Written by: Ali-Reza Adl-Tabatabai, Founder and CEO, Gitar
Key Takeaways
- AI code generation has increased PR review times by 91%, so automated Kubernetes YAML validation now matters for every fast-moving team.
- Gitar leads as the top free AI tool with auto-fix capabilities that commit validated solutions directly to PRs, unlike suggestion-only alternatives.
- Tools like Datree, KubeLinter, and Checkov excel in policy enforcement and security scanning, but still require manual fix implementation.
- Setup times range from 30 seconds with Gitar to 15 minutes with some scanners, and Gitar offers the fastest native CI integrations across GitHub, GitLab, and more.
- Experience automated Kubernetes YAML fixes that guarantee green builds and start your free Gitar trial today.
AI code generation now ships more Kubernetes changes than most teams can safely review by hand. PR queues grow, CI fails more often, and manual YAML validation cannot keep up with 2026 deployment velocity. Automated AI review tools have become a practical requirement, not a nice-to-have. This guide walks through seven free options and shows which tools actually help you ship reliable Kubernetes manifests faster.
1. Gitar (Top Pick: AI That Fixes K8s YAML)
How Gitar Handles Broken Kubernetes Manifests
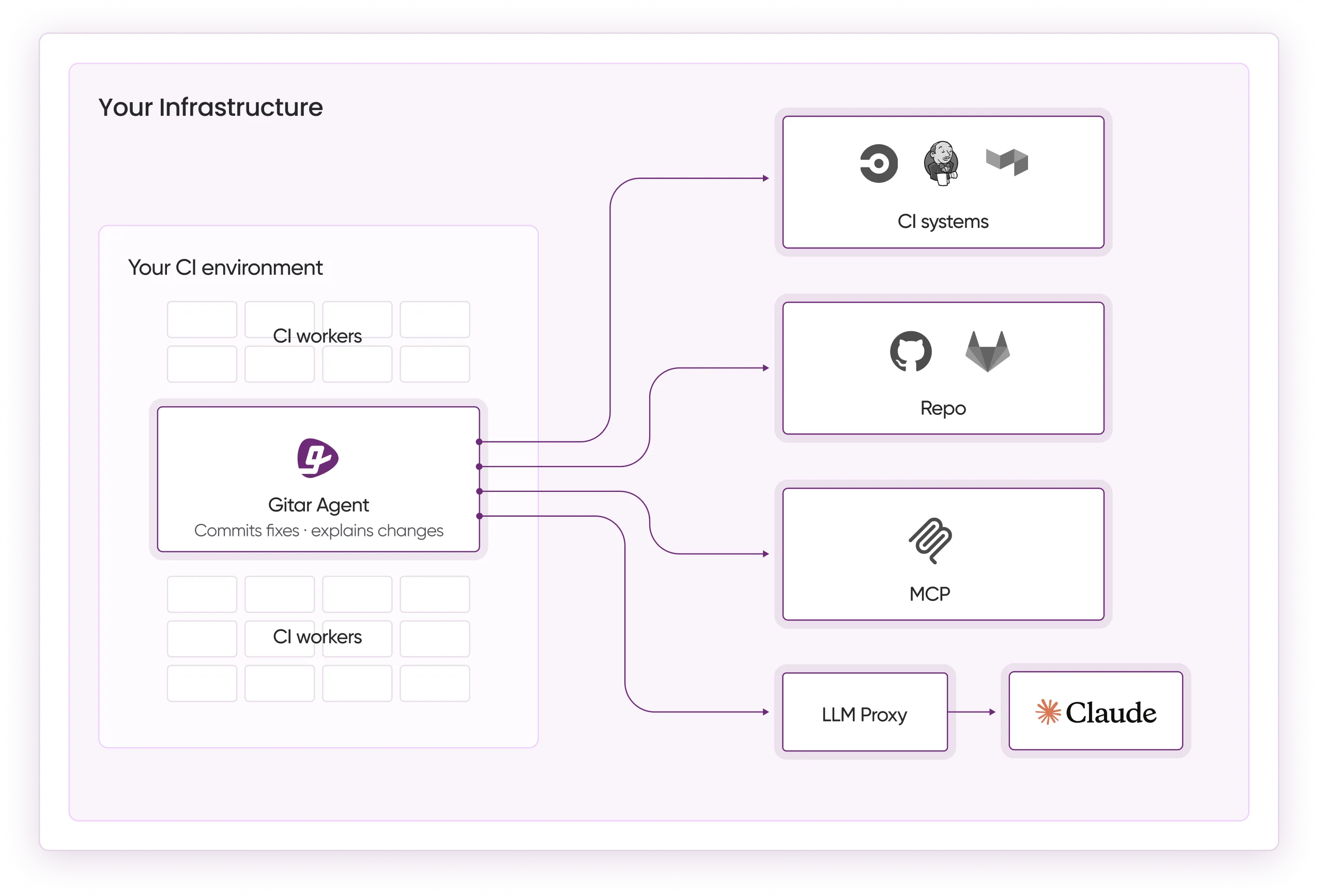
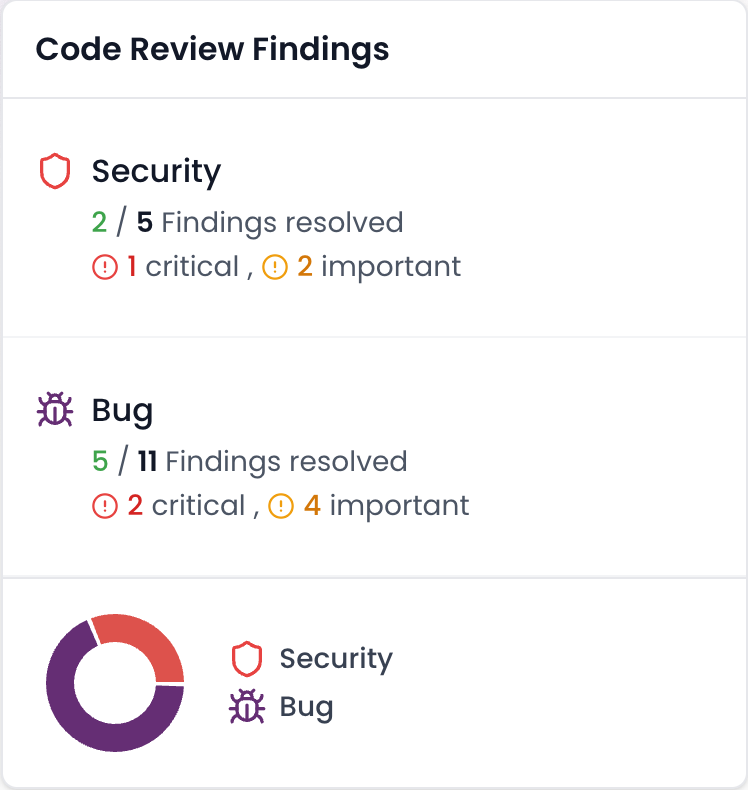
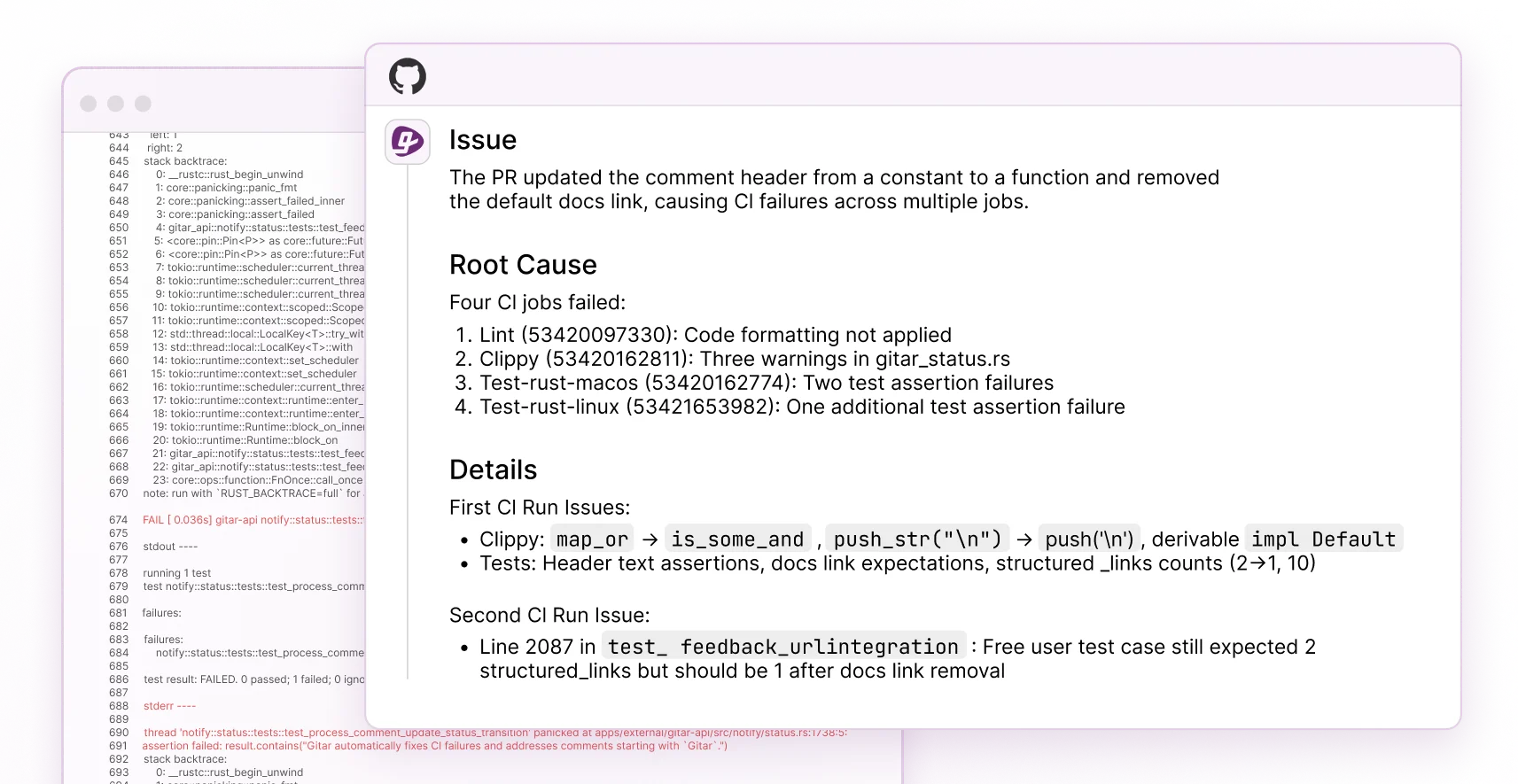
Gitar stands apart as the AI code review platform that actually fixes code issues automatically. When CI fails, Gitar analyzes the failure logs, generates the correct fix with full repository context, validates the solution, and commits it directly to your PR. This healing engine approach removes the manual work required by suggestion-only tools and shortens the path from red builds to green builds.
The following table breaks down Gitar’s core capabilities that enable this end-to-end automation:
|
Feature |
Capability |
Description |
|
Auto-Fix |
Full automation |
Commits validated fixes directly to PRs |
|
CI Integration |
Native support |
GitHub Actions, GitLab CI, CircleCI, Buildkite |
|
Code Coverage |
Comprehensive |
Security, bugs, performance, best practices |
|
Natural Language Rules |
Custom policies |
Define workflows without complex YAML |
Gitar Setup in Under a Minute
Installation takes under 60 seconds. Install the Gitar GitHub App from the marketplace, enable the 14-day Team Plan trial, and push a PR with Kubernetes YAML. Gitar analyzes any CI failures and posts a single dashboard comment with findings and fixes. GitLab users follow a similar flow through the GitLab marketplace, with the same automatic analysis once CI runs.
What Our Gitar Tests Showed
We tested Gitar with a sample PR that failed CI. Within 60 seconds of the CI failure, Gitar posted a comprehensive analysis, automatically generated a fix, and committed the solution. The updated code passed all subsequent CI checks, which demonstrated Gitar’s healing engine capabilities in a realistic workflow.
Gitar Pros and Ideal Teams
Pros: The unlimited 14-day trial includes full Team Plan features, so you can exercise every capability before paying. This trial covers native support for all major CI platforms, which enables repository-wide context analysis for accurate fixes. Gitar posts a single clean dashboard comment instead of cluttering PRs with many bot messages, which keeps review noise low. Every fix is validated against your actual CI environment before Gitar commits it, so you only merge working solutions.
Ideal for: Teams experiencing high PR volumes from AI code generation, DevOps engineers managing complex Kubernetes deployments, and organizations that need fast feedback loops without manual intervention.
2. Datree (Policy-as-Code Validation)
How Datree Enforces Kubernetes Policies
Datree provides policy-as-code validation for Kubernetes YAML with a focus on preventing misconfigurations before deployment. The platform offers pre-built policies for security and best practices, and teams can create custom rules that match internal standards. Datree suggests fixes and explains violations but does not implement changes automatically.
Datree Setup and CI Integration
Install the Datree CLI via npm or download the binary. Configure policies through the web dashboard, then integrate Datree into CI by adding the datree test command to your pipeline. Setup includes creating an account and configuring policy tokens for authentication so CI runs can report results correctly.
Datree Results in Practice
Datree successfully identified missing resource limits and security context issues in our test Deployment. The tool provided detailed explanations and suggestions that helped developers understand each violation. Policy violations appeared with clear severity levels, which made it easier to prioritize fixes, although every change still required manual implementation.
Pros: Comprehensive policy library, clear violation explanations, and solid CI integration documentation.
Cons: Suggestion-only approach, manual fix implementation, and limited free tier features for larger teams.
Ideal for: Teams that want policy enforcement without auto-fixes and organizations with strict change control processes that prefer humans to apply every change.
3. Workik AI (Context-Aware Analysis)
How Workik AI Uses Project Context
Workik AI offers context-aware Kubernetes YAML analysis with integration into popular IDEs. The platform understands repository structure and provides intelligent suggestions based on existing patterns in your codebase. The free tier includes basic validation and suggestions that help individual developers catch issues early.
Workik AI Setup in IDEs and CI
Sign up for a Workik account and install the IDE extension or use the web interface. Connect your repository for context analysis, then configure the Kubernetes YAML review settings. CI integration requires webhook configuration, which adds some complexity compared with tools that provide native CI apps.
Workik AI in Real-World Testing
Workik identified several issues in our test manifests, including improper label usage and missing annotations. The suggestions matched the project’s existing patterns, which made them easier to accept. Some debugging and refactoring features offered automated improvements, although Kubernetes YAML fixes still relied mainly on suggestions.
Pros: Strong IDE integration, context-aware suggestions, and good understanding of project patterns.
Cons: Limited free tier and higher setup complexity for CI integration.
Ideal for: Individual developers working in IDEs and small teams with simple validation needs that value in-editor feedback.
If Workik’s suggestion-only approach does not match your workflow, try Gitar’s 14-day free trial for automated fixes that commit working solutions directly to your PRs.
4. K8sGPT (AI-Powered Diagnostics)
How K8sGPT Explains Kubernetes Errors
K8sGPT combines Kubernetes expertise with AI to analyze cluster issues and YAML configurations. The tool excels at diagnosing problems in running clusters and also supports static YAML analysis. It works especially well when you need clear explanations for complex error messages.
K8sGPT Setup and AI Provider Configuration
Install K8sGPT via package managers or download the binary. Configure an AI provider such as OpenAI, Azure OpenAI, or supported local models, then authenticate. For YAML analysis, run the analyze command with manifest files and review the AI-generated explanations.
What K8sGPT Found in Testing
K8sGPT provided excellent explanations of YAML issues, especially around networking and RBAC configurations. The AI-generated responses were detailed and educational, which helped less experienced engineers understand root causes. Auto-remediation options exist for some scenarios, although the tool focuses more on diagnostics than on preventive checks.
Pros: High-quality error explanations, support for multiple AI providers, and strong learning value. Cons: Requires AI provider setup and works primarily as a diagnostic tool rather than a preventive gate.
Ideal for: DevOps engineers learning Kubernetes, teams that need detailed error explanations, and groups troubleshooting complex configurations.
5. KubeLinter (Fast Static Analysis)
How KubeLinter Secures Kubernetes YAML
KubeLinter integrates with CI/CD pipelines for automated security checks on Kubernetes YAML files and Helm charts. The tool focuses on security misconfigurations and DevOps best practices with fast execution times suitable for pull request checks.
KubeLinter Setup for CI Pipelines
Download the KubeLinter binary or use the Docker image. KubeLinter offers easy CI/CD integration with minimal configuration required. Add the lint command to your CI pipeline with the path to your YAML files and review the reported findings.
KubeLinter Test Findings
KubeLinter quickly identified security issues including missing security contexts and dangerous capabilities. The tool provided clear, actionable feedback with specific line numbers and explanations that guided manual fixes. Every remediation step still required a developer to change the manifests.
Pros: Fast execution, comprehensive security checks, minimal setup complexity, and strong CI integration.
Cons: No auto-fix capability, focus on security and best practices only, and suggestion-only output.
Ideal for: Security-focused teams, organizations that need fast PR feedback, and teams with existing manual fix workflows.
6. kubeconform (Schema Validation)
How kubeconform Validates Kubernetes Schemas
kubeconform validates Kubernetes manifests against schemas, supporting specific Kubernetes versions and recursive directory validation. The tool excels at catching schema violations and API version mismatches before deployment.
kubeconform Setup and CI Usage
Install kubeconform via package managers or download the binary. The tool requires no configuration for basic usage, which keeps onboarding simple. Integrate it into CI by adding the validation command to your pipeline with flags that match your Kubernetes version.
kubeconform in Hands-On Tests
kubeconform successfully caught API version mismatches and schema violations in our test manifests. The tool produced detailed JSON output suitable for automated processing and reporting. It did not provide fix suggestions or auto-remediation, so developers still had to interpret and correct each issue.
Pros: Accurate schema validation, support for multiple Kubernetes versions, fast execution, and no configuration required for basic checks.
Cons: Schema validation focus only, no security or best practice checks, and no fix suggestions.
Ideal for: Teams focused on schema compliance, GitOps workflows that require validation, and projects with basic CI integration needs.
7. Checkov (Infrastructure Security Scanning)
How Checkov Scans Kubernetes and IaC
Checkov is an open-source IaC scanning tool that supports Kubernetes YAML/Helm manifests, detecting misconfigurations and security issues. The tool enforces policy and compliance frameworks like CIS and integrates into CI/CD pipelines across many platforms.
Checkov Setup and Policy Configuration
Install Checkov via pip or use the Docker image. The tool works out of the box with default policies that cover common security risks. Configure custom policies using YAML or Python, then integrate Checkov into CI by adding the scan command to your pipeline.
Checkov Security Results in Testing
Checkov identified multiple security issues including missing network policies and insecure configurations. The tool produced detailed policy violation reports with remediation guidance and auto-fix capabilities through specific integrations. Teams still need to tune policies to reduce noise and focus on the most relevant findings.
Pros: Comprehensive security scanning, support for multiple IaC formats, extensive policy library, and strong CI integration.
Cons: Can generate many findings, and requires policy tuning for practical day-to-day use.
Ideal for: Security teams that require broad scanning, compliance-focused organizations, and teams comfortable with policy management.
Side-by-Side: Free AI K8s YAML Review Tools Comparison Table
The table below highlights the key differences between these tools. Only Gitar offers auto-fix capabilities in its free trial, while all other tools rely on manual implementation of suggestions. Setup time and coverage depth also vary significantly, so this comparison helps you choose the tool that fits your workflow and risk profile.
|
Tool |
Free Tier Depth |
Auto-Fix |
K8s Coverage |
Setup Time |
|
Gitar |
14-day full Team Plan |
Yes |
Full code review |
30 seconds |
|
Datree |
Limited policies |
No |
Policy-based validation |
5 minutes |
|
Workik AI |
Basic validation |
No |
Context-aware suggestions |
10 minutes |
|
K8sGPT |
Full diagnostic features |
No |
Cluster + YAML analysis |
15 minutes |
|
KubeLinter |
Full security scanning |
No |
Security + best practices |
2 minutes |
|
kubeconform |
Full schema validation |
No |
Schema compliance only |
1 minute |
|
Checkov |
Full security scanning |
No |
Security + compliance |
5 minutes |
Based on Gitar documentation and comprehensive testing, Gitar leads in automation depth and practical value for teams managing high PR volumes.
Key Considerations and Gaps in Free AI K8s YAML Reviewers
Most free AI Kubernetes YAML review tools follow the suggestion-only model, which leaves developers to manually implement fixes and hope they work. This approach creates a false economy, because teams save on tool costs but lose productivity to repeated remediation cycles. Community feedback consistently highlights this frustration and calls for cluster-less validation with auto-fix capabilities that actually guarantee green builds.
The 2026 reality favors auto-fix for teams that care about velocity. Validation tools catch issues and improve visibility, but only healing engines like Gitar remove the manual toil that slows modern development workflows.
Start your free Gitar trial and experience the difference between suggestions and solutions.
Frequently Asked Questions
Best Free AI Tool for Kubernetes YAML Security Reviews
Gitar’s 14-day Team Plan trial offers comprehensive AI code review with automatic fixes for code issues. Unlike suggestion-only tools, Gitar validates fixes against your actual CI environment and commits working solutions directly to your PRs.
Automatic Kubernetes YAML Fixes in CI with Gitar
Gitar integrates natively with GitHub Actions, GitLab CI, CircleCI, and Buildkite to analyze CI failures, generate fixes, and commit solutions. When your code fails validation or deployment, Gitar’s healing engine resolves the issue without manual intervention and keeps your builds green.
Difference Between Free Tools and Gitar’s Trial
Free tools typically provide suggestions that require manual implementation and do not guarantee that fixes will work. Gitar’s 14-day Team Plan trial includes full auto-fix capabilities, repository-wide context analysis, and validation against your actual CI environment. You get a complete healing engine that removes manual toil and delivers working solutions.
Reddit Opinions on Free AI Kubernetes YAML Tools
Reddit discussions often mention KubeLinter and Checkov for security scanning, since both tools cover many common risks. The community increasingly recognizes that suggestion-only tools do not solve the core problem of manual fix implementation. Gitar addresses this gap by providing actual fixes rather than just identifying issues, which makes it a practical choice for teams managing high PR volumes.
Cluster Requirements for Testing These AI Review Tools
You do not need a Kubernetes cluster to test the tools in this comparison. Gitar, KubeLinter, Checkov, and the other options can validate manifests, detect security issues, and check best practices using only the YAML files in your repository. This cluster-less approach enables fast feedback in CI/CD pipelines before deployment.
Conclusion: Choose the Right Free AI Code Review for Kubernetes YAML
The current landscape of free AI code review for Kubernetes YAML manifests spans basic schema validation, policy enforcement, diagnostics, and security scanning. Only Gitar bridges the gap between identifying problems and resolving them with a healing engine that fixes issues automatically.
Tools like KubeLinter, Checkov, and kubeconform excel at finding problems, yet they still leave you with the manual work of implementing fixes. In 2026’s high-velocity development environment, suggestion-only tools slow teams down instead of unblocking delivery.
