Last updated: January 27, 2026
Key Takeaways for CI Leaders
- Flaky tests drag CI/CD success rates down to 82% and create about $750K in annual losses per 20‑developer team.
- Race conditions, timing issues, and order dependencies cause most flakes and erode trust in automated testing.
- Tools like BuildPulse and Datadog detect and quarantine flaky tests but still rely on manual root-cause fixes.
- Gitar analyzes logs, generates validated code fixes, and auto-commits PRs, so teams move beyond detection-only tools.
- Teams see 650–2,200% ROI, 25–50% lower upkeep costs, and support across GitHub Actions, CircleCI, GitLab, and enterprise CI.
- Gitar rolls out in four phases, from free install to full autofix, so teams can adopt autonomous CI remediation safely.
Flaky Tests in 2026: What Causes Them and Why They Hurt
Flaky tests produce inconsistent results on the same code, so a red test no longer reliably signals a real defect. Research shows that 63% of flaky tests in LLM-generated code come from reliance on unordered collections, where tests assume a specific order that the platform never guarantees.
The most common flaky patterns include:
- Race conditions: Tests touch elements before async operations complete, so timing controls success or failure.
- Order dependencies: Tests depend on execution sequence because of shared state or poor cleanup between runs.
- Environment variations: CPU, memory, network latency, or OS differences between developer machines and CI runners.
- Data dependencies: Tests rely on random, stale, or non-deterministic data that changes between executions.
Common flaky test types include timing-based failures from async operations, environment-dependent issues from resource variations, and infrastructure-induced problems from container throttling or network issues.
The financial impact grows quickly. Studies indicate that 16% of test failures are flaky, which undermines confidence in CI and wastes engineering time. A 20‑developer team that spends one hour per day on CI issues can lose roughly $750,000 per year in productivity.
How CI Remediation Tools Differ: From Detection to Healing
The CI remediation market now splits into clear categories, and each category solves a different slice of the flaky test problem.
Detection and Quarantine Tools such as BuildPulse identify flaky tests and quarantine them to reduce noise. This approach avoids false failures but leaves root causes untouched and can hide real bugs that still need attention.
Observability Platforms like Datadog CI Visibility track test performance and failure patterns. These tools excel at monitoring and alerting, yet they stop at insights and do not apply fixes.
Native CI Features from CircleCI, GitHub Actions, and GitLab add retries and basic failure analysis. These features remain tied to a single CI provider and still depend on manual debugging and patching.
Autonomous Healing Engines form the newest category. These systems analyze failures and generate code changes automatically. CircleCI’s Chunk autonomous agent fixes 90% of analyzed flaky tests by opening pull requests, which proves that self-healing pipelines are practical at scale.
|
Capability |
BuildPulse/Datadog/CircleCI |
Gitar |
|
Flaky Detection/Quarantine |
Yes |
Yes (Free) |
|
Root-Cause Analysis |
Partial (reruns/insights) |
Full log analysis |
|
Auto-Fix Code |
No |
Yes (14-day free trial) |
|
CI Validation/Commit |
No |
Yes (14-day free trial) |
AI coding tools now sit in 84% of developer workflows, which means CI pipelines receive more code and more potential failures. Most tools still stop at detection, so teams face a growing gap between identifying flaky tests and actually fixing them. See how Gitar outperforms traditional solutions and try free autonomous CI failure remediation now.
Why Gitar Wins: Free AI Healing with Validated Fixes
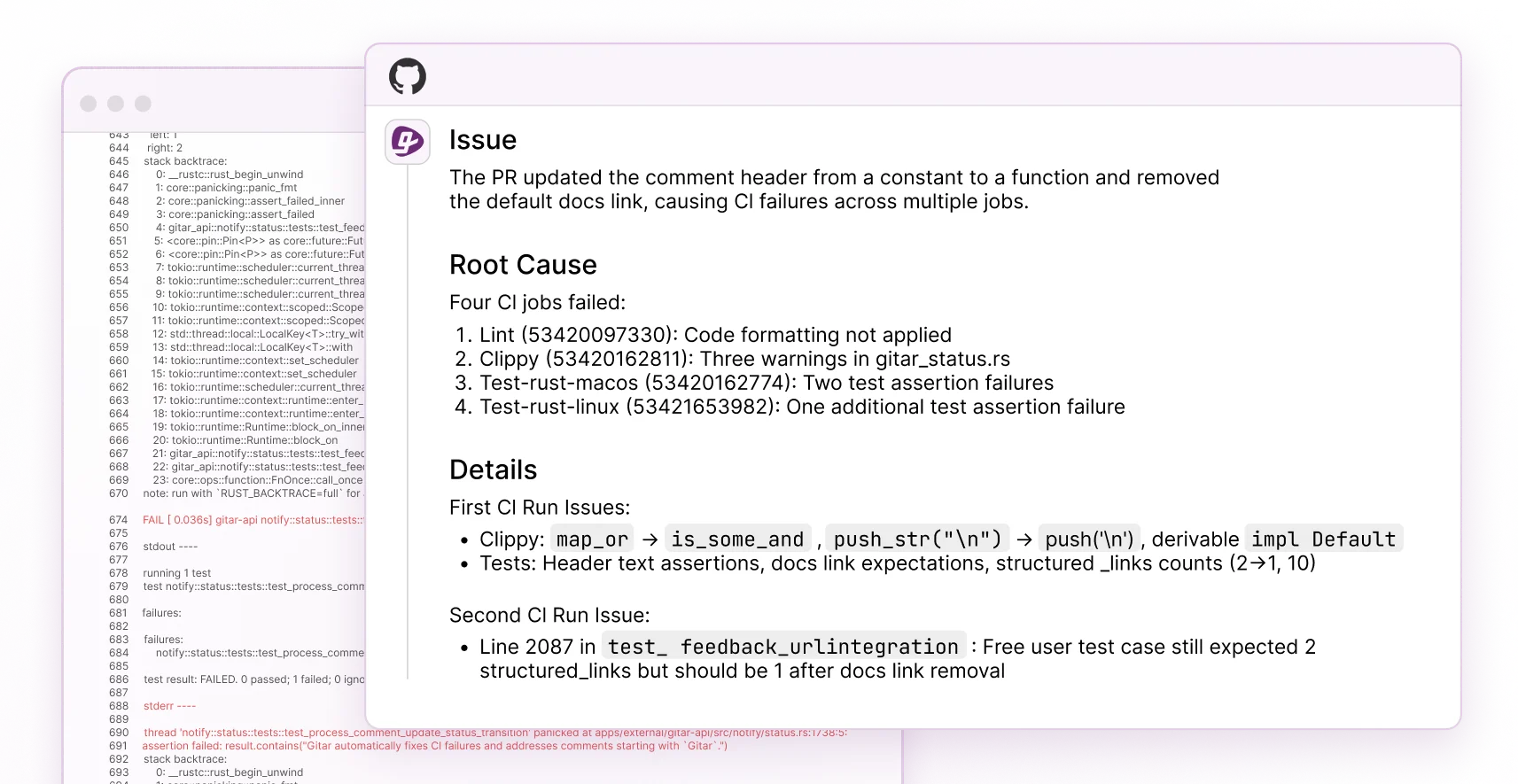
Gitar focuses on healing, not just detection, and drives every failure through a complete remediation loop. When CI fails, Gitar parses the logs, identifies the root cause, generates a context-aware fix using full repository knowledge, validates the change in the real CI environment, and commits a clean PR update.
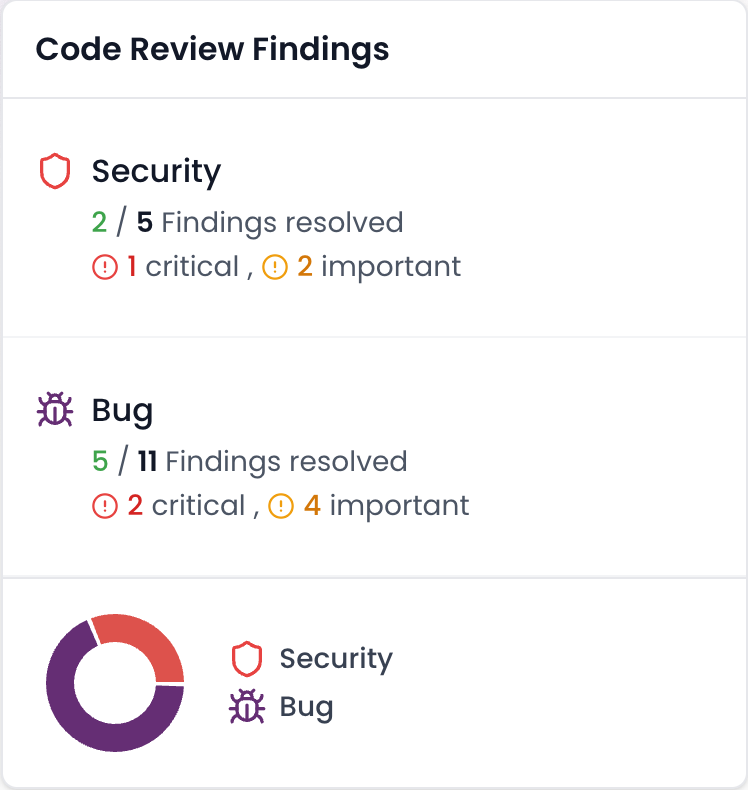
This workflow differs from tools that only suggest patches without running them. Gitar already supports enterprise environments with more than 50 million lines of code and thousands of daily PRs, while still offering a free tier for code review.
The platform has surfaced high-severity security issues in Copilot-generated code that Copilot did not flag. Engineering teams also report that Gitar’s PR summaries are more concise than Greptile and Bugbot. A single updating comment keeps all CI analysis and review feedback in one place and reduces notification noise.
Gitar includes a natural language rules system that lets teams define automation behavior without complex YAML. This approach opens CI automation to every developer, not just DevOps specialists.
Planning for ROI, Build vs Buy, and Toolchain Fit
Autonomous CI remediation delivers measurable financial returns. Enterprises report 25–50% lower automation upkeep costs after adopting self-healing frameworks. Some organizations save about $750,000 per year for a 20‑developer team by cutting CI time from one hour to 15 minutes per day per engineer.
Most enterprises achieve 650–2,200% first-year ROI from autonomous testing through reduced test maintenance and faster releases.
Build-versus-buy decisions must factor in the complexity of a homegrown remediation engine. Custom LLM scripts demand heavy engineering effort, rarely integrate deeply with CI, and usually stop short of applying and validating fixes.
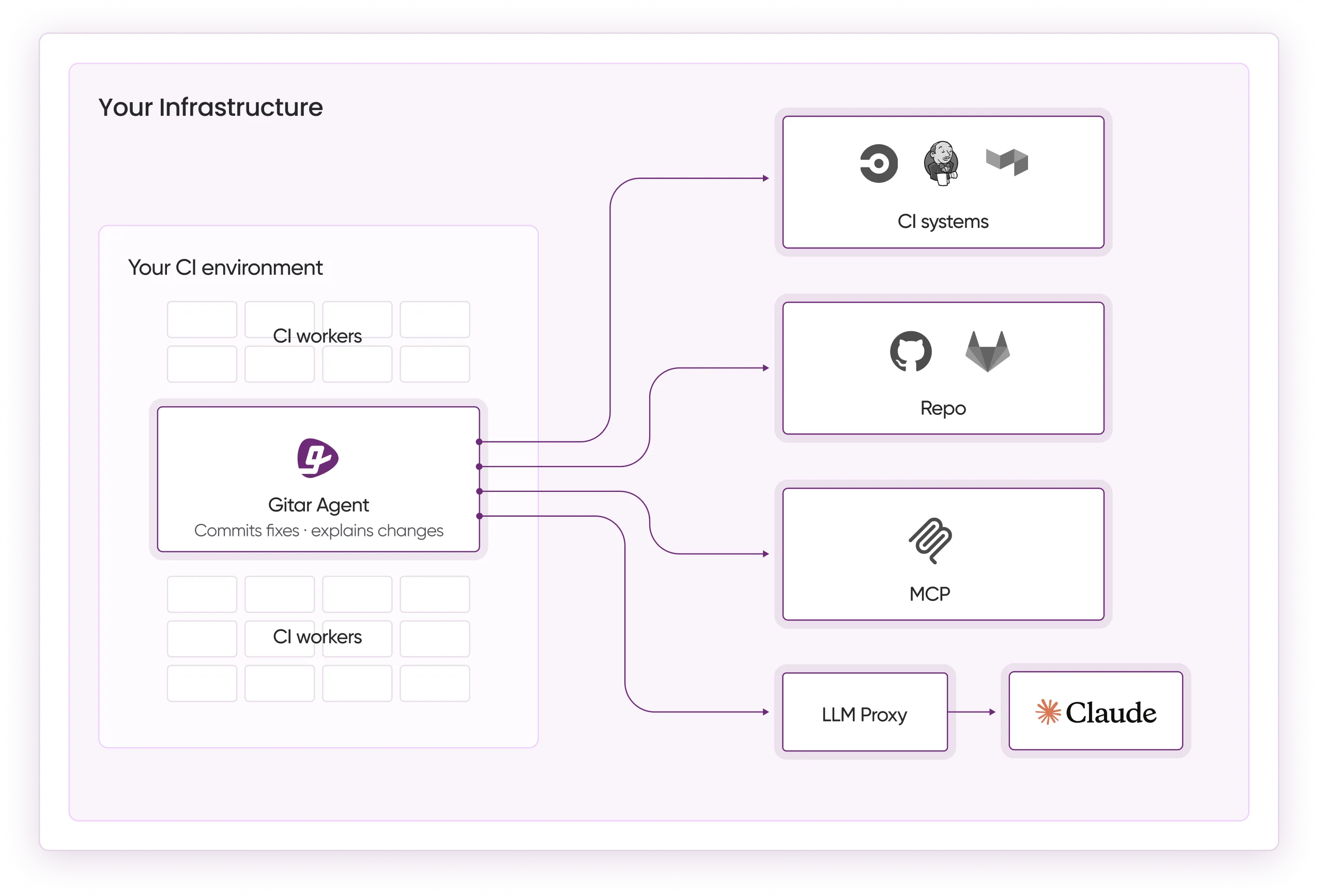
Gitar integrates with GitHub and GitLab for version control, GitHub Actions, GitLab CI, CircleCI, and Buildkite for CI, and Slack, Jira, and Linear for collaboration. Teams can adopt autonomous remediation without replacing their existing stack.
Configurable automation levels let teams begin with suggestion-only mode, then move to auto-commit for specific failure types. This staged rollout reduces risk and builds confidence while still delivering early value.
How Gitar Technically Stabilizes Flaky Tests
Gitar targets common CI failure patterns, including flaky tests, with specific fix strategies. For race conditions, the platform adds explicit waits and retry logic. Root causes include pending AJAX or Fetch calls, active animations, stale DOM elements, and racing assertions.
A typical JavaScript race condition fix might change this snippet:
// Flaky: Assertion before async resolve expect(element.textContent).toBe(‘Updated’);
Into this version:
// Fixed: Explicit wait for state await waitFor(() => expect(element.textContent).toBe(‘Updated’));
For async issues, Gitar replaces hardcoded delays with waits that track real application readiness. The engine uses full-project context, including related components and dependencies, when it proposes changes.
Gitar’s natural language rules system lets teams encode remediation patterns such as:
— title: “Async Test Stabilization” when: “Test failures contain ‘timeout’ or ‘race condition'” actions: “Add explicit waits and retry logic” —
Case studies report high autofix rates for recurring CI failures, including security bugs and infrastructure-sensitive issues.
Four-Phase Rollout Plan for Gitar
Phase 1: Installation (30 seconds)
Teams install the Gitar GitHub App or GitLab integration without creating an account or entering a credit card. Gitar immediately posts dashboard comments on new PRs and delivers free code review plus CI analysis.
Phase 2: Trust Building
Teams begin in suggestion mode, where Gitar proposes fixes for review. The platform handles lint errors, test failures, and build breaks while keeping feedback inside a single comment thread. This phase lets teams assess fix quality before enabling automation.
Phase 3: Enable Autofix
Teams then enable automatic commits for trusted fix categories based on observed success. Automation levels can vary by repository or failure type, which preserves control while shrinking manual toil. Most teams see quick productivity gains as routine issues resolve without human effort.
Phase 4: Analytics and Enterprise Features
Teams use the analytics dashboard to spot CI patterns, define natural language rules for custom workflows, and connect enterprise integrations. Security-focused organizations can deploy Gitar agents inside their own CI infrastructure with full access to configs and secrets.
Common Implementation Pitfalls
- Relying on quarantine instead of fixing flaky tests at the source.
- Paying for tools that only suggest fixes and never apply them.
- Ignoring cross-platform needs in mixed CI and VCS environments.
- Skipping a gradual rollout and enabling aggressive automation too early.
Frequently Asked Questions
How Gitar Fixes Flaky Tests in GitHub Actions
Gitar connects directly to GitHub Actions workflows and watches CI runs in real time. When a flaky test appears, Gitar inspects the logs, identifies issues such as race conditions or timing gaps, and generates a fix using full repository context. It then validates the change in the same CI environment and commits the working solution to the PR. This workflow also applies to GitLab CI, CircleCI, and Buildkite.
How Gitar Compares to BuildPulse and Datadog CI Visibility
BuildPulse and Datadog focus on detection and quarantine, while Gitar focuses on healing. BuildPulse isolates flaky tests to reduce noise, and Datadog surfaces CI performance insights, yet both still require engineers to craft and apply fixes. Gitar generates, validates, and commits code changes automatically. Gitar also offers free, unlimited code review for all repositories and users, while many competitors charge $15–30 per developer for suggestion-only features.
Cost of Autonomous CI Remediation vs Other Platforms
Gitar provides free, unlimited code review and a 14-day free trial of autofix features. Competing tools such as CodeRabbit at $15 per developer and Greptile at $30 per developer charge monthly for suggestions that still need manual work. A 30-person team can pay $450–900 each month for less capability than Gitar’s free tier. Teams often save around $750,000 per year in productivity while paying nothing for Gitar’s core platform.
Support for CircleCI and Enterprise CI Environments
Gitar supports GitHub Actions, GitLab CI, CircleCI, and Buildkite out of the box. The platform emulates full environments, including SDK versions, multi-dependency builds, and third-party security scans. Enterprises can deploy agents inside their own CI infrastructure with access to private configs, secrets, and caches. Gitar already operates at enterprise scale and maintains SOC 2 Type II and ISO 27001 certifications.
How Teams Stay in Control of Automated Commits
Gitar lets teams tune automation levels to match their risk tolerance. Many teams start in suggestion mode and require manual approval for every change. After they gain confidence, they enable auto-commit for safe categories such as lint fixes or simple race condition patches. Detailed explanations accompany each fix, including analysis steps and validation results, and teams can revert to suggestion-only mode at any time.
Conclusion: Move from Detection to Autonomous Green Builds
AI coding has accelerated code creation and exposed CI as the new bottleneck. Flaky tests now represent a major source of delay, context switching, and lost trust in automation, often costing teams more than $1 million per year.
Quarantining flaky tests or relying on reruns hides problems and still charges teams for manual cleanup. The industry now needs platforms that analyze root causes, ship validated fixes, and keep builds green through real remediation.
Gitar delivers that model with a free AI healing engine, comprehensive code review, autonomous fix generation, and broad CI support without per-seat pricing.