Written by: Ali-Reza Adl-Tabatabai, Founder and CEO, Gitar
Key Takeaways for Faster, Consistent Code Reviews
- AI coding tools speed up coding 3 to 5 times but increase PR review time by 91%, so automated style enforcement in CI has become essential.
- Define coding standards with config files like .editorconfig, ESLint, and Ruff, then wire those linters into CI workflows for GitHub Actions, GitLab CI, and other platforms.
- Use branch protection rules and pre-commit hooks to block merges on violations and catch style issues before they reach production.
- Gitar’s healing engine goes beyond suggestions by automatically fixing lint errors, test failures, and build breaks, which keeps CI builds green.
- Start your 14-day free trial at Gitar.ai to automate fixes and ship higher-quality software faster.
5 Steps to Automate Code Style Enforcement in CI/CD
Automated code review style enforcement works best when you build it in layers that cover every stage of development.
- Define coding standards with configuration files (.editorconfig, ESLint, Ruff).
- Integrate linters into CI pipeline YAML workflows.
- Configure branch protection rules to block merges on violations.
- Add pre-commit hooks for local enforcement.
- Enhance enforcement with AI auto-fix capabilities through Gitar’s healing engine.
Step 1: Define Your Coding Standards with Config Files
Start by establishing consistent style rules across your codebase using language-specific configuration files. For JavaScript projects, ESLint remains the standard choice, while Ruff has emerged as the fastest Python linter in 2026, outperforming Pylint and Flake8 and includes built-in autofix capabilities.
Create an .editorconfig file for universal formatting:
root = true [*] charset = utf-8 end_of_line = lf indent_style = space indent_size = 2 trim_trailing_whitespace = true
For Python projects, configure Ruff in pyproject.toml:
[tool.ruff] line-length = 88 select = [“E”, “F”, “W”, “C90”] ignore = [“E203”, “W503”]
Java projects should implement Checkstyle with custom rule sets. See the Gitar documentation for comprehensive configuration examples across different languages.
After you define these standards in configuration files, connect them to your CI system so every commit and pull request must follow the same rules.
GitHub Actions Workflow for Code Style Enforcement
Create a .github/workflows/code-quality.yml file to automate style enforcement in GitHub Actions:
name: Code Quality on: [push, pull_request] jobs: lint: runs-on: ubuntu-latest steps: – uses: actions/checkout@v4 – name: Set up Node.js uses: actions/setup-node@v4 with: node-version: ’18’ – name: Install dependencies run: npm ci – name: Run ESLint run: npx eslint . –ext .js,.jsx,.ts,.tsx – name: Run Prettier run: npx prettier –check . python-lint: runs-on: ubuntu-latest steps: – uses: actions/checkout@v4 – name: Set up Python uses: actions/setup-python@v4 with: python-version: ‘3.11’ – name: Install Ruff run: pip install ruff – name: Run Ruff run: ruff check .
This workflow fails the CI pipeline when style violations appear, which prevents merges until issues are resolved. The multi-language setup covers JavaScript, TypeScript, and Python codebases in a single, consistent process.
Branch Protection Rules to Block Lint Failures
Branch protection rules turn your lint workflows into hard gates that block non-compliant code. In GitHub, go to Settings > Branches and enable “Require status checks to pass before merging.” Repository administrators can configure code quality gates to block pull request merges if findings exceed specified severity levels.
Select your lint workflow jobs as required status checks so no code reaches the main branch without passing style enforcement. GitLab offers similar controls through push rules and merge request approvals.
Eliminate manual fix cycles entirely with Gitar’s automated healing engine and keep these protection rules from slowing your team down.
Pre-Commit Hooks, CI Linters, and Lint-Staged
Pre-commit hooks give developers instant feedback, while CI linters act as the final quality gate before merging. Install pre-commit hooks with:
npm install –save-dev lint-staged husky npx husky install npx husky add .husky/pre-commit “npx lint-staged”
Configure lint-staged in package.json:
{ “lint-staged”: { “*.{js,jsx,ts,tsx}”: [“eslint –fix”, “prettier –write”], “*.py”: [“ruff check –fix”] } }
This setup catches issues early while CI remains the authoritative quality gate. Teams that need deeper analysis can add SonarQube for enterprise-grade static analysis with quality gates that integrate across multiple CI platforms.
GitLab CI YAML Snippet for Style Enforcement
GitLab CI users can enforce style rules with a simple YAML configuration:
stages: – lint eslint: stage: lint image: node:18 script: – npm ci – npx eslint . –ext .js,.jsx,.ts,.tsx only: – merge_requests – main
CircleCI users can create similar workflows and rely on the orb ecosystem for streamlined linter integration across multiple languages and frameworks.
Auto-Fix Lint Errors in CI with Gitar’s Healing Engine
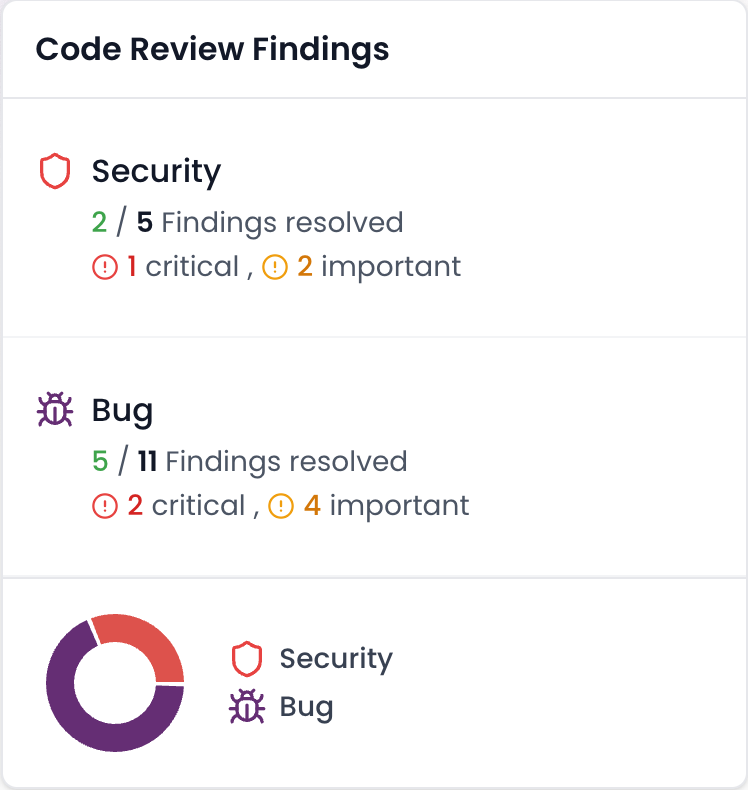
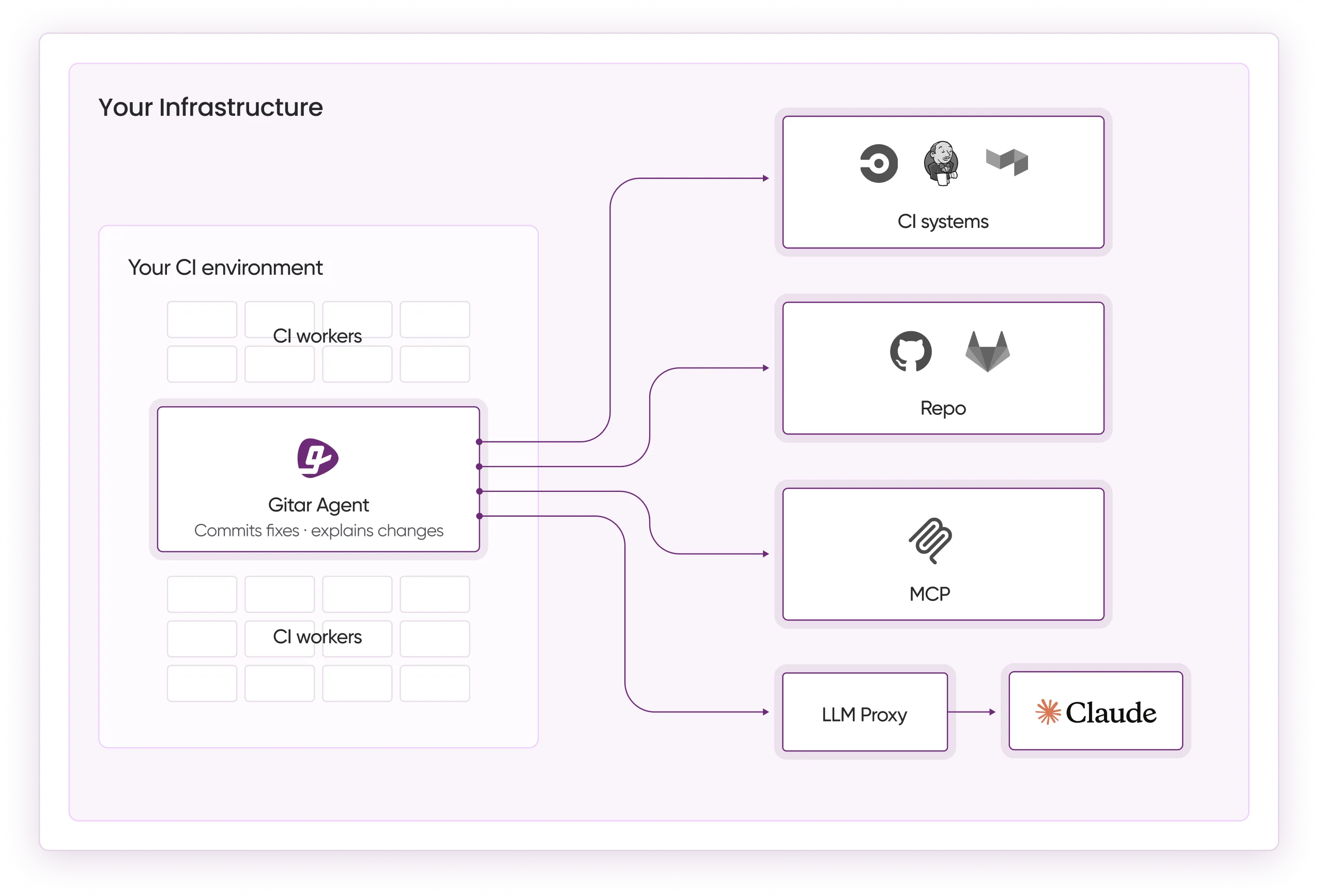
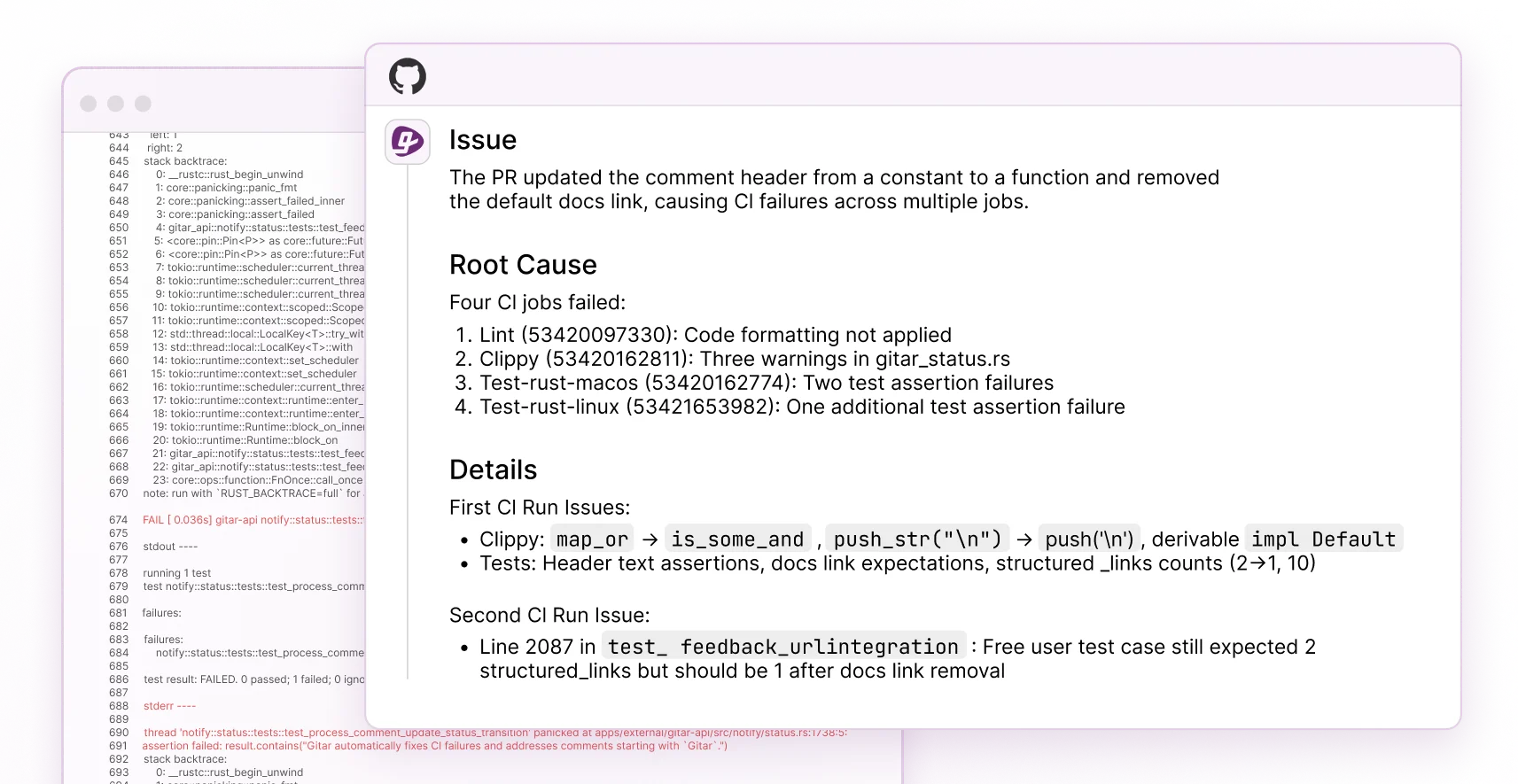
Traditional linters only identify violations, while Gitar’s healing engine analyzes and fixes CI failures, including lint errors. Install Gitar through the official site and follow a four-phase rollout that builds trust and automation over time.
Phase 1: Installation sets up the Gitar GitHub App or GitLab integration and starts your 14-day Team Plan trial.
Phase 2: Trust Building keeps Gitar in suggestion mode so you can review and approve fixes while it proves it can resolve lint errors, test failures, and build breaks.
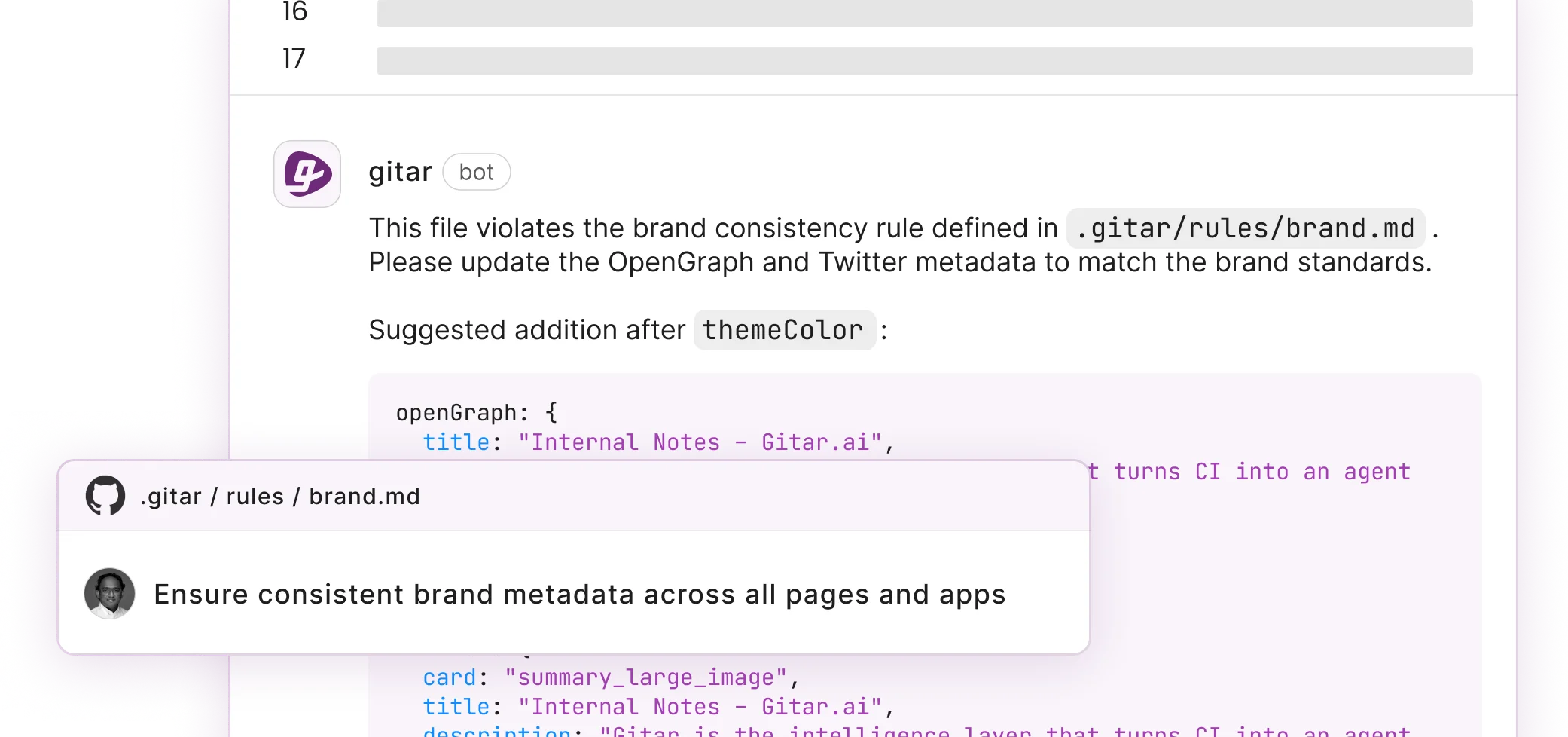
Phase 3: Automation enables auto-commit for trusted fix types and adds repository rules written in natural language in .gitar/rules/*.md files.
Phase 4: Platform Expansion uses analytics, custom workflows, and enterprise features such as running agents inside your own CI infrastructure.
Create custom rules using natural language:
— title: “Security Review” when: “PRs modifying authentication or encryption code” actions: “Assign security team and add label” —
This capability to auto-apply and validate fixes distinguishes Gitar from suggestion-only tools in real CI environments:
|
Capability |
CodeRabbit/Greptile |
Gitar |
|
Suggestions |
Yes |
Yes |
|
Auto-apply fixes |
No |
Yes |
|
CI validation |
No |
Yes |
|
Green build guarantee |
No |
Yes |
Experience the difference between suggestion engines and healing engines with Gitar’s 14-day free trial and see these capabilities in your own pipelines.
Custom Rules, CI Pitfalls, and How Gitar Helps
Gitar excels at enforcing team-specific coding standards through natural language rules that go beyond standard linters. Common pitfalls include 73% of enterprise CI/CD integrations failing because vendors focus on individual workflows instead of production pipelines.
Teams avoid configuration drift by keeping rules as code and by using enforcement tools that understand the complete deployment topology, not just isolated file diffs. Gitar’s rules-as-code model and CI-aware agents address these failure modes directly, building on the documentation you saw earlier.
FAQ
Does Gitar handle custom linters beyond ESLint and Ruff?
Gitar’s healing engine analyzes and fixes CI failures from any linter. You can define custom rules using natural language in .gitar/rules/*.md files to enforce team-specific patterns. The platform learns your codebase patterns and applies fixes consistently across the entire repository.
How does Gitar compare to CodeRabbit for code style enforcement?
CodeRabbit provides suggestions and comments but requires manual implementation of fixes and charges $15 to $30 per developer for that limited functionality. Gitar automatically applies fixes, validates them against your CI pipeline, and guarantees green builds. During the trial period, you get full access to auto-fix capabilities that remove this manual work.
Should I use pre-commit hooks or CI linters for style enforcement?
Use both to cover local development and shared branches. Pre-commit hooks catch issues during development for faster feedback, while CI linters act as the authoritative quality gate that stops non-compliant code from reaching production. Gitar combines both approaches by fixing issues during development and keeping CI pipelines green.
Does Gitar support multi-platform CI environments?
Yes, Gitar integrates with GitHub Actions, GitLab CI, CircleCI, and Buildkite. The platform emulates your complete CI environment, including specific SDK versions, multi-dependency builds, and third-party security scans. Enterprise customers can run Gitar agents within their own CI infrastructure for maximum security and context.
What is the ROI of automated code style enforcement?
Automated style enforcement reduces merge delays by up to 80% by removing manual fix cycles. For a 20-developer team, this can save about 45 minutes per developer per day on CI and review issues, which creates productivity gains that far exceed the cost of automation tools.
Conclusion: Turn CI Style Checks into Automatic Fixes with Gitar
AI-assisted development has shifted the bottleneck from writing code to reviewing and stabilizing it in CI. Traditional linters highlight style violations, while Gitar’s healing engine fixes them, validates the changes, and keeps builds green, which moves teams from suggestion engines to true automation.
Start your free trial today and see how Gitar transforms CI failures into automatic fixes so your team can focus on shipping features instead of chasing lint errors.