Written by: Ali-Reza Adl-Tabatabai, Founder and CEO, Gitar
Key Takeaways
- AI-generated code increases PR volume and review times, with half of PRs idle over 50% of their lifespan, costing teams up to $1M annually.
- Brittle YAML configs cause 60% of CI delays due to indentation errors, unpinned versions, and hardcoded secrets vulnerable to supply chain attacks.
- Apply 10 concrete practices such as 2-space indentation, anchors and aliases, version pinning to SHAs, parallel jobs, and caching to build robust workflows.
- Gitar’s healing engine auto-fixes CI failures, uses natural language rules, and guarantees green builds, outperforming traditional YAML and suggestion tools.
- Start a Team Plan trial with Gitar to automate code reviews, reduce YAML maintenance, and ship features faster.
The Problem: Why YAML Configs Fail in AI-Driven Code Review Workflows
AI-generated code has exposed critical weaknesses in traditional YAML-based CI/CD configurations. Second Talent’s 2026 report found that AI-generated code has 1.7x more issues, 1.75x more logic errors, and 1.57x more security vulnerabilities than human-written code, yet most teams still rely on fragile YAML configs that cannot adapt to this new reality.
Common YAML pitfalls include indentation errors that break entire pipelines, unpinned action versions vulnerable to supply chain attacks, and hardcoded secrets that leak into logs. The tj-actions/changed-files action compromise in March 2025 (CVE-2025-30066) affected 23,000+ repositories, while GhostAction hijacked 327 accounts and stole 3,325 secrets in September 2025. These incidents show how brittle YAML configurations become attack vectors when teams prioritize speed over security.
Lack of parallelism and caching in poorly configured workflows creates slow feedback loops that compound the AI code review bottleneck. When builds take 15 minutes or more and fail due to simple configuration errors, developer productivity drops and technical debt grows.
The Solution: 10 YAML Config Best Practices for Automating Code Review Workflows
1. Use Consistent 2-Space Indentation and Strategic Quoting
YAML’s whitespace sensitivity requires consistent indentation across every file. All YAML workflow examples consistently use 2-space indentation, unquoted keys, and simple numeric or string values where possible. Use quotes only when strings contain special characters or spaces.
2. Apply Anchors and Aliases for DRY Configuration
Anchors and aliases reduce duplication and keep jobs consistent. Use anchors (&) to define shared blocks and aliases (*) to reuse them across jobs.
3. Enforce Secure Secrets Management
Hardcoded secrets in GitHub Actions YAML workflows remain a top vulnerability, visible to users with read access and persisting in Git history. Store secrets only in GitHub Secrets or external secret managers.
4. Pin Versions for Supply Chain Security
Only 3.9% of GitHub repositories pin 100% of their third-party Actions to immutable commit SHA hashes, which leaves most projects exposed to tag overwrites. Pin every third-party action to a full 40-character commit SHA.
5. Add Schema Validation with Modern Tools
Zod provides runtime validation for external data with automatic TypeScript type inference. Use schema validation to catch configuration errors before deployment.
6. Run Independent Jobs in Parallel
Parallel execution shortens pipelines by running independent checks at the same time. Design workflows to minimize cross-job dependencies.
7. Implement Graceful Error Handling
Handle errors gracefully using proper exit codes and ::error:: or ::warning:: logging commands with file and line annotations. Provide clear summaries for failed steps.
8. Use Strategic Caching
Multi-level caching cuts build times and reduces external API calls. Configure restore-keys so workflows can fall back to broader cache matches.
9. Tune AI Code Review Parameters
CodeRabbit uses a .coderabbit.yaml file in the repository root to tune review focus, set ignore patterns, and customize findings reporting. Configure AI tools with clear thresholds and filters.
10. Configure Multi-Language Matrix Builds
Matrix strategies support diverse codebases by testing across multiple operating systems, language versions, and special cases.
These YAML best practices stabilize your workflows, and Gitar’s auto-fix capabilities remove much of the ongoing maintenance so your team can focus on shipping quality code.
Why Gitar Revolutionizes Code Review Automation
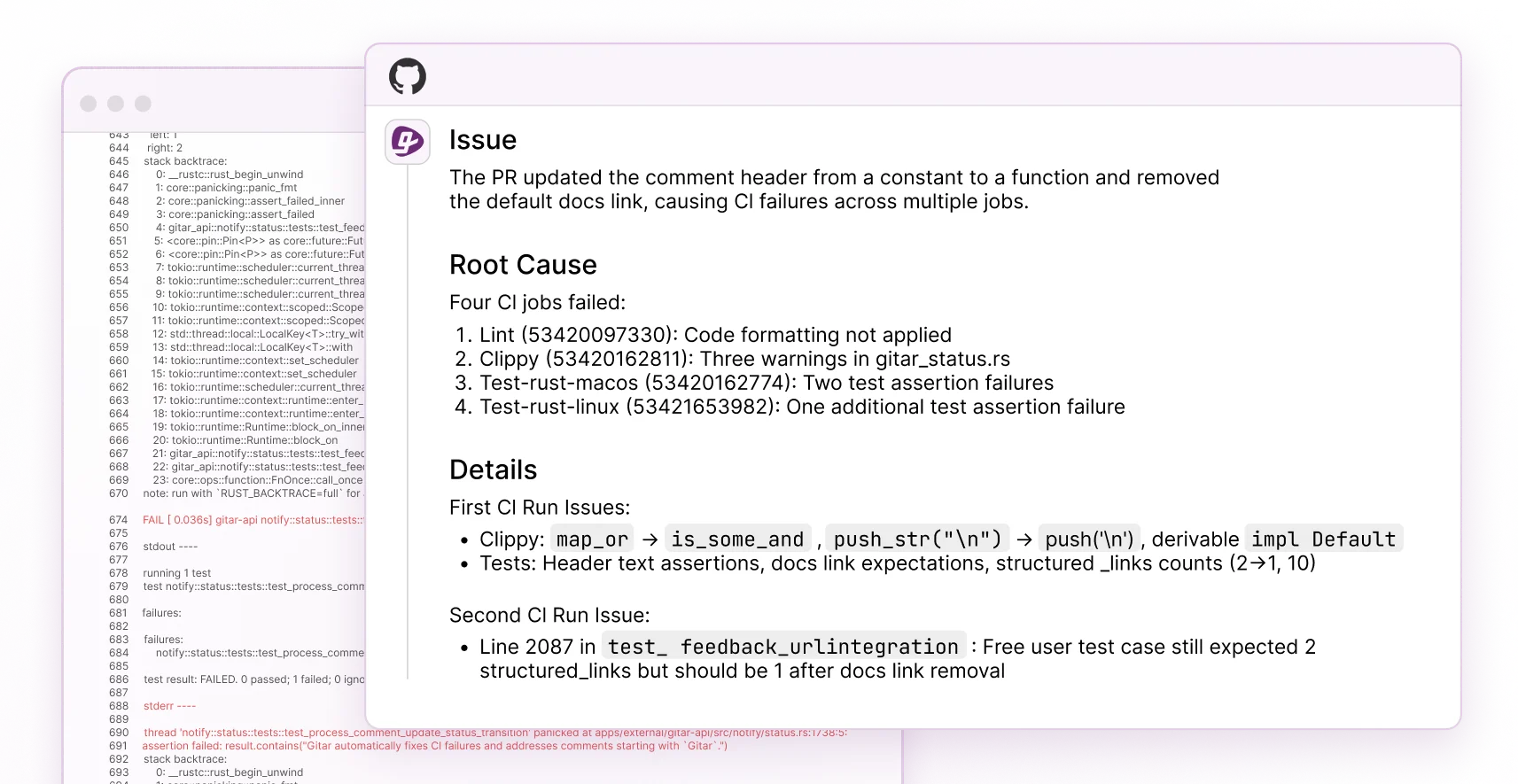
Traditional YAML configurations require constant manual maintenance and deep expertise. Gitar replaces that fragile model with a healing engine that manages code review automation for you. Unlike suggestion-only tools like CodeRabbit, Gitar automatically applies fixes, validates them against CI, and guarantees green builds.
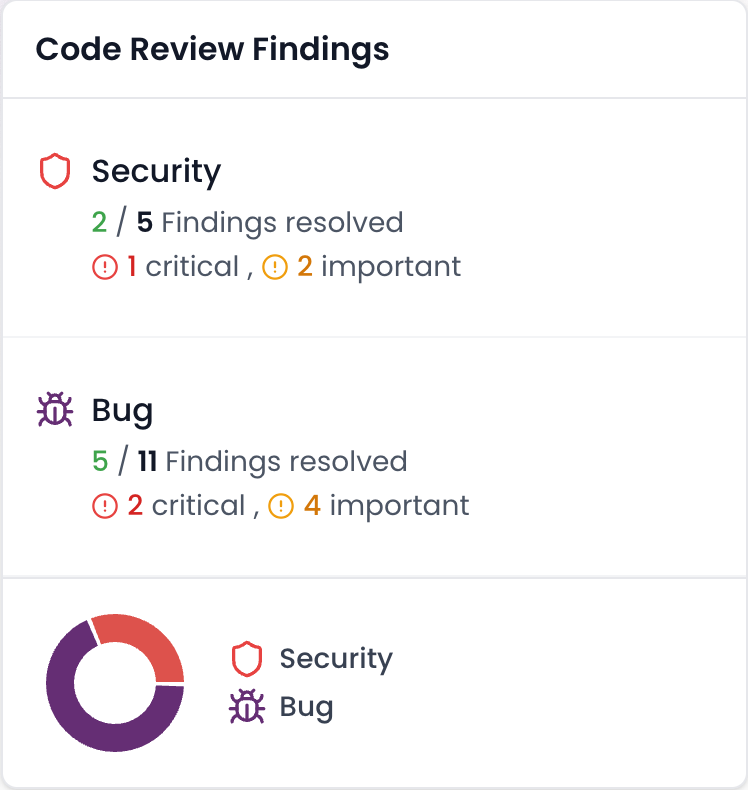
The table below shows how Gitar’s healing engine differs from both static YAML and suggestion-only tools across four critical capabilities that affect daily developer experience.
|
Capability |
Traditional YAML |
CodeRabbit |
Gitar |
|
Auto-fix CI failures |
No |
No |
Yes |
|
Natural language rules |
No |
Limited |
Yes |
|
Validate fixes work |
Manual |
No |
Yes |
|
Single comment interface |
N/A |
No |
Yes |
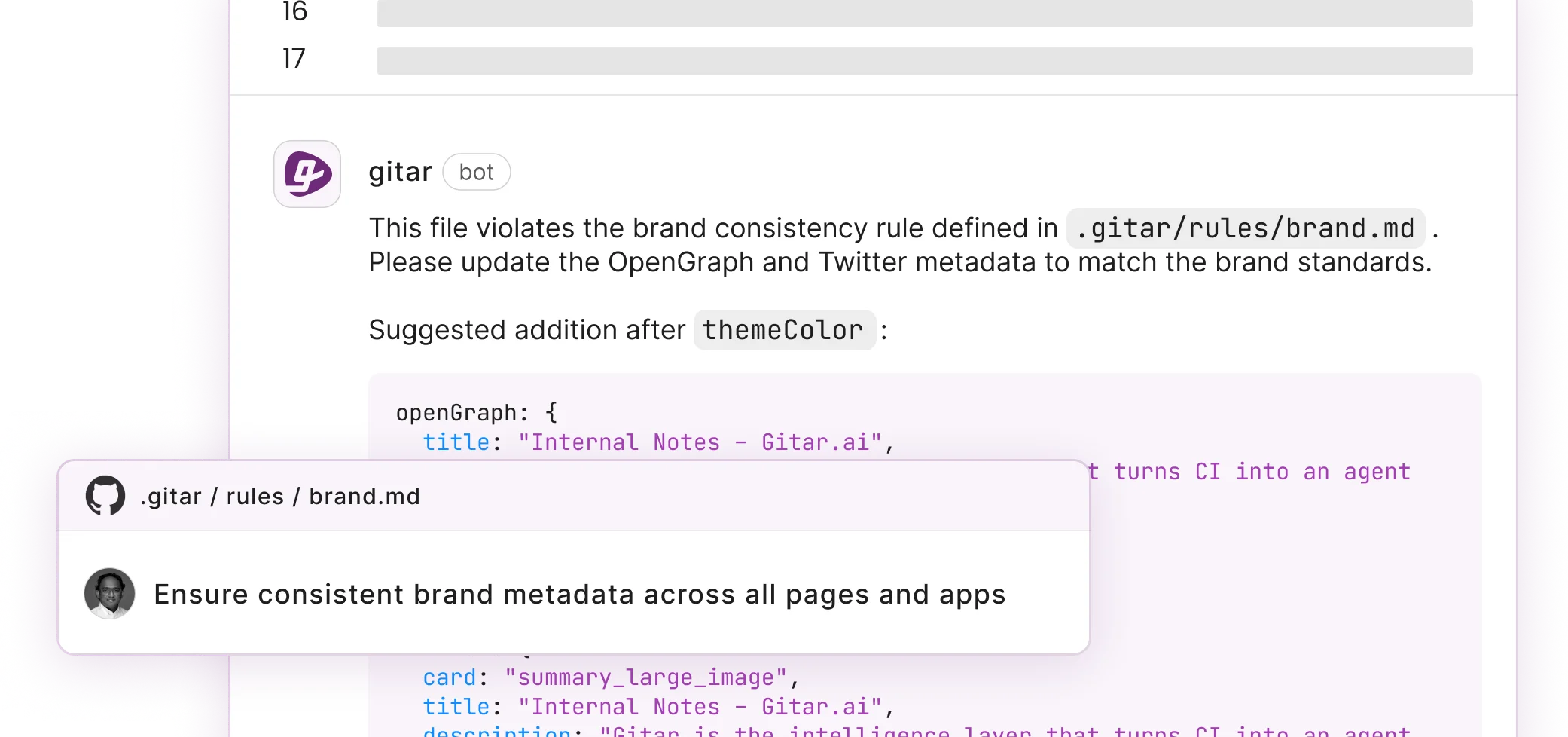
Gitar’s repository rules system lets teams define complex workflows using natural language markdown files in .gitar/rules/, which removes the need for complex YAML syntax. See the Gitar documentation for details. For example:
This approach delivers measurable ROI. Teams report reducing daily CI and review overhead from 1 hour to 15 minutes per developer.
Step-by-Step: Bulletproof YAML and Gradual Gitar Migration
1. Install Gitar: Add the Gitar GitHub App to your repositories to establish the foundation for intelligent automation while your existing YAML workflows continue running.
2. Implement YAML Gates: With Gitar installed, apply the 10 best practices above to create robust baseline configurations with proper indentation, version pinning, and secrets management. These hardened configs keep pipelines stable during the migration.
3. Enable Auto-Fix: After your YAML baseline stabilizes, configure Gitar to resolve CI failures automatically, starting with low-risk fixes such as lint errors and then expanding to build failures and test issues. This phased rollout builds trust in the automation.
4. Create Natural Language Rules: As Gitar proves reliable with auto-fixes, replace complex YAML workflows with readable markdown rules in .gitar/rules/ that describe your team’s review requirements and automation triggers. This completes the shift from manual to intelligent configuration management.
Troubleshooting Common Issues: During migration, watch for unrelated PR failures that signal infrastructure problems rather than code issues. Use TruffleHog for secrets scanning and tune AI model parameters to balance thoroughness with noise reduction.
Teams like Tigris and Collate report that Gitar’s consolidated approach reduces notification fatigue and surfaces more actionable insights than traditional multi-tool setups.
Transform your code review workflow today and let Gitar’s healing engine handle CI failures while your team focuses on building features.
YAML Code Review Automation FAQs
This FAQ section addresses common questions that arise once teams start applying YAML best practices and exploring Gitar for automation.
What are the essential YAML syntax requirements for code review workflows?
YAML code review workflows require consistent 2-space indentation throughout the file, strategic quoting only for strings containing special characters or spaces, and proper use of lists and mappings. Key structural elements include the workflow name, trigger events such as on: pull_request, job definitions with explicit runner specifications like runs-on: ubuntu-latest, and step sequences with clear names and actions. Avoid tabs, keep spacing consistent, and use YAML validators to catch syntax errors before deployment.
How do I secure YAML configurations against supply chain attacks?
Secure YAML configs by pinning all third-party actions to full 40-character commit SHAs instead of version tags, storing all sensitive data in GitHub Secrets or external secret managers, and applying the principle of least privilege for workflow permissions. Enable Dependabot for vulnerability alerts, use action allowlists to restrict which third-party actions can run, and avoid the dangerous pull_request_target trigger that grants write access to fork PRs. Regular security scanning with tools like TruffleHog helps detect accidentally committed secrets.
What AI code review parameters should I configure in YAML?
AI code review tools typically use configuration files such as .coderabbit.yaml to set review intensity levels, ignore patterns for files that should not be reviewed, and custom rules specific to your codebase. Key parameters include model selection for tools that support multiple LLMs, severity thresholds that control which issues trigger comments, and integration settings for posting results. Configure path filters to exclude irrelevant files, choose appropriate review profiles such as strict or chill, and enable auto-review features gradually as you gain confidence in the tool’s accuracy.
How can I improve YAML workflows for faster code review cycles?
Improve YAML workflows by running independent tasks such as linting, testing, and security scanning in parallel, using strategic caching for dependencies and build artifacts, and structuring jobs with clear dependency chains using the needs keyword. Enable fail-fast strategies for critical checks, add proper error handling with continue-on-error where appropriate, and use matrix builds to test multiple configurations at once. Consider composite actions for repeated step sequences and reusable workflows for patterns shared across repositories.
What is the difference between traditional YAML configs and modern AI-powered alternatives?
Traditional YAML configurations require manual maintenance, expert DevOps knowledge, and constant updates as requirements change. They remain brittle, prone to syntax errors, and provide no intelligence about why builds fail or how to fix them. Modern AI-powered alternatives such as Gitar’s repository rules system use natural language markdown files that are easier to read, write, and maintain. These systems can diagnose CI failures, apply fixes, and evolve configurations as the codebase changes, which reduces operational burden while improving reliability.
Conclusion: Master YAML Today, Automate Fully with Gitar Tomorrow
YAML config best practices create the foundation for reliable code review automation, yet manual configuration management cannot keep pace with AI-accelerated development. The 10 practices outlined above, from consistent indentation to strategic caching, stabilize current workflows and reduce immediate pain points.
Intelligent platforms now extend that foundation by evolving beyond static configurations. Gitar’s healing engine approach transforms brittle YAML into autonomous workflows that self-heal without human intervention, delivering on the green build guarantee discussed earlier.
Install Gitar now to move beyond static YAML and let the healing engine manage CI failures while your team focuses on product work.