Written by: Ali-Reza Adl-Tabatabai, Founder and CEO, Gitar
Key Takeaways for Qodo PR-Agent in CircleCI
- CircleCI pipelines using Qodo PR-Agent often fail because of authentication errors, token limits, webhook issues, and large PR timeouts that demand manual configuration.
- Fix authentication by adding masked OPENAI_KEY and GITHUB_TOKEN environment variables in CircleCI, and grant the token repository and pull request write permissions.
- Handle large PRs and token limits by updating .pr_agent.toml with max_model_tokens, fallback models, and enable_large_pr_handling set to true.
- Troubleshoot webhooks by confirming GitHub App permissions, matching secrets, and successful delivery in GitHub and CircleCI logs.
- Replace this configuration overhead with Gitar, which manages CircleCI failures automatically and keeps builds green without extra setup.
The Problem: Qodo PR-Agent CircleCI Failures Drain Engineering Time
Engineering teams spend hours debugging Qodo PR-Agent integration issues that block green builds. Recent GitHub issue #2292 shows litellm.AuthenticationError problems with Anthropic models, while issue #2287 reveals authentication overrides breaking provider-specific configurations. Issue #2238 demonstrates AttributeError failures when handling large PRs.
60% of projects experience delays from CI pipeline failures, and manual troubleshooting consumes developer time that could ship features. The root cause is configuration sprawl across GitHub tokens, OpenAI keys, webhook signatures, and TOML files, which creates many fragile integration points.
Authentication issues usually appear first, because Qodo cannot reach the AI or GitHub APIs without correct keys and permissions.
Qodo PR-Agent CircleCI Authentication Errors
Authentication failures appear as 401 errors or litellm.AuthenticationError messages in CircleCI logs. Missing or misconfigured API keys and insufficient GitHub token permissions cause most of these problems.
Use this sequence to resolve authentication issues:
- Open your CircleCI project settings and select Environment Variables.
- Add these masked environment variables.
OPENAI_KEY=your_openai_api_key_here GITHUB_TOKEN=your_github_token_with_repo_and_pull_requests_write_permissions
- Confirm that your GitHub token includes repository and pull_requests write permissions.
- Check CircleCI job logs and confirm successful authentication before continuing.
Gitar removes this authentication work by managing API access internally, so you avoid handling keys, tokens, or environment variables for CI failure resolution.
Once authentication works reliably, the next common failure appears when Qodo processes large pull requests.
Fix Qodo PR-Agent Token Limits in Large PRs
Large pull requests can exceed model context windows, which causes timeouts and AttributeError failures. GitHub issue #2238 shows DynaBox attribute errors when teams attempt large PR handling configurations.
Configure token limits in your .pr_agent.toml file to keep large reviews stable.
[config] max_model_tokens = 128000 enable_large_pr_handling = true [openai] fallback_models = [“gpt-4”, “gpt-3.5-turbo”] [anthropic] fallback_models = [“claude-3-sonnet”, “claude-3-haiku”]
Trigger /review on a large PR and watch for timeout or AttributeError messages in the logs to confirm the fix. Gitar’s context management handles PRs of any size and avoids manual token limits or fallback model tuning.
After token and context settings, configuration shifts to the core .pr_agent.toml file and CircleCI job definition.
Configure .pr_agent.toml and CircleCI Jobs for Qodo
Model fallbacks and network resilience depend on a TOML configuration that matches your CircleCI environment. Place a .pr_agent.toml file in your repository root with a clear model and GitHub setup.
[config] model = “gpt-4” model_turbo = “gpt-3.5-turbo” fallback_models = [“gpt-4”, “gpt-3.5-turbo”, “claude-3-sonnet”] [github] deployment_type = “app”
Update your CircleCI config.yml so jobs run the pr-agent image consistently.
version: 2.1 jobs: pr-agent-review: docker: – image: codiumai/pr-agent:latest steps: – checkout – run: name: Run PR Agent command: python -m pr_agent.cli –pr_url=$CIRCLE_PULL_REQUEST
Gitar connects to existing CircleCI pipelines without TOML files or YAML edits, which removes this entire configuration layer.
With core configuration in place, the next frequent source of failures involves webhooks and permissions between GitHub and CircleCI.
Troubleshoot Qodo PR-Agent Webhooks and Permissions
GitHub discussion #2079 reports webhook skipping on pull request synchronize events, which shows “Skipping action: synchronize” messages and prevents reviews from triggering.
Use this checklist to verify webhook configuration.
- Confirm that GitHub App permissions include webhooks, pull requests, and repository access.
- Validate webhook signatures in your CircleCI environment variables.
- Test webhook delivery in GitHub repository settings under Webhooks.
GITHUB_WEBHOOK_SECRET=your_webhook_secret_here PR_AGENT_WEBHOOK_SECRET=matching_secret_in_pr_agent_config
Monitor CircleCI logs for confirmation that webhooks arrive and payloads process successfully.
Qodo PR-Agent CircleCI Logs: Common Errors and Fixes
The table below links the most frequent CircleCI errors to their symptoms, root causes, and direct fixes, so you can scan logs and act quickly.
|
Error |
Symptoms |
Cause |
Fix |
|
litellm.AuthenticationError |
401 responses, no PR comments |
Missing OPENAI_KEY |
Add masked environment variable |
|
AttributeError: DynaBox |
Large PR timeouts |
Invalid large PR config |
Update .pr_agent.toml syntax |
|
Webhook signature invalid |
Events not processing |
Secret mismatch |
Sync GitHub and CircleCI secrets |
|
Token rate limit exceeded |
API quota errors |
High usage volume |
Implement fallback models |
Gitar handles these failure patterns automatically, so you avoid manual error triage and log analysis.
Qodo vs. Gitar: CircleCI Workflow Tradeoffs
The comparison below highlights how Gitar removes the configuration and maintenance overhead that makes Qodo PR-Agent difficult to run reliably at scale.
|
Feature |
Qodo PR-Agent |
Gitar |
Benefit |
|
Configuration |
Manual TOML/YAML setup |
Zero-config integration |
75% less setup time |
|
CI Failure Handling |
No CI context |
Auto-healing with validation |
Guaranteed green builds |
|
Authentication |
Multiple API keys required |
No tokens needed |
Eliminates auth errors |
|
Large PR Support |
Manual token limits |
Automatic context handling |
No timeout configuration |
91% of developers now use AI tools, which drives a surge in pull requests and makes manual configuration approaches hard to sustain.
Best Practices for Stable Qodo PR-Agent in CircleCI
Stable Qodo PR-Agent operation depends on a simple maintenance routine that covers updates, monitoring, and validation.
First, keep your foundation current by updating the pr-agent Docker image regularly and validating GitHub App permissions at least once a quarter. These steps prevent many silent failures.
Next, monitor CircleCI logs for authentication problems and webhook delivery issues before they block releases. Early detection reduces time spent on emergency debugging.
Finally, test /review triggers manually after configuration changes, and configure fallback models to absorb API rate limits during peak usage.
Teams that prefer to avoid this maintenance work can rely on Gitar’s autonomous CI healing, which manages these concerns as part of its service.
Why Gitar Removes Qodo’s CircleCI Pain Points
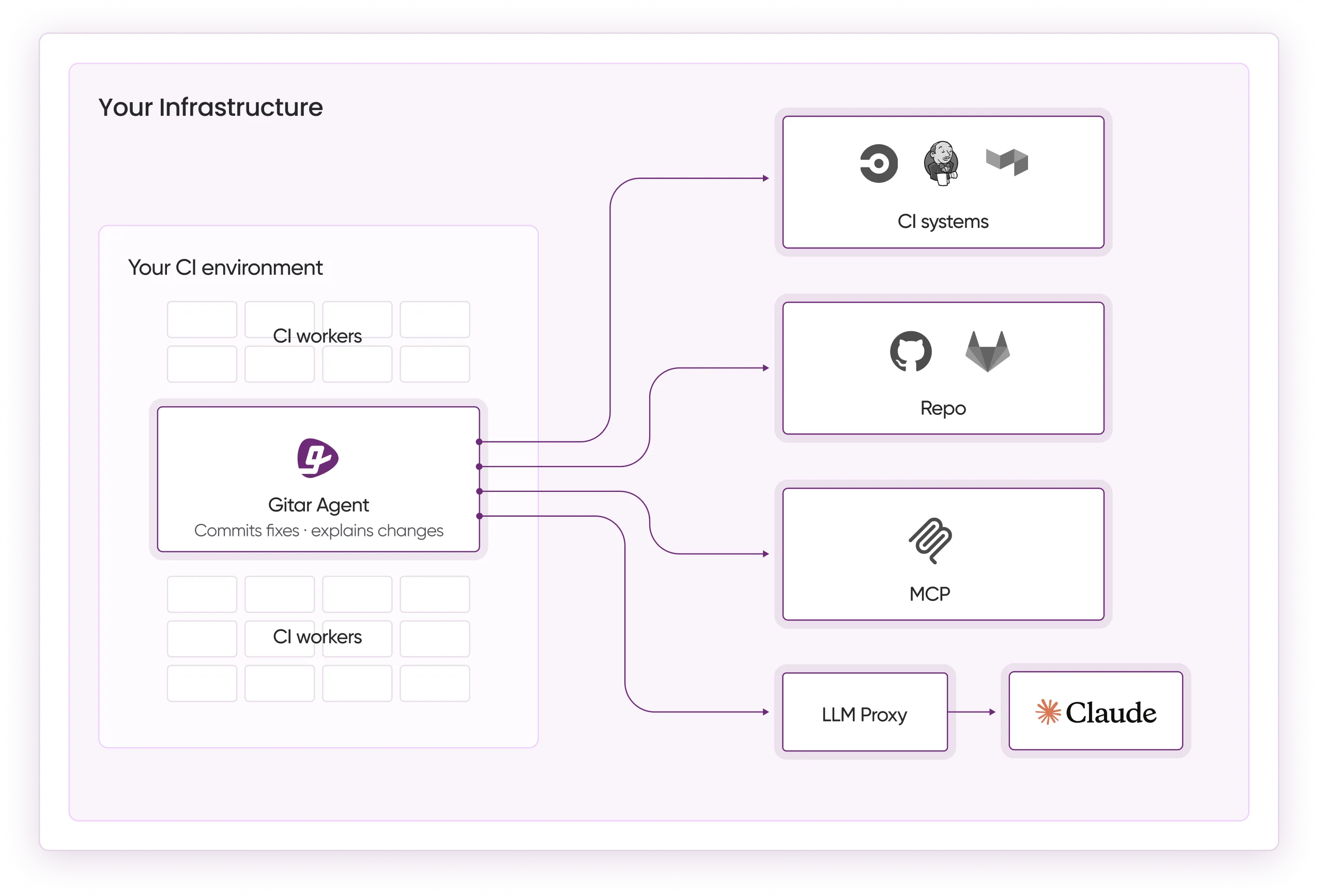
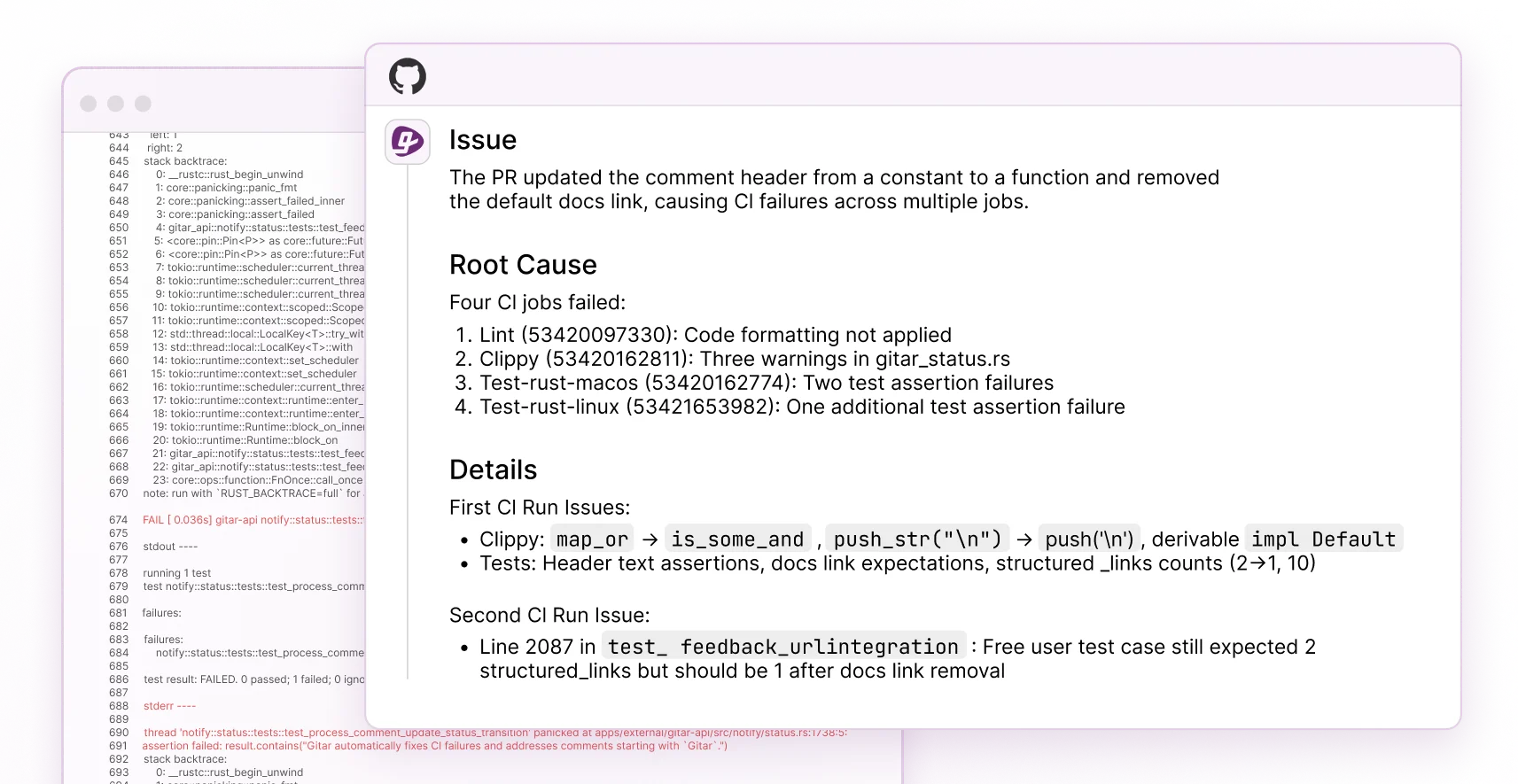
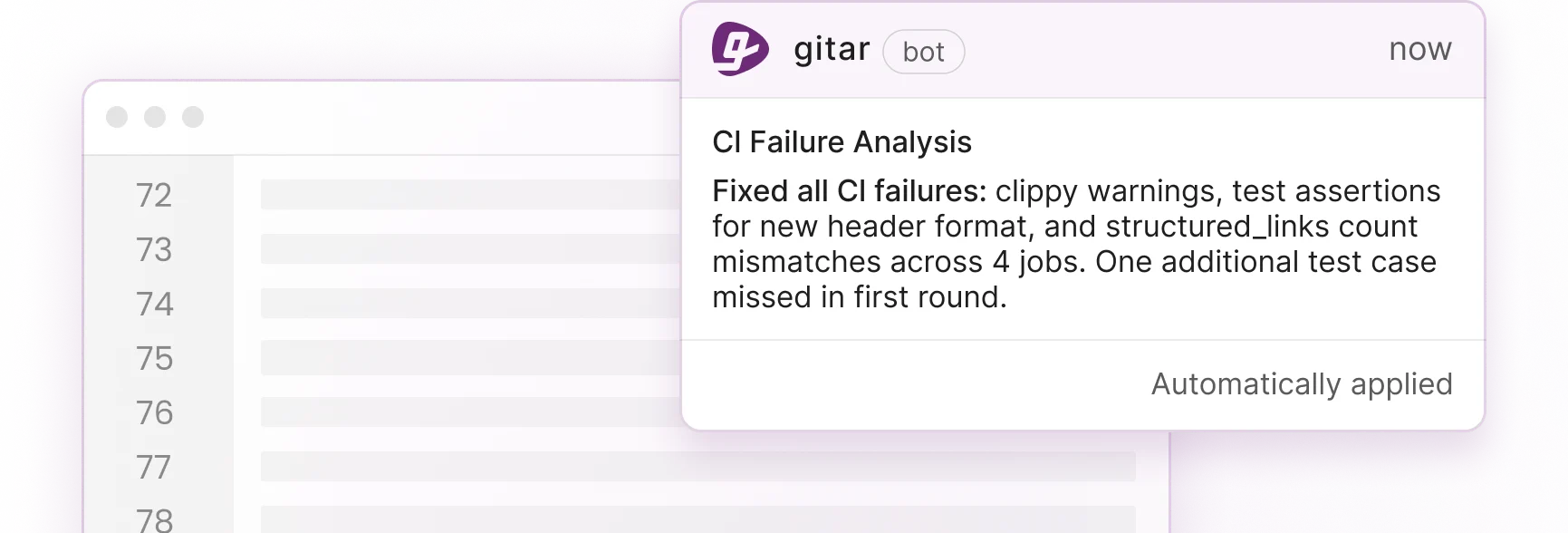
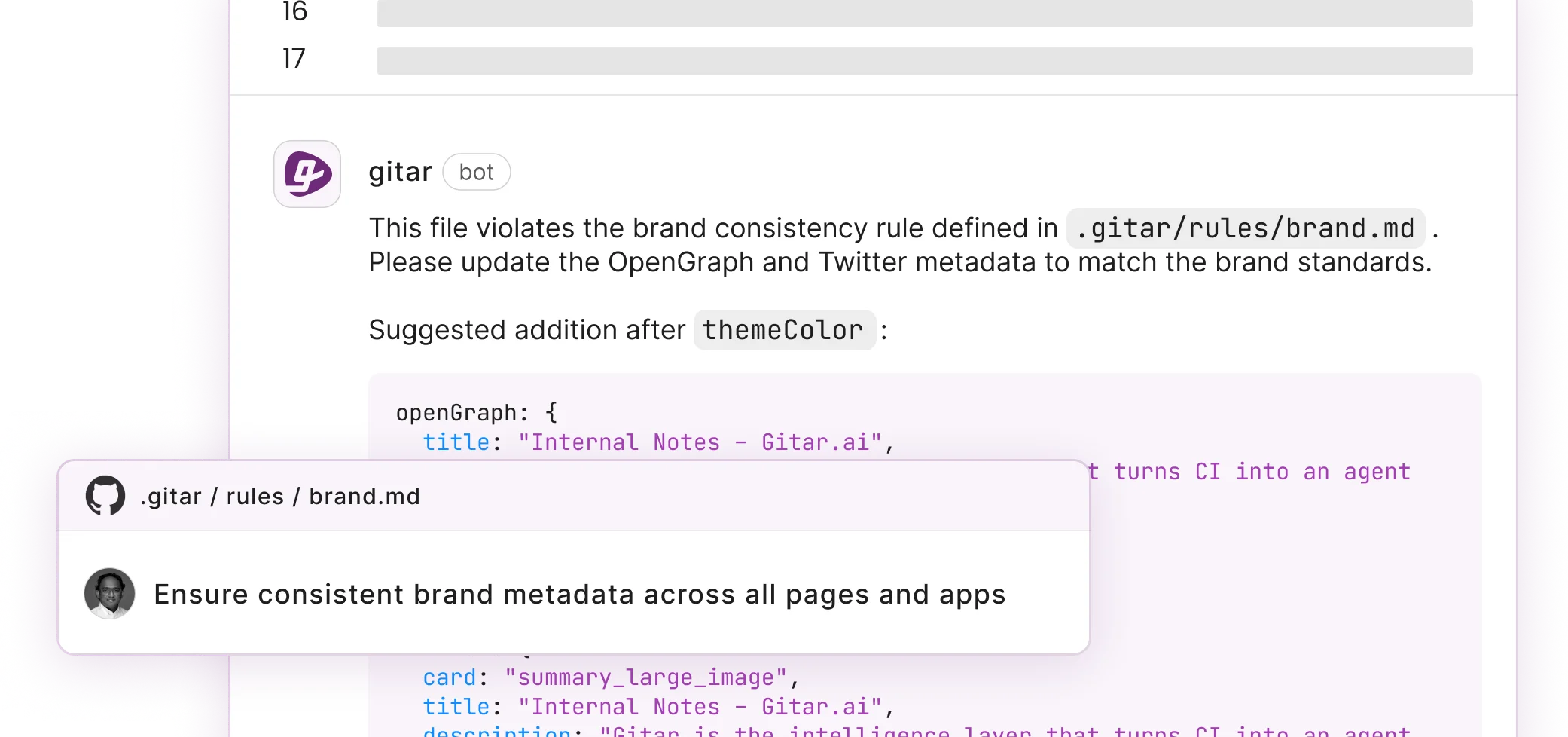
Gitar’s Healing Engine provides CircleCI integration that analyzes failures, generates validated fixes, and commits them without manual intervention. Gitar added CI failure analysis on October 2, 2025[Gitar Docs], and the system now updates a dashboard comment as new commits land.
This zero-configuration approach appears in several ways. Instead of writing complex YAML files, you define repository rules in natural language and Gitar interprets them. That simplicity extends to integrations, because Jira and Slack connect automatically and provide cross-platform context without webhook setup.
Security-focused teams deploy Gitar’s enterprise CI agent inside their own infrastructure, which keeps credentials local and avoids exposure to external services. All findings and fixes appear in a single dashboard comment that replaces scattered notifications across tools.
Teams report that “Gitar fixed CircleCI flakes we chased for hours, and the auto-commit feature resolved lint errors before we even saw the failure notification.” Gitar’s CI agent maintains full context from pull request creation to merge, working continuously to keep CI green and uncover root causes.
Start shipping higher quality software faster with Gitar’s 14-day Team Plan trial, which activates full CI failure analysis without extra setup.
Frequently Asked Questions
How do I set OPENAI_KEY for Qodo in CircleCI?
Open your CircleCI project settings, select Environment Variables, and add OPENAI_KEY as a masked variable with your OpenAI API key. Confirm that the key has enough quota and the correct permissions for your expected usage volume. Gitar avoids this step entirely by handling AI model access internally instead of exposing keys in CI.
Why is Qodo PR-Agent not triggering /review commands?
Check webhook configuration in your GitHub repository settings and confirm that pull request events are enabled. Ensure your GitHub App has permissions for webhooks and pull requests, then verify that CircleCI receives webhook payloads by reviewing job logs. Gitar triggers reviews automatically on each pull request without manual commands or webhook tuning.
Is Gitar compatible with CircleCI?
Yes, Gitar supports CircleCI integration. The system analyzes CI failures from CircleCI pipelines and commits fixes directly to pull requests, using the same Healing Engine described above.
How do I fix Qodo large PR timeouts?
Set max_model_tokens in your .pr_agent.toml file and configure fallback models to handle context window limits. Enable enable_large_pr_handling and monitor logs for AttributeError messages until they disappear. Gitar manages large pull requests by chunking analysis and preserving context across model calls, so no timeout configuration is required.
What are the webhook validation steps for Qodo?
Confirm that webhook signatures match between GitHub App settings and CircleCI environment variables. Test webhook delivery in GitHub repository settings and check CircleCI logs for payload receipt. Ensure your webhook secret is masked in CircleCI and matches the value in your pr-agent configuration. Gitar connects directly with GitHub Apps and removes the need for manual secret management.
Conclusion: From Qodo Fixes to Gitar’s Autonomous CI
This guide walked through five categories of Qodo PR-Agent failures in CircleCI. You saw how missing API keys cause authentication errors, how token limits and context windows break large PRs, how TOML and YAML configuration mistakes disrupt reviews, how webhook signature mismatches block triggers, and how ongoing maintenance keeps all of these pieces in sync.
Each fix addresses a symptom of a deeper problem. Qodo requires you to coordinate GitHub tokens, OpenAI keys, webhook secrets, Docker images, and TOML files, which creates many chances for pipelines to fail.
Gitar’s CI Failure Analysis deduplicates failures across jobs, surfaces causes without log digging, and keeps information updated in real time.
The 2026 development landscape favors autonomous systems that remove configuration overhead instead of adding more tools to maintain. Gitar’s Healing Engine delivers CircleCI integration, automatic failure resolution, and consistently green builds without the upkeep of traditional AI review tools.
Start your 14-day Team Plan trial to automatically fix broken builds and ship higher quality software faster, with no additional configuration.