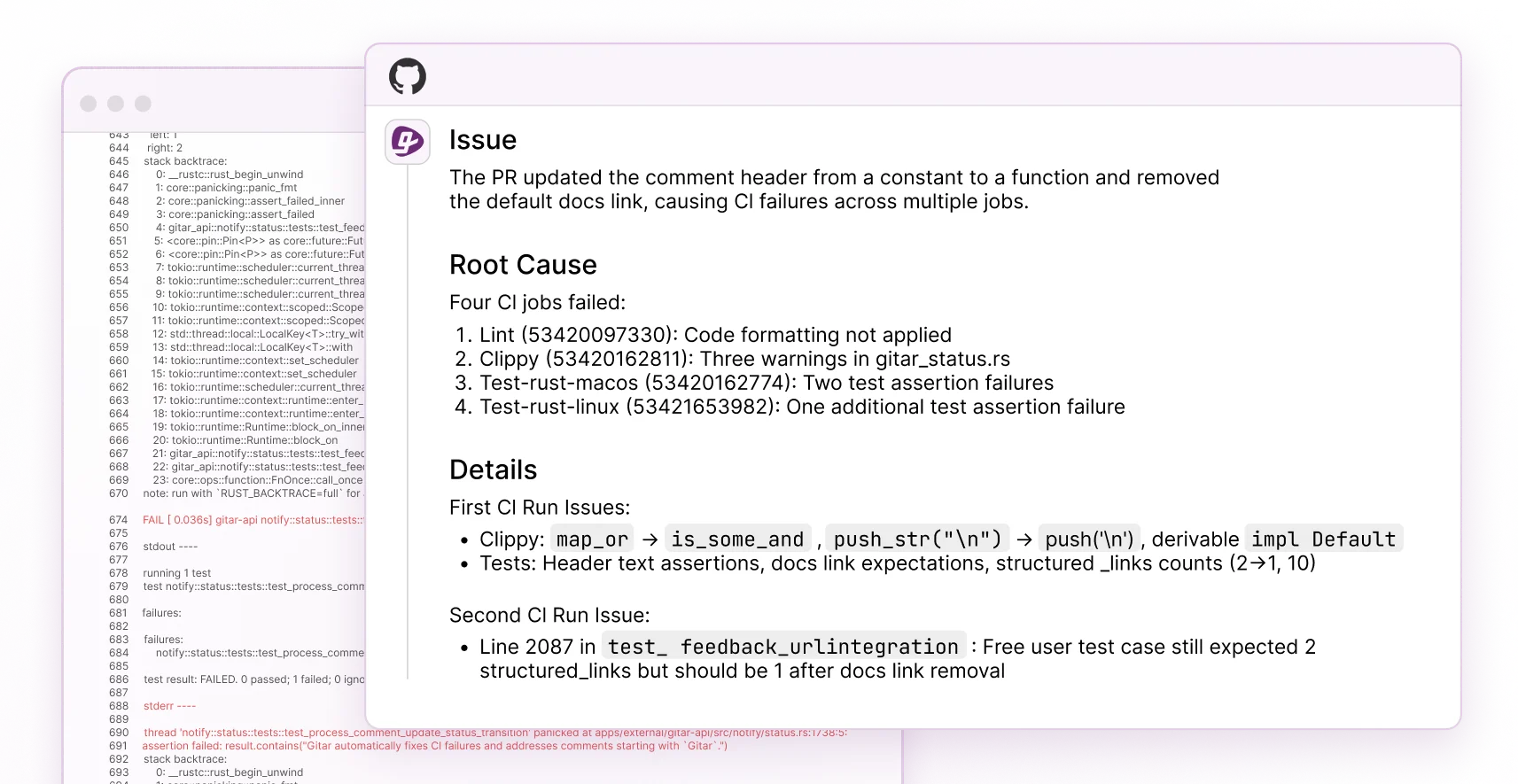
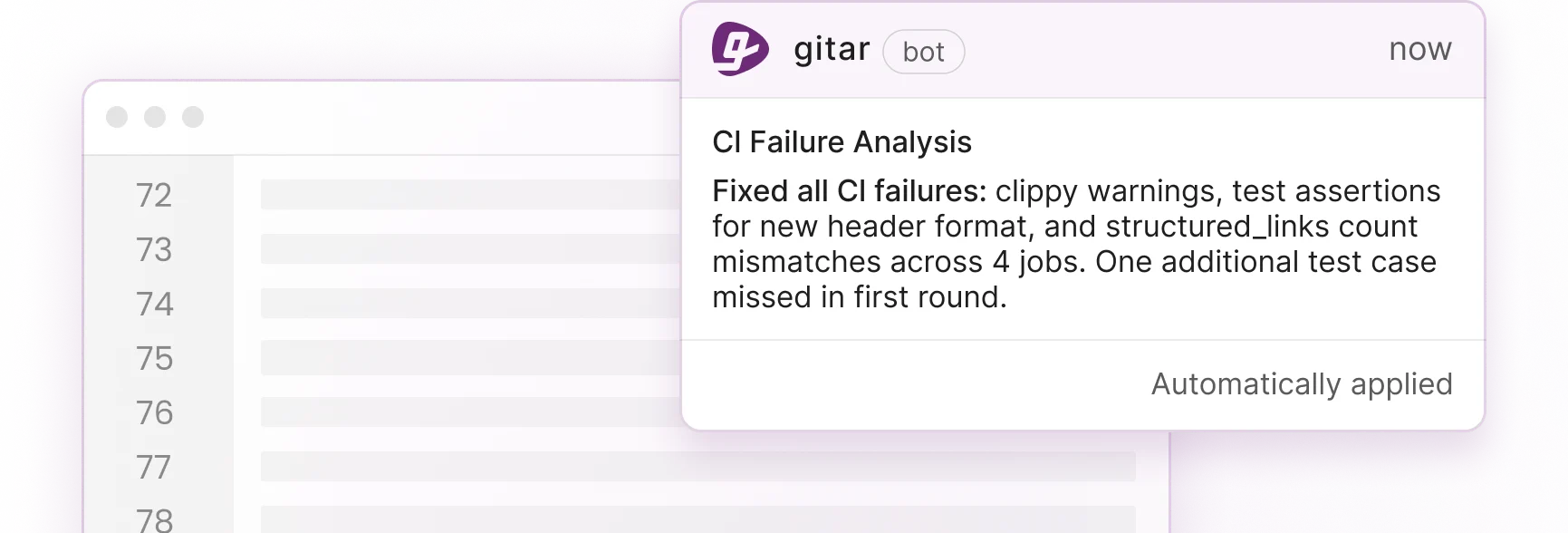
The GitHub Actions, GitLab CI, and Jenkins examples above show how to detect issues, but detection alone still requires manual fixes. While traditional tools identify problems, Gitar heals them. Gitar’s CI failure analysis automatically analyzes failures and provides insights in the dashboard comment, updating dynamically with new commits. See the Gitar documentation for details.
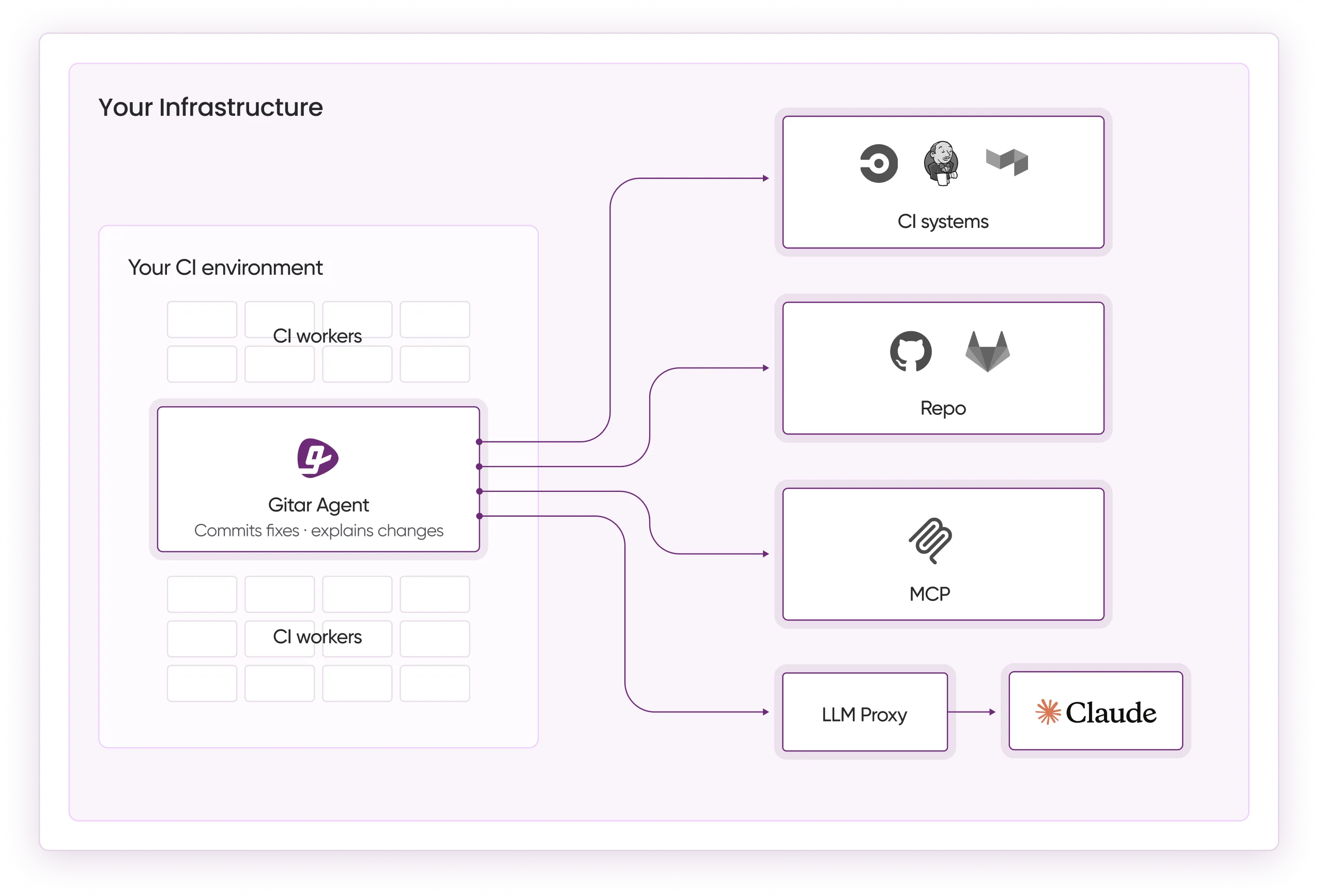
Gitar integrates with your existing CI/CD infrastructure as a GitHub App or GitLab integration that monitors your workflows and reacts to failures.
Traditional code review tools identify issues but leave developers to fix them manually, which creates context switching and delays. Gitar removes this friction through four capabilities that competitors lack.
|
Feature |
CodeRabbit/Greptile |
Gitar |
|
Auto-fix CI failures |
No |
Yes |
|
Validate fixes against CI |
No |
Yes |
|
Guarantee green builds |
No |
Yes |
|
Single clean comment |
No |
Yes |
Gitar’s CI Failure Analysis deduplicates failures across multiple jobs, providing clear root cause analysis without overwhelming noise. The intelligence layer maintains full context from PR creation to merge, which enables automated fixes that understand your codebase.
Teams report significant productivity gains. Tigris noted Gitar’s summaries are “more concise than Greptile/Bugbot,” and Collate’s engineering lead highlighted the “unrelated PR failure detection” saving “significant time.”
Start your 14-day free trial to experience automated CI fixes that eliminate manual intervention.
Fix Flaky Checks and Ensure Reliable Deployments
Common pitfalls in automated code checks include flaky tests, resource constraints, and configuration drift, and all three erode trust in your pipeline. When tests fail randomly, consume excessive resources, or behave differently across environments, developers start ignoring CI results. Address these issues with proven strategies.
Flaky Test Management: Use matrix strategy to parallelize tests and implement caching for dependencies. Isolate tests with mocks and in-memory databases so external services do not introduce randomness.
Resource Optimization: Implement concurrency controls and parallel job execution to reduce pipeline duration. These improvements should bring total pipeline time below the critical 10-minute threshold, where slower feedback causes context switching and lost focus.
Security Tool Configuration: Avoid alert fatigue by configuring tools to block only critical and high-severity findings while tracking lower-priority issues in separate reports.
Environment Consistency: Use Infrastructure as Code (IaC) and containerization so development, staging, and production environments stay synchronized.
ROI of Automated Code Checks in CI/CD with Gitar
The financial impact of implementing comprehensive automated code checks with intelligent auto-fix capabilities becomes clear when you account for context switching. For a 20-developer team spending 1 hour daily on CI failures and code review issues, cutting 75% of that overhead produces measurable savings.
|
Metric |
Before Automation |
After Gitar Integration |
|
Annual productivity cost (20 devs) |
$250K |
|
|
Time on CI/review issues |
1 hour/day/developer |
15 minutes/day/developer |
|
Context switching interrupts |
Multiple per day |
Near-zero |
|
Build failure resolution time |
30-60 minutes |
Automatic |
FAQ
What is the best way to add linting to GitHub Actions?
Create a .github/workflows/lint.yml file that runs on pull requests and push events. Use actions/setup-node with caching, run npm ci for consistent dependencies, then execute linting commands like npm run lint and npx prettier –check. Configure the job to run before tests with the needs keyword so your pipeline fails fast.
How does Gitar integrate with my existing CI/CD pipeline?
Gitar installs as a GitHub App or GitLab integration that monitors your existing workflows. When CI failures occur, Gitar analyzes the logs, generates fixes with full codebase context, validates the solutions, and commits them to your PR. You keep your current YAML configurations, and Gitar works alongside your existing tools.
Can Gitar handle complex multi-language pipelines?
Gitar supports Python, JavaScript, TypeScript, Go, Java, Rust, and more. The AI agent emulates your environment, including SDK versions, multi-dependency builds, and third-party scans. For enterprise deployments, Gitar runs inside your own CI with access to secrets and caches so fixes match your production environment.
How do I prevent automated code checks from slowing down my pipeline?
Run independent checks like linting, testing, and security scans in parallel. Use caching for dependencies and build artifacts. Configure incremental analysis that scans only changed files on pull requests while full scans run on schedules. Set thresholds that block only critical issues while tracking lower-priority findings separately.
What security scanning tools should I integrate first?
Start with Static Application Security Testing (SAST) tools like SonarQube for code analysis, Software Composition Analysis (SCA) tools like Snyk for dependency scanning, and secret detection tools like GitGuardian. Add container scanning with Trivy if you use Docker. Run these tools in parallel and focus on critical and high-severity findings to avoid alert fatigue.
Conclusion: Integrate Automated Code Checks into CI/CD with Gitar
Automated code checks in your CI/CD pipeline protect code quality in the AI-driven development era. Traditional tools detect problems, but intelligent automation delivers the real shift by fixing issues as they appear.
The seven-step approach in this guide, from tool selection through Gitar AI integration, gives you a practical framework for resilient, self-healing pipelines. With fail-fast mechanisms, parallel execution, and smart caching, you catch issues early while keeping delivery speed high.
Start your 14-day free trial in 30 seconds and watch Gitar automatically fix your next CI failure.
