Written by: Ali-Reza Adl-Tabatabai, Founder and CEO, Gitar
Key Takeaways for Securing AI-Assisted Code
- 84% of developers use AI coding tools, and 45% of AI-generated code contains security vulnerabilities like SQL injection and XSS.
- Gitar focuses on AI-powered auto-fixing of security issues directly in PRs, with fixes validated by CI pipelines during its 14-day Team Plan trial.
- GitHub CodeQL delivers semantic analysis for public repos, while Semgrep cuts false positives by up to 98% with custom rules.
- Snyk OSS and SonarCloud support multi-language scanning and dependency checks, which works well for open-source projects.
- Teams can combine open-source tools for private repo scanning or start a Gitar trial today for GitHub security with automated fixes.
How To Evaluate AI Code Security Scanners for GitHub
When selecting an AI code security scanner for GitHub projects, start by checking whether the tool uses AI-powered contextual analysis or traditional rule-based detection. This choice affects both accuracy and false positive rates. Next, review free tier limits and private repository support, because these factors shape your long-term cost and coverage.
Then assess practical implementation details such as GitHub Actions integration complexity, automatic fix capabilities, supported programming languages, and setup time. These elements determine how quickly your team can reach reliable security coverage. Review vendor documentation and release notes to track feature maturity and stability over time.
1. Gitar (Top Pick for Auto-Fixing)
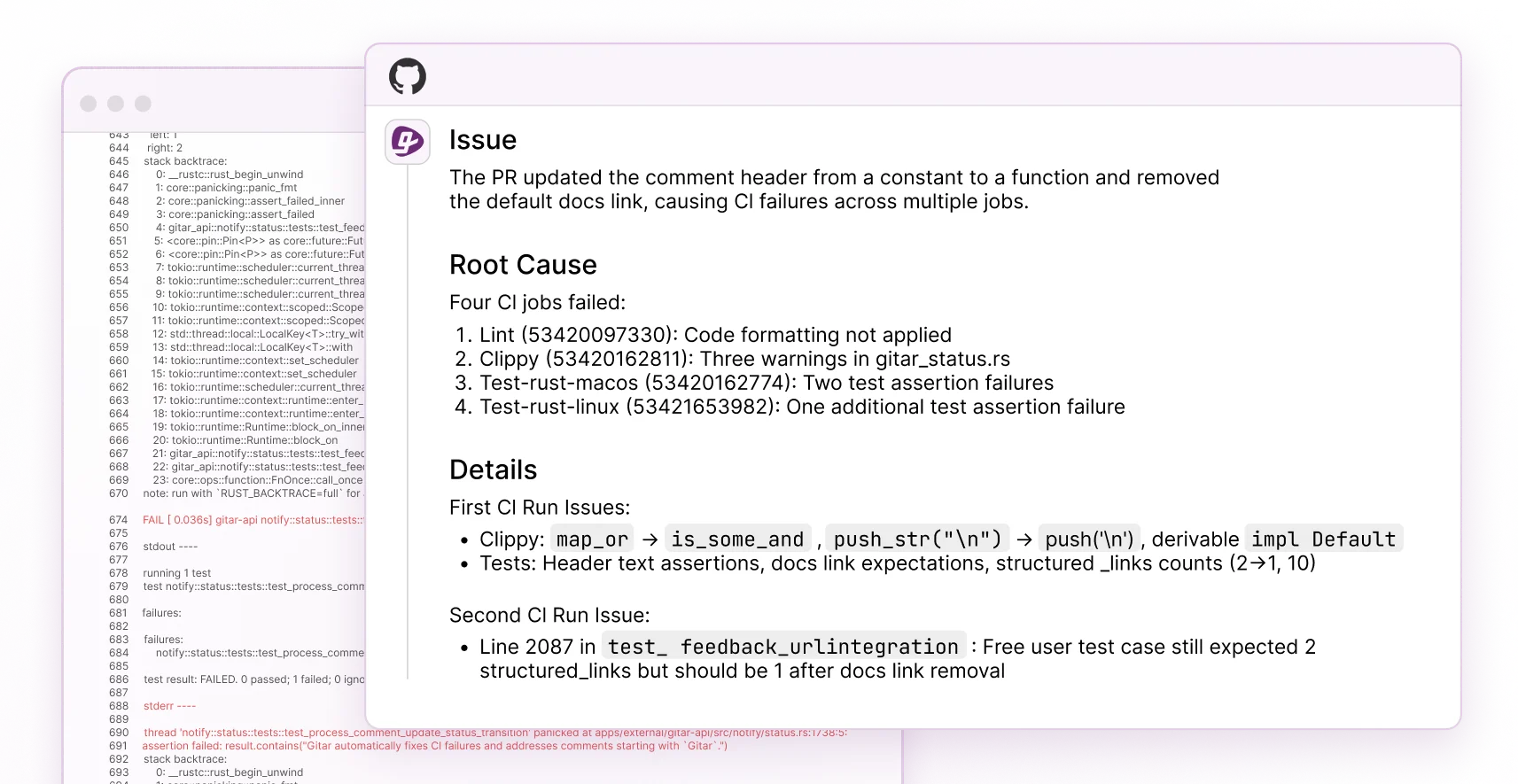
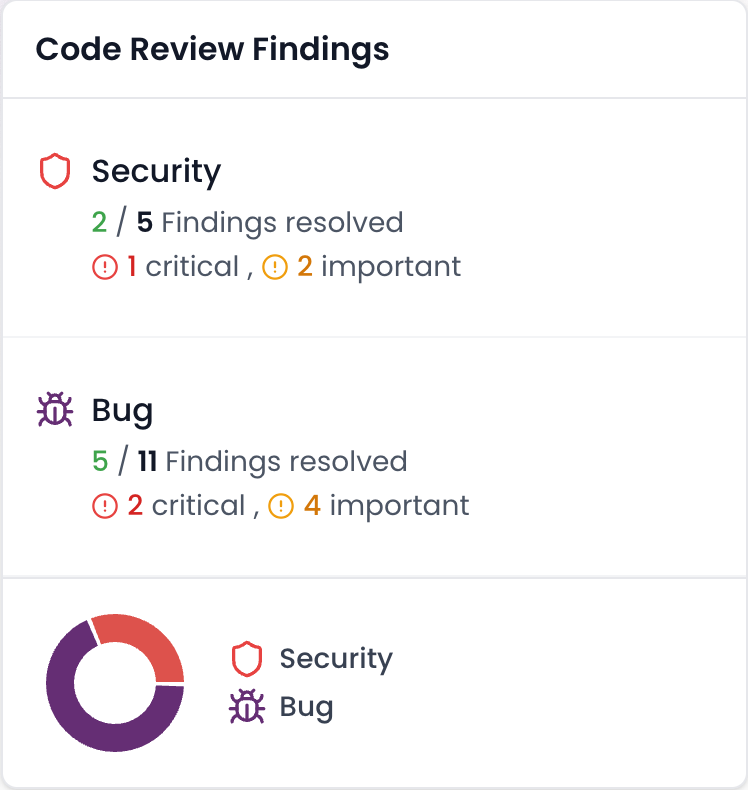
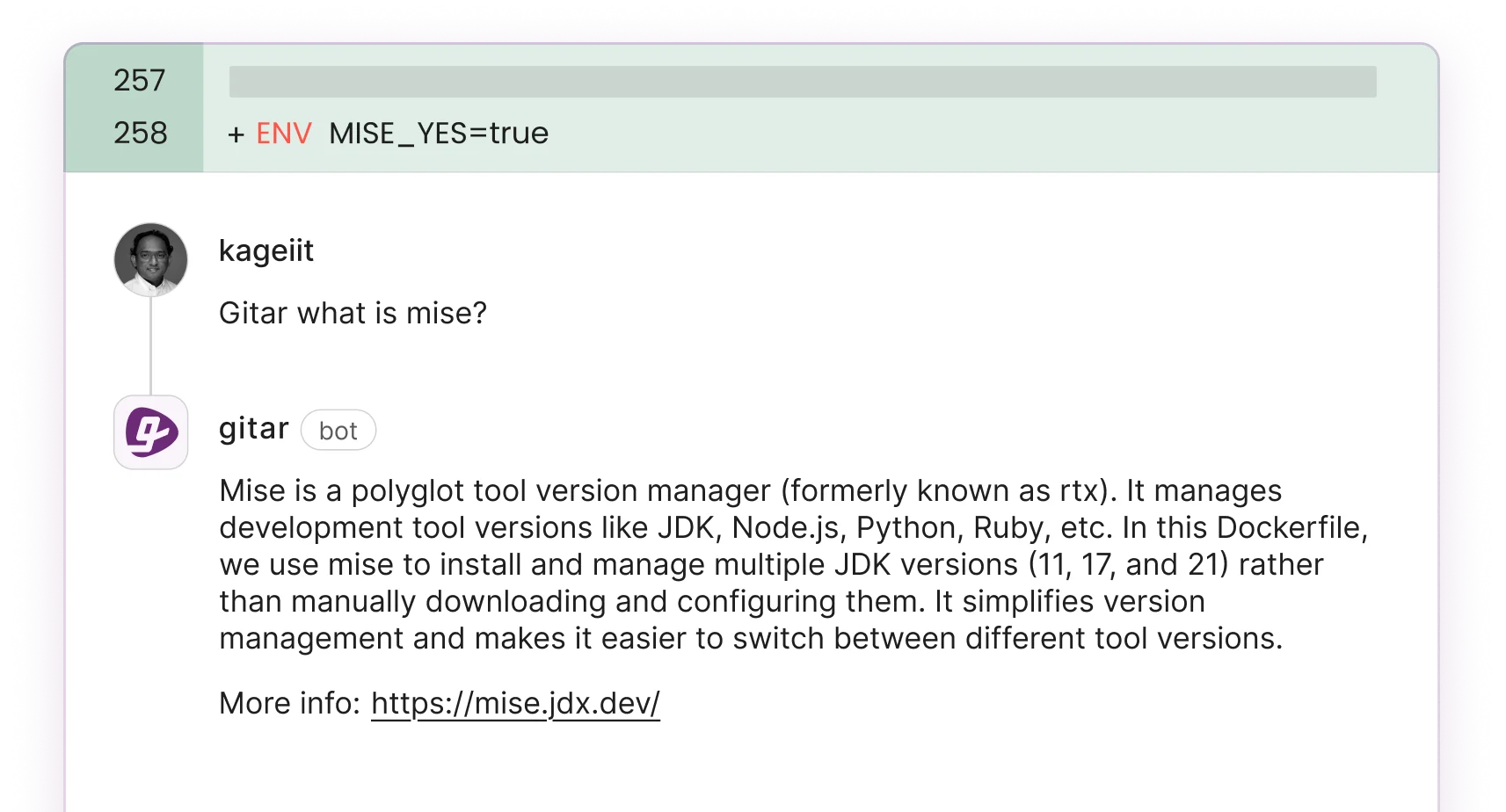
Gitar’s AI healing engine delivers end-to-end code review and security scanning, then automatically fixes CI failures, bugs, and vulnerabilities directly in pull requests and CI pipelines. The trial includes unlimited users and full access to inline code review comments, CI failure analysis, and the GitHub App integration.
Key features include configurable PR merge blocking based on code review verdict severity and inline code review comments with verdict badges that appear on the exact lines needing attention. Gitar’s CI failure analysis deduplicates failures across multiple jobs and surfaces root causes, so teams avoid manual log digging.
Setup takes about 30 seconds by installing the GitHub App from docs.gitar.ai. The platform holds SOC 2 Type 2 certification for enterprise-grade security, which helps satisfy compliance requirements.
| Feature | Pro | Con |
|---|---|---|
| Auto-fix | Validates fixes in CI | Trial period limited |
| Private repos | Full trial support | Requires GitHub App |
| Setup | 30-second installation | Learning curve for rules |
Gitar works best for teams overwhelmed by PR reviews who want reliable fixes instead of suggestion-only reports.
2. GitHub CodeQL for Semantic Vulnerability Detection
GitHub Advanced Security offers CodeQL-powered SAST with semantic analysis for OWASP Top 10 vulnerabilities, including SQL injection detection through data flow paths from user input to database queries. Copilot Autofix generates targeted patches for vulnerabilities and supports push protection for secrets.
Given that 45% of AI-generated code contains vulnerabilities, GitHub Advanced Security with CodeQL helps teams catch these issues through semantic analysis before they reach production. CodeQL integrates natively with GitHub, which simplifies adoption, but private repositories require GitHub Advanced Security licensing at $30 per active committer each month.
| Feature | Pro | Con |
|---|---|---|
| Integration | Native GitHub platform | Private repos require licensing |
| Coverage | OWASP Top 10 detection | Advanced customization needed for complex cases |
| Setup | Standard Actions workflow | Custom query development required |
CodeQL fits public repositories that need enterprise-grade semantic analysis without adding separate tools.
3. Semgrep for Custom Rules and Low Noise
Semgrep provides AI-powered contextual analysis with dataflow-based reachability that eliminates up to 98% of false positives for high-severity dependency vulnerabilities. The Semgrep Assistant learns from human triage decisions and auto-generates new rules, which improves accuracy over time.
Semgrep Community Edition integrates with GitHub for pattern-based OWASP Top 10 scanning using custom rules. Teams can tune rulesets for large polyglot repositories and still keep noise low.
| Feature | Pro | Con |
|---|---|---|
| Accuracy | 98% false positive reduction | Rule-based limitations |
| Customization | Custom rule creation | Requires rule expertise |
| Performance | Fast scanning speed | Self-hosting option for private repos |
Semgrep suits teams that need custom security rules and predictable, low-noise findings.
4. Snyk OSS for Dependency and Container Security
Snyk’s DeepCode AI engine combines symbolic and generative AI for context-aware static analysis with auto-fix suggestions trained on millions of real-world fixes. The platform scans more than 15 million open-source packages and detected over 24,000 new vulnerabilities in 2024.
Snyk covers software composition analysis, container scanning, and Infrastructure as Code security. The platform offers scanning for public and private GitHub repositories and integrates with GitHub Actions.
| Feature | Pro | Con |
|---|---|---|
| SCA depth | 15M+ package coverage | Limited scan frequency |
| AI fixes | Real-world training data | Fix validation via PR review |
| Integration | Multiple CI platforms | Rate limiting on free tier |
Snyk OSS works well for open-source projects that need strong dependency and container vulnerability management.
5. SonarCloud for Code Quality and Security Gates
SonarQube scans source code for bugs, vulnerabilities, and security hotspots with built-in AI CodeFix for contextual fix suggestions. The community edition supports static analysis across more than a dozen languages including Java, JavaScript, and TypeScript.
The platform enforces quality gates that block non-compliant code and offers real-time IDE feedback through SonarLint. SonarCloud extends this capability to the cloud and provides analysis for open-source projects with GitHub Actions support.
| Feature | Pro | Con |
|---|---|---|
| Language support | 12+ programming languages | No true auto-fix capability |
| Quality gates | Automated compliance blocking | OSS projects only for free |
| IDE integration | Real-time feedback | Limited AI features |
Install Gitar now to automatically fix security vulnerabilities that SonarCloud only highlights, with validated fixes that keep builds green.
6. DeepSource for Security and Performance Analysis
DeepSource provides AI-powered static analysis for security vulnerabilities, code quality issues, and performance problems across many programming languages. The platform suggests automated fixes and integrates with GitHub through pull request analysis.
The free tier supports public repositories with unlimited analysis runs and collaboration features, while paid plans unlock private repository scanning. DeepSource detects security anti-patterns and explains each finding in detail, which helps developers learn as they remediate.
| Feature | Pro | Con |
|---|---|---|
| Analysis depth | Security and performance | Paid for private repos |
| Explanations | Detailed issue context | Autofix via PRs |
| Team features | Collaboration tools | 30+ languages supported |
DeepSource suits open-source projects that want broad code quality coverage in addition to security checks.
7. Trivy for Container and IaC Security
Trivy scans filesystems, container images, IaC configurations, and code for vulnerabilities, misconfigurations, and secrets using a large vulnerability database. Aqua Security’s Trivy detects secrets within code, containers, and IaC files through extensive CI/CD plugin support including GitHub Actions.
Trivy delivers fast scans with strong accuracy for container and Infrastructure as Code security. Teams can secure private repositories by running Trivy inside CI/CD pipelines rather than granting direct repo access.
| Feature | Pro | Con |
|---|---|---|
| IaC scanning | Comprehensive coverage | Rule-heavy approach |
| Container security | Image vulnerability detection | Limited AI features |
| Speed | Fast scanning performance | No auto-fix capability |
Trivy fits DevOps teams that focus on container and infrastructure security alongside application code.
Free Private Repository Scanning Workarounds
Teams that want to avoid subscriptions can combine several open-source tools for private GitHub repositories. Gitleaks integrates with GitHub Actions using a simple workflow that scans private repositories for more than 150 secret types. TruffleHog scans git history for over 800 secret types with credential verification, which reduces false alarms.
Teams can build an “Ultimate Free Stack” by pairing Semgrep Community Edition for SAST, Trivy for container scanning, and Gitleaks for secret detection in a single GitHub Actions workflow. This stack offers broad coverage without subscription costs, but it requires manual configuration and does not provide the auto-fix capabilities available in Gitar’s trial.
Tool Comparison Matrix for Fast Shortlisting
The following tables compare the seven scanners across key decision factors such as free tier access, AI capabilities, private repository support, auto-fix strength, language coverage, and GitHub setup effort. Use these side-by-side views to quickly narrow options that match your team’s security goals and workflow constraints.
| Tool | Free Tier Details | AI Depth | Private Repos |
|---|---|---|---|
| Gitar | 14-day full trial | AI code review and auto-fix | Full trial support |
| GitHub CodeQL | Public repos unlimited | Semantic analysis | Advanced Security required |
| Semgrep | Community edition | Contextual analysis | Self-hosting required |
| Snyk OSS | Public and private repos | DeepCode AI engine | Free tier supported |
| Tool | Auto-Fix Security | Languages | GitHub Setup |
|---|---|---|---|
| Gitar | Full auto-fix | Multi-language | 30-second install |
| GitHub CodeQL | Security alerts and patches | 20+ languages | Native Actions |
| Semgrep | AI autofixes available | 17+ languages | Simple YAML |
| Snyk OSS | Automated PR fixes | 10+ languages | Actions marketplace |
Key Considerations and Tradeoffs for Your Team
Solo developers should focus on GitHub Actions simplicity and short setup time, while teams gain more from auto-fix capabilities that cut manual remediation. Implementation complexity also matters, with Gitar offering a 30-second setup compared to multi-tool stacks that demand deeper YAML and CI knowledge. Organizations using AI agents for quality control can prevent security vulnerabilities that would overwhelm human review capacity.
When comparing scanners, include developer time savings, training effort, and maintenance overhead in your total cost of ownership, not just subscription pricing.
Frequently Asked Questions
Scanning Private GitHub Repositories Without Enterprise Contracts
Several approaches support private repositories without long-term enterprise commitments. Open-source tools such as Gitleaks, TruffleHog, and Semgrep Community Edition can run inside GitHub Actions workflows to deliver broad coverage. Gitar’s 14-day Team Plan trial also supports private repositories with automatic vulnerability fixes, which lets teams test enterprise-grade capabilities before paying.
Difference Between AI-Powered and Rule-Based Security Scanners
AI-powered scanners use machine learning to understand code context, data flow, and complex vulnerability patterns that simple regex rules miss. These tools can detect logic flaws, authentication issues, and advanced attack paths while reducing false positives through contextual reasoning. Rule-based scanners rely on predefined patterns and signatures, which makes them fast but less effective at spotting new or highly contextual vulnerabilities.
Automatic Fixing of Vulnerabilities During Gitar’s Trial
Gitar’s 14-day Team Plan trial includes the full healing engine that analyzes security findings, generates validated fixes, and commits them to your pull requests. The platform validates each fix against your CI pipeline to confirm that it resolves the issue without breaking functionality. This approach gives teams confidence in secure, green builds.
Best Scanners for SQL Injection and XSS Detection
GitHub CodeQL excels at SQL injection detection through semantic data flow analysis that traces user input to database queries across functions. For XSS detection, Semgrep’s pattern-based rules combined with AI contextual analysis provide strong accuracy with low false positive rates. Gitar complements both tools by automatically fixing these vulnerabilities after detection instead of leaving them for manual remediation.
Setting Up Multi-Tool Security Scanning in GitHub Actions
To run multiple scanners, define a GitHub Actions workflow that chains or parallels each tool in a single YAML file. Use Gitleaks for secret scanning, Semgrep for SAST, and Trivy for container vulnerabilities. Configure matrix builds so these tools run in parallel and reduce total scan time. This approach offers flexibility but introduces configuration overhead compared to integrated options like Gitar’s single-step setup.
Conclusion and Next Steps for Securing Your GitHub Projects
Start by running these scanners against your own repositories and tracking which tools surface the most relevant vulnerabilities with manageable noise. Pay close attention to GitHub Actions integration effort and false positive rates during your trials. For teams that want immediate productivity gains, start your Gitar 14-day trial and experience automatic vulnerability fixes that keep builds secure and green while you continue evaluating other options.
